TECHNICAL ASSET FINGERPRINT
5b04740f3e2192f02c1a2341
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
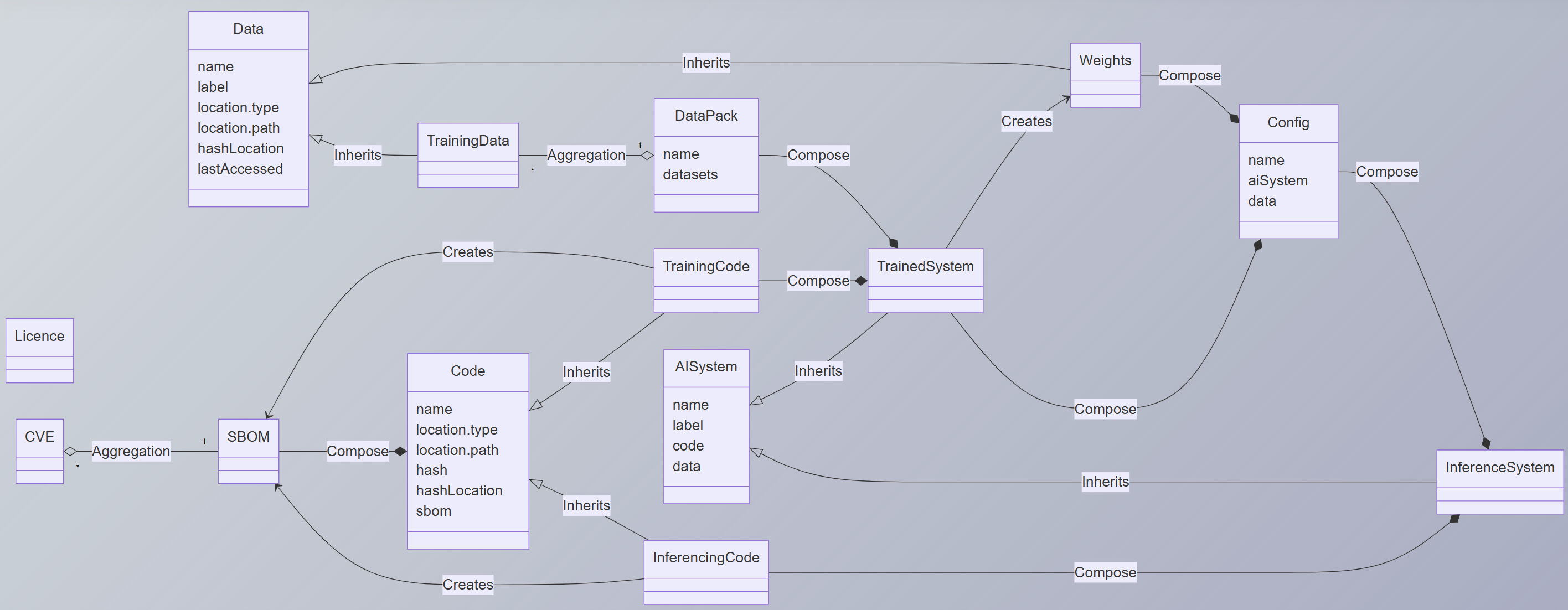
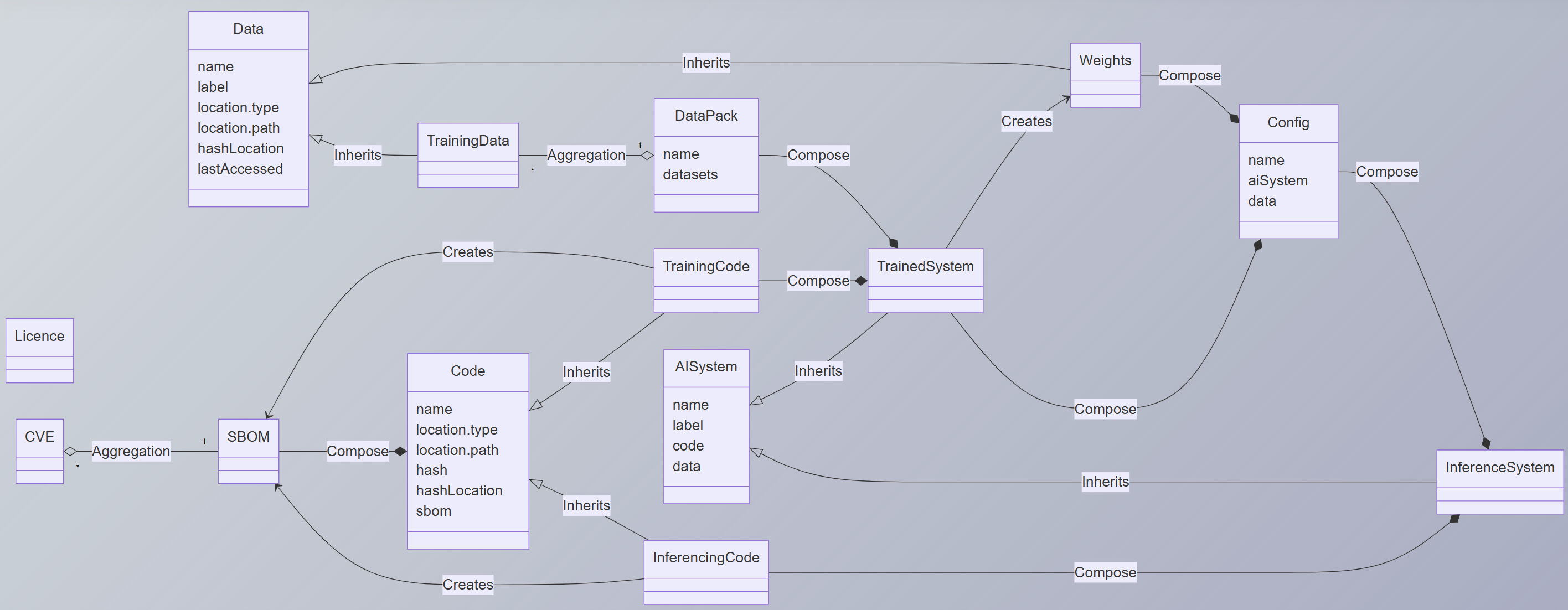
## Diagram: AI System Architecture
### Overview
The image is a diagram illustrating the architecture of an AI system, showing the relationships between various components such as data, code, models, and configurations. The diagram uses UML-like notation to represent classes and their relationships (inheritance, composition, aggregation).
### Components/Axes
The diagram consists of several rectangular boxes representing different components of the AI system. Each box is divided into two sections: the top section contains the name of the component, and the bottom section lists attributes or properties associated with that component. The relationships between components are indicated by arrows labeled with the type of relationship (e.g., "Inherits", "Compose", "Aggregation", "Creates").
The components are:
* **Data**: Attributes include name, label, location.type, location.path, hashLocation, lastAccessed. Located at the top-left of the diagram.
* **TrainingData**: No attributes listed. Located below and to the right of "Data".
* **DataPack**: Attributes include name, datasets. Located to the right of "TrainingData".
* **TrainingCode**: No attributes listed. Located below "DataPack".
* **TrainedSystem**: No attributes listed. Located to the right of "TrainingCode".
* **Weights**: No attributes listed. Located at the top-right of the diagram.
* **Config**: Attributes include name, aiSystem, data. Located below "Weights".
* **InferenceSystem**: No attributes listed. Located at the bottom-right of the diagram.
* **Code**: Attributes include name, location.type, location.path, hash, hashLocation, sbom. Located in the bottom-left quadrant of the diagram.
* **AISystem**: Attributes include name, label, code, data. Located to the right and slightly above "Code".
* **InferencingCode**: No attributes listed. Located below "AISystem".
* **Licence**: No attributes listed. Located at the bottom-left of the diagram.
* **CVE**: No attributes listed. Located to the left of "SBOM".
* **SBOM**: No attributes listed. Located to the right of "CVE".
