\n
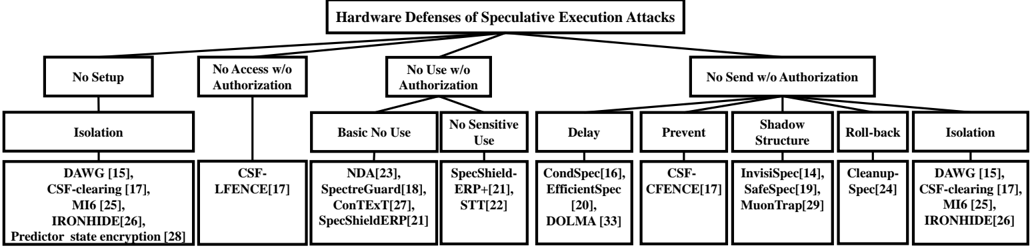
## Diagram: Hardware Defenses of Speculative Execution Attacks
### Overview
The image is a hierarchical diagram illustrating various hardware defenses against speculative execution attacks. The diagram is structured as a tree, branching out from a central title into several categories and subcategories of defenses. The diagram uses boxes to represent categories and lists specific defense mechanisms within each category.
### Components/Axes
The diagram is organized into the following levels:
* **Top Level:** "Hardware Defenses of Speculative Execution Attacks" - This is the main title, positioned at the top center.
* **Level 2:** Four main categories branching from the top level:
* "No Setup"
* "No Access w/o Authorization"
* "No Use w/o Authorization"
* "No Send w/o Authorization"
* **Level 3:** Subcategories branching from Level 2:
* Under "No Setup": "Isolation"
* Under "No Access w/o Authorization": "Basic No Use"
* Under "No Use w/o Authorization": "No Sensitive Use", "Delay", "Prevent"
* Under "No Send w/o Authorization": "Shadow Structure", "Roll-back", "Isolation"
* **Level 4:** Specific defense mechanisms listed under each Level 3 subcategory. These are enclosed in brackets with numerical references.
### Detailed Analysis or Content Details
**No Setup -> Isolation:**
* DAWG [15], CSF-clearing [17], M16 [25], IRONHIDE[26]
* Predictor state encryption [28]
**No Access w/o Authorization -> Basic No Use:**
* NDA[23], SpectreGuard[18], ConTEX[72], SpecShieldERP[21]
**No Use w/o Authorization -> No Sensitive Use:**
* SpecShield [21], ERP[21], STT[22]
**No Use w/o Authorization -> Delay:**
* CondSpec[16], EfficientSpec [20], DOLMA [33]
**No Use w/o Authorization -> Prevent:**
* CSF-CFENCE[17]
**No Send w/o Authorization -> Shadow Structure:**
* InvisiShield[14], SafeGuard[19], MuonTrap[29]
**No Send w/o Authorization -> Roll-back:**
* Cleanup-Spec[24]
**No Send w/o Authorization -> Isolation:**
* DAWG [15], CSF-clearing [17], M16 [25], IRONHIDE[26]
### Key Observations
* "Isolation" appears as a defense strategy under both "No Setup" and "No Send w/o Authorization", suggesting it's a fundamental approach.
* Several defense mechanisms are referenced with numerical annotations (e.g., [15], [17]), likely indicating citations or references to research papers.
* The diagram presents a comprehensive overview of hardware-based defenses, categorizing them based on the attack vector they address.
* The diagram is symmetrical in its branching structure, except for the "No Setup" branch which only has one subcategory.
### Interpretation
The diagram illustrates a layered approach to defending against speculative execution attacks. The top-level categories represent different phases or aspects of the attack that need to be mitigated. The subcategories and specific mechanisms then provide increasingly granular defenses. The repetition of "Isolation" suggests its importance as a core security principle. The numerical references indicate that these defenses are based on established research and development efforts. The diagram is a valuable resource for understanding the landscape of hardware defenses against these attacks, and how different approaches can be combined to provide a more robust security posture. The diagram suggests a focus on preventing unauthorized access, use, and sending of sensitive data during speculative execution.