## Hierarchy Diagram: Hardware Defenses of Speculative Execution Attacks
### Overview
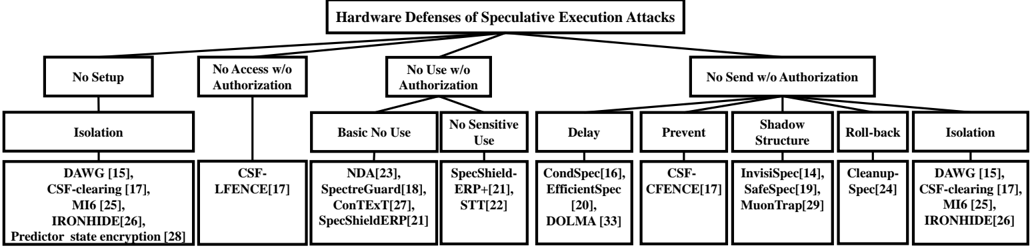
The image is a hierarchy diagram illustrating different hardware defenses against speculative execution attacks. The diagram branches out from a central title into four main categories, which are further subdivided into specific defense mechanisms. Each defense mechanism is listed with associated citations in square brackets.
### Components/Axes
* **Title:** Hardware Defenses of Speculative Execution Attacks
* **First Level Categories:**
* No Setup
* No Access w/o Authorization
* No Use w/o Authorization
* No Send w/o Authorization
* **Second Level Categories (under "No Use w/o Authorization"):**
* Basic No Use
* No Sensitive Use
* Delay
* Prevent
* Shadow Structure
* Roll-back
* Isolation
* **Defense Mechanisms (listed under each category):**
* Isolation (under "No Setup"): DAWG [15], CSF-clearing [17], MI6 [25], IRONHIDE [26], Predictor state encryption [28]
* CSF-LFENCE [17] (under "No Access w/o Authorization")
* Basic No Use (under "No Use w/o Authorization"): NDA [23], SpectreGuard [18], ConTEXT [27], SpecShieldERP [21]
* No Sensitive Use (under "No Use w/o Authorization"): SpecShield-ERP+ [21], STT [22]
* Delay (under "No Use w/o Authorization"): CondSpec [16], EfficientSpec [20], DOLMA [33]
* Prevent (under "No Send w/o Authorization"): CSF-CFENCE [17]
* Shadow Structure (under "No Send w/o Authorization"): InvisiSpec [14], SafeSpec [19], MuonTrap [29]
* Roll-back (under "No Send w/o Authorization"): Cleanup-Spec [24]
* Isolation (under "No Send w/o Authorization"): DAWG [15], CSF-clearing [17], MI6 [25], IRONHIDE [26]
### Detailed Analysis or ### Content Details
The diagram is structured as a tree, with the main title at the top and the categories branching downwards. Each category is represented by a rectangular box, and the connections between the boxes indicate the hierarchical relationships. The defense mechanisms are listed below their respective categories, each followed by a citation in square brackets.
* **No Setup:** This category includes defenses that do not require any initial setup. The listed mechanisms are Isolation, DAWG [15], CSF-clearing [17], MI6 [25], IRONHIDE [26], and Predictor state encryption [28].
* **No Access w/o Authorization:** This category includes defenses that prevent access without authorization. The listed mechanism is CSF-LFENCE [17].
* **No Use w/o Authorization:** This category includes defenses that prevent use without authorization. It is further divided into Basic No Use and No Sensitive Use.
* **Basic No Use:** NDA [23], SpectreGuard [18], ConTEXT [27], SpecShieldERP [21]
* **No Sensitive Use:** SpecShield-ERP+ [21], STT [22]
* **Delay:** CondSpec [16], EfficientSpec [20], DOLMA [33]
* **No Send w/o Authorization:** This category includes defenses that prevent sending data without authorization.
* **Prevent:** CSF-CFENCE [17]
* **Shadow Structure:** InvisiSpec [14], SafeSpec [19], MuonTrap [29]
* **Roll-back:** Cleanup-Spec [24]
* **Isolation:** DAWG [15], CSF-clearing [17], MI6 [25], IRONHIDE [26]
### Key Observations
* The "Isolation" defense mechanism appears under both "No Setup" and "No Send w/o Authorization" categories, suggesting it can be implemented in different ways.
* The citations in square brackets likely refer to research papers or publications that describe the respective defense mechanisms.
* The diagram provides a structured overview of different approaches to hardware-based defenses against speculative execution attacks.
### Interpretation
The diagram provides a taxonomy of hardware defenses against speculative execution attacks. It categorizes these defenses based on their operational principles, such as preventing unauthorized access, use, or data transmission. The inclusion of specific defense mechanisms with citations allows for further research and understanding of each approach. The hierarchical structure helps to organize and classify the various defenses, making it easier to compare and contrast their strengths and weaknesses. The repetition of "Isolation" under different categories suggests that this defense strategy can be applied in multiple contexts.