The relationships are:
* **Inherits**: Data inherits from TrainingData, Code inherits from AISystem, Code inherits from InferencingCode, AISystem inherits from TrainedSystem, Config inherits from InferenceSystem.
* **Aggregation**: TrainingData aggregates DataPack, CVE aggregates SBOM. The multiplicity is indicated as "*" for TrainingData and CVE, and "1" for DataPack and SBOM.
* **Compose**: DataPack composes TrainedSystem, TrainingCode composes TrainedSystem, Weights composes Config, Config composes InferenceSystem, SBOM composes TrainedSystem, AISystem composes TrainedSystem, InferencingCode composes InferenceSystem.
* **Creates**: TrainingData creates TrainingCode, Weights creates Config, Code creates InferencingCode.
### Detailed Analysis or ### Content Details
* **Data** inherits into **TrainingData**.
* **TrainingData** has an aggregation relationship with **DataPack** (many to one).
* **DataPack** composes into **TrainedSystem**.
* **DataPack** also composes into **TrainingCode**.
* **TrainingCode** composes into **TrainedSystem**.
* **Weights** composes into **Config**.
* **Config** composes into **InferenceSystem**.
* **Code** inherits into **AISystem**.
* **AISystem** inherits into **TrainedSystem**.
* **AISystem** has attributes name, label, code, and data.
* **Code** has attributes name, location.type, location.path, hash, hashLocation, and sbom.
* **Code** creates **InferencingCode**.
* **InferencingCode** composes into **InferenceSystem**.
* **Config** has attributes name, aiSystem, and data.
* **CVE** has an aggregation relationship with **SBOM** (many to one).
* **SBOM** composes into **TrainedSystem**.
### Key Observations
* The diagram illustrates a hierarchical structure with inheritance and composition relationships.
* The "TrainedSystem" component appears to be a central hub, composed of multiple other components.
* Data and code are separated into distinct components, with clear relationships defined.
* The diagram includes security-related components like "CVE" and "SBOM", suggesting a focus on security considerations.
### Interpretation
The diagram provides a high-level overview of the architecture of an AI system, emphasizing the relationships between different components. It highlights the flow of data and code through the system, from initial data collection and training to inference and deployment. The use of inheritance and composition suggests a modular and reusable design. The inclusion of security-related components indicates a focus on addressing potential vulnerabilities and ensuring the integrity of the system. The diagram suggests that the TrainedSystem is the core component, integrating data, code, and configurations to perform its intended function.
DECODING INTELLIGENCE...
EXPERT: gemma-3-27b-it-free VERSION 1
RUNTIME: google-free/gemma-3-27b-it
INTEL_VERIFIED
\n
## Diagram: System Component Relationships
### Overview
This diagram depicts the relationships between various components in a system, likely related to machine learning or AI model development and deployment. It uses a UML-like class diagram notation to show inheritance, composition, aggregation, and creation relationships between entities like Data, Code, TrainingData, and InferenceSystem. The diagram is oriented with the primary data flow appearing to move from the top to the bottom.
### Components/Axes
The diagram consists of rectangular boxes representing components, connected by arrows indicating relationships. The arrowheads denote the type of relationship:
* **Inherits:** A solid arrow with a hollow arrowhead.
* **Creates:** A dashed arrow with a hollow arrowhead.
* **Compose:** A solid arrow with a filled arrowhead.
* **Aggregation:** A hollow arrow with a hollow arrowhead.
The components and their attributes are:
* **Data:** Attributes: name, label, location.type, location.path, hashLocation, lastAccessed.
* **TrainingData:** Inherits from Data.
* **DataPack:** Attributes: name, datasets.
* **TrainingCode:**
* **TrainedSystem:**
* **Weights:**
* **Config:** Attributes: name, aiSystem, data.
* **Code:** Attributes: name, location.type, location.path, hash, hashLocation, sbom.
* **AISystem:** Attributes: name, label, code, data. Inherits from Code.
