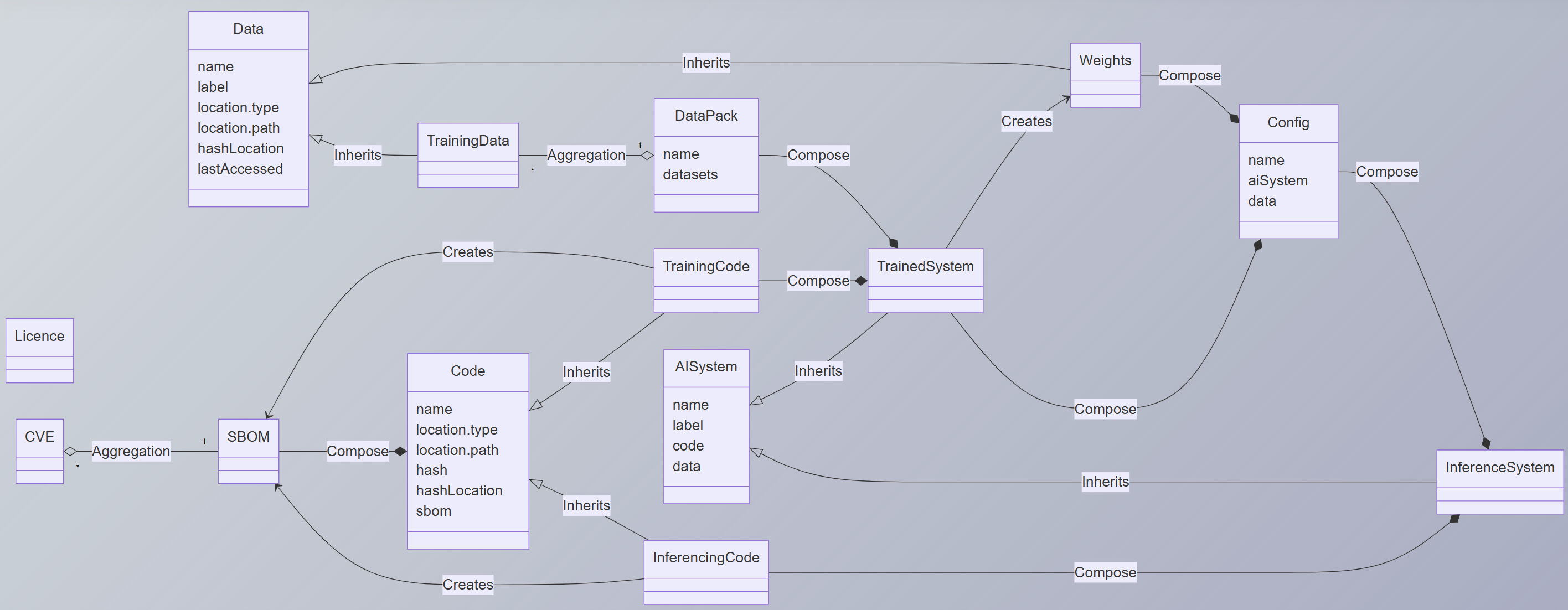
## UML Class Diagram: AI System Architecture
### Overview
This UML class diagram illustrates the architecture of an AI system, detailing components, relationships, and data flows. It includes classes for data management, training, configuration, and inference, with explicit inheritance and composition relationships.
### Components/Axes
#### Classes and Attributes
1. **Data**
- Attributes: `name`, `label`, `location.type`, `location.path`, `hashLocation`, `lastAccessed`
2. **TrainingData** (inherits from Data)
- No additional attributes shown
3. **DataPack**
- Attributes: `name`, `datasets` (aggregation)
4. **Weights**
- No attributes shown
5. **Config**
- Attributes: `name`, `aiSystem`, `data`
6. **TrainedSystem**
- Attributes: `name`, `code`, `data`, `weights`
7. **AI System**
- Attributes: `name`, `label`, `code`, `data`
8. **InferenceSystem**
- Attributes: `name`, `code`, `trainedSystem`
9. **Code**
- Attributes: `name`, `location.type`, `location.path`, `hash`, `hashLocation`, `sbom`
10. **TrainingCode** (inherits from Code)
- No additional attributes shown
11. **InferencingCode** (inherits from Code)
- No additional attributes shown
12. **SBOM** (aggregated by CVE)
- No attributes shown
13. **CVE**
- No attributes shown
14. **Licence**
- No attributes shown
#### Relationships
- **Inherits**:
- `TrainingData` ← `Data`
- `TrainingCode` ← `Code`
- `InferencingCode` ← `Code`
- `AI System` ← `Data`
- `TrainedSystem` ← `AI System`
- `InferenceSystem` ← `AI System`
- **Aggregation**:
- `DataPack` ← `TrainingData`
- `CVE` ← `SBOM`
- **Composition**:
- `TrainedSystem` ← `TrainingCode` + `Weights`
- `InferenceSystem` ← `InferencingCode` + `TrainedSystem`
- `Config` ← `AI System` + `Data`
- **Creates**:
- `TrainingCode` → `TrainedSystem`
- `Weights` → `TrainedSystem`
- `Config` → `TrainedSystem`
### Detailed Analysis
#### Data Flow
1. **Data** serves as the foundational class, with attributes for metadata (name, label, location, hashes, access timestamps).
2. **TrainingData** inherits from Data, representing preprocessed training datasets.
3. **DataPack** aggregates TrainingData, organizing datasets under a name.
4. **TrainingCode** (inheriting from Code) creates a **TrainedSystem** when combined with **Weights**.
5. **TrainedSystem** composes:
- TrainingCode (source code)
- Weights (model parameters)
- Config (system configuration linking AI System and Data)
6. **AI System** inherits Data and composes Config, representing the operational AI environment.
7. **InferenceSystem** inherits AI System and composes:
- InferencingCode (code for inference tasks)
- TrainedSystem (pre-trained model)
#### Spatial Grounding
- **Top-Left**: Data, TrainingData, DataPack, Weights, Config
- **Center**: TrainingCode, TrainedSystem, AI System
- **Bottom**: Code, SBOM, CVE, Licence
- **Right**: InferenceSystem, InferencingCode
### Key Observations
1. **Modular Design**: The system separates data, training, and inference components, promoting reusability.
2. **Security Focus**: SBOM (Software Bill of Materials) and CVE (Common Vulnerabilities and Exposures) indicate emphasis on security and transparency.
3. **Configuration Dependency**: Config acts as a bridge between AI System and Data, ensuring compatibility.
4. **Inheritance Hierarchy**: Code serves as a base class for TrainingCode and InferencingCode, reducing redundancy.
### Interpretation
This architecture demonstrates a layered approach to AI system development:
- **Data Layer**: Manages raw data and metadata, critical for reproducibility.
- **Training Layer**: Converts raw data into TrainingData, trains models (TrainedSystem), and packages weights.
- **Inference Layer**: Uses TrainedSystem and custom InferencingCode for real-time predictions.
- **Security/Compliance**: SBOM and CVE integration ensures traceability and vulnerability management.
The diagram emphasizes **composition over inheritance** for flexibility, with Config acting as a critical integration point. The absence of numerical values suggests this is a conceptual model rather than a performance benchmark. The use of SBOM highlights modern practices in software supply chain security.