* **InferenceSystem:**
* **InferencingCode:**
* **Licence:**
* **CVE:**
* **SBOM:**
### Detailed Analysis or Content Details
The diagram shows the following relationships:
* **Data** inherits to **TrainingData**.
* **DataPack** is composed of **TrainingCode** and **TrainedSystem**.
* **DataPack** aggregates **Datasets**.
* **TrainingData** creates **DataPack**.
* **Weights** composes **Config**.
* **Config** composes **aiSystem** and **data**.
* **Code** inherits to **AISystem**.
* **AISystem** inherits to **InferenceSystem**.
* **Code** attributes: name, location.type, location.path, hash, hashLocation, sbom.
* **AISystem** attributes: name, label, code, data.
* **InferencingCode** creates **InferenceSystem**.
* **Licence** aggregates **CVE** and **SBOM**.
* **Code** composes **SBOM**.
### Key Observations
The diagram highlights a clear separation between training and inference phases. Training involves Data, TrainingData, DataPack, TrainingCode, and TrainedSystem. Inference involves AISystem, InferenceSystem, and InferencingCode. The inclusion of Licence, CVE, and SBOM suggests a focus on security and compliance. The composition of Config by Weights indicates that model weights are a key part of the configuration.
### Interpretation
The diagram represents a system architecture for developing and deploying AI models. The flow suggests that raw Data is transformed into TrainingData, which is then used to create a DataPack. This DataPack, along with TrainingCode, produces a TrainedSystem. During inference, the TrainedSystem, along with InferencingCode, forms an InferenceSystem. The inclusion of Code, SBOM, CVE, and Licence indicates a strong emphasis on software bill of materials, vulnerability management, and licensing compliance. The diagram suggests a modular design, where components are clearly defined and interconnected through well-defined relationships. The use of inheritance promotes code reuse and maintainability. The overall architecture appears to be designed for scalability and security, with a clear separation of concerns between training and inference.
DECODING INTELLIGENCE...
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
## UML Class Diagram: AI System Lifecycle and Components
### Overview
This image is a Unified Modeling Language (UML) class diagram illustrating the structural relationships and data flow between components involved in the lifecycle of an Artificial Intelligence (AI) system. It models entities from raw data and code, through training, to a deployed inference system, including aspects of security and licensing.
### Components/Classes
The diagram consists of 14 distinct classes (represented as boxes) connected by labeled relationship arrows. Each class contains a list of its attributes.
**Classes and their Attributes:**
1. **Data** (Top-left)
* `name`
* `label`
* `location.type`
* `location.path`
* `hashLocation`
* `lastAccessed`
2. **TrainingData** (Below Data)
* (No attributes listed in the visible compartment)
3. **DataPack** (Center-top)
* `name`
* `datasets`
4. **Weights** (Top-right)
* (No attributes listed in the visible compartment)
5. **Config** (Right of Weights)
* `name`
* `aiSystem`
* `data`
6. **TrainingCode** (Center)
* (No attributes listed in the visible compartment)
7. **TrainedSystem** (Center-right)
* (No attributes listed in the visible compartment)
8. **AISystem** (Below TrainedSystem)
* `name`
* `label`
* `code`
* `data`
9. **InferenceSystem** (Bottom-right)
* (No attributes listed in the visible compartment)
10. **Code** (Center-left)
* `name`
* `location.type`
* `location.path`
* `hash`
* `hashLocation`
* `sbom`
11. **InferencingCode** (Below Code)
* (No attributes listed in the visible compartment)
12. **SBOM** (Left, connected to Code)
* (No attributes listed in the visible compartment)
13. **Licence** (Far left, isolated)
* (No attributes listed in the visible compartment)
14. **CVE** (Far left, below Licence)
* (No attributes listed in the visible compartment)
### Detailed Analysis: Relationships and Flow
The classes are interconnected through four primary types of relationships, indicated by arrow styles and labels:
1. **Inheritance (Generalization):** Represented by a solid line with a hollow, triangular arrowhead pointing to the parent class.
* `TrainingData` **Inherits** from `Data`.
* `AISystem` **Inherits** from `TrainedSystem`.
* `InferenceSystem` **Inherits** from `AISystem`.
* `Code` **Inherits** from `InferencingCode` (Note: The arrow direction suggests `InferencingCode` is a subclass of `Code`).
2. **Aggregation:** Represented by a solid line with a hollow diamond at the container end.
* `DataPack` has an **Aggregation** relationship with `TrainingData`. The multiplicity is `1` DataPack to `*` (many) TrainingData items.
* `SBOM` has an **Aggregation** relationship with `CVE`. The multiplicity is `1` SBOM to `*` (many) CVEs.
3. **Composition:** Represented by a solid line with a filled diamond at the container end. This implies a strong "owns" relationship.
* `DataPack` **Composes** `TrainedSystem`.
* `TrainingCode` **Composes** `TrainedSystem`.
* `Weights` **Composes** `Config`.
* `Config` **Composes** `InferenceSystem`.
* `AISystem` **Composes** `InferenceSystem`.
* `Code` **Composes** `SBOM`.
* `InferencingCode` **Composes** `InferenceSystem`.
4. **Creation Dependency:** Represented by a dashed line with an open arrowhead and the label "Creates".
* `TrainingCode` **Creates** `SBOM`.
* `InferencingCode` **Creates** `SBOM`.
### Key Observations
* **Central Hub:** The `TrainedSystem` class acts as a central hub, composed by both `DataPack` (data) and `TrainingCode` (code), and is the parent of the `AISystem`.
* **Lifecycle Flow:** The diagram suggests a clear pipeline: `Data` -> `TrainingData` -> `DataPack` -> `TrainedSystem`. Parallel to this, `Code` -> `TrainingCode` -> `TrainedSystem`. The `TrainedSystem` then evolves into an `AISystem` and finally an `InferenceSystem` for deployment.
* **Security & Compliance Integration:** The inclusion of `SBOM` (Software Bill of Materials) and `CVE` (Common Vulnerabilities and Exposures) as components created by code and aggregating security vulnerabilities highlights a focus on supply chain security and vulnerability management.
* **Configuration Separation:** The `Config` class, which composes `Weights` and is itself composed by the `InferenceSystem`, separates model configuration and parameters from the core system logic.
* **Isolated Element:** The `Licence` class is present but has no connecting relationships in this view, suggesting it may be a metadata element not directly tied to the operational flow depicted.
### Interpretation
This diagram provides a structural blueprint for an AI system's asset management and lifecycle. It emphasizes **modularity** and **traceability**.
* **What it demonstrates:** It models how an AI system is not a monolithic entity but an assembly of distinct, traceable components: data assets (`Data`, `TrainingData`), code artifacts (`Code`, `TrainingCode`), and the resulting trained models (`TrainedSystem`, `Weights`). The relationships show provenance—what creates or owns what.
* **How elements relate:** The flow moves from raw ingredients (Data, Code) through a training process (involving DataPack and TrainingCode) to produce a trained asset (TrainedSystem). This asset is then specialized (AISystem) and packaged with configuration (Config) for deployment (InferenceSystem). The parallel creation of an SBOM by the code components integrates security auditing directly into the development lifecycle.
* **Notable Implications:** The model prioritizes **reproducibility** (via hashing attributes in `Data` and `Code`) and **security** (via SBOM/CVE aggregation). The inheritance hierarchy (`TrainedSystem` -> `AISystem` -> `InferenceSystem`) suggests a progressive specialization of the system for different purposes, from a general trained model to a deployable service. The absence of a link to `Licence` might indicate a gap in modeling legal compliance within this specific diagram view.
DECODING INTELLIGENCE...
EXPERT: nemotron-free VERSION 1
RUNTIME: free/nvidia/nemotron-nano-12b-v2-vl:free
INTEL_VERIFIED
## UML Class Diagram: AI System Architecture
### Overview
This UML class diagram illustrates the architecture of an AI system, detailing components, relationships, and data flows. It includes classes for data management, training, configuration, and inference, with explicit inheritance and composition relationships.
### Components/Axes
#### Classes and Attributes
1. **Data**
- Attributes: `name`, `label`, `location.type`, `location.path`, `hashLocation`, `lastAccessed`
2. **TrainingData** (inherits from Data)
- No additional attributes shown
3. **DataPack**
- Attributes: `name`, `datasets` (aggregation)
4. **Weights**
- No attributes shown
5. **Config**
- Attributes: `name`, `aiSystem`, `data`
6. **TrainedSystem**
- Attributes: `name`, `code`, `data`, `weights`
7. **AI System**
- Attributes: `name`, `label`, `code`, `data`
8. **InferenceSystem**
- Attributes: `name`, `code`, `trainedSystem`
9. **Code**
- Attributes: `name`, `location.type`, `location.path`, `hash`, `hashLocation`, `sbom`
10. **TrainingCode** (inherits from Code)
- No additional attributes shown
11. **InferencingCode** (inherits from Code)
- No additional attributes shown
12. **SBOM** (aggregated by CVE)
- No attributes shown
13. **CVE**
- No attributes shown
14. **Licence**
- No attributes shown
#### Relationships
- **Inherits**:
- `TrainingData` ← `Data`
- `TrainingCode` ← `Code`
- `InferencingCode` ← `Code`
- `AI System` ← `Data`
- `TrainedSystem` ← `AI System`
- `InferenceSystem` ← `AI System`
- **Aggregation**:
- `DataPack` ← `TrainingData`
- `CVE` ← `SBOM`
- **Composition**:
- `TrainedSystem` ← `TrainingCode` + `Weights`
- `InferenceSystem` ← `InferencingCode` + `TrainedSystem`
- `Config` ← `AI System` + `Data`
- **Creates**:
- `TrainingCode` → `TrainedSystem`
- `Weights` → `TrainedSystem`
- `Config` → `TrainedSystem`
### Detailed Analysis
#### Data Flow
1. **Data** serves as the foundational class, with attributes for metadata (name, label, location, hashes, access timestamps).
2. **TrainingData** inherits from Data, representing preprocessed training datasets.
3. **DataPack** aggregates TrainingData, organizing datasets under a name.
4. **TrainingCode** (inheriting from Code) creates a **TrainedSystem** when combined with **Weights**.
5. **TrainedSystem** composes:
- TrainingCode (source code)
- Weights (model parameters)
- Config (system configuration linking AI System and Data)
6. **AI System** inherits Data and composes Config, representing the operational AI environment.
7. **InferenceSystem** inherits AI System and composes:
- InferencingCode (code for inference tasks)
- TrainedSystem (pre-trained model)
#### Spatial Grounding
- **Top-Left**: Data, TrainingData, DataPack, Weights, Config
- **Center**: TrainingCode, TrainedSystem, AI System
- **Bottom**: Code, SBOM, CVE, Licence
- **Right**: InferenceSystem, InferencingCode
### Key Observations
1. **Modular Design**: The system separates data, training, and inference components, promoting reusability.
2. **Security Focus**: SBOM (Software Bill of Materials) and CVE (Common Vulnerabilities and Exposures) indicate emphasis on security and transparency.
3. **Configuration Dependency**: Config acts as a bridge between AI System and Data, ensuring compatibility.
4. **Inheritance Hierarchy**: Code serves as a base class for TrainingCode and InferencingCode, reducing redundancy.
### Interpretation
This architecture demonstrates a layered approach to AI system development:
- **Data Layer**: Manages raw data and metadata, critical for reproducibility.
- **Training Layer**: Converts raw data into TrainingData, trains models (TrainedSystem), and packages weights.
- **Inference Layer**: Uses TrainedSystem and custom InferencingCode for real-time predictions.
- **Security/Compliance**: SBOM and CVE integration ensures traceability and vulnerability management.
The diagram emphasizes **composition over inheritance** for flexibility, with Config acting as a critical integration point. The absence of numerical values suggests this is a conceptual model rather than a performance benchmark. The use of SBOM highlights modern practices in software supply chain security.
DECODING INTELLIGENCE...