\n
## Diagram: Hardware Defenses of Speculative Execution Attacks
### Overview
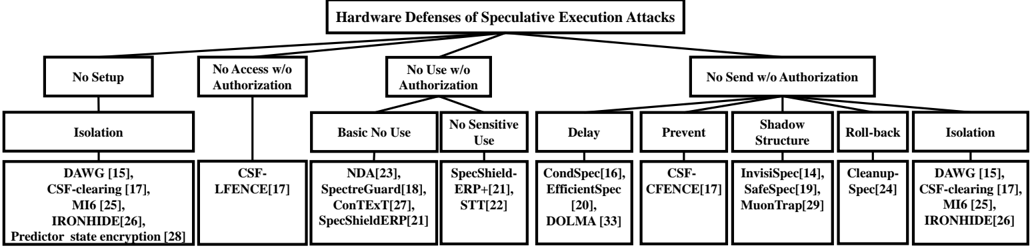
This image is a hierarchical taxonomy diagram illustrating various hardware-based defense mechanisms against speculative execution attacks. The diagram is structured as a tree, with the main title at the top and categories branching downward into more specific defense strategies and their associated implementations or research papers.
### Components/Axes
The diagram is organized into a multi-level hierarchy. The primary structure is as follows:
* **Top-Level Title (Center):** "Hardware Defenses of Speculative Execution Attacks"
* **First-Level Categories (Four main branches, from left to right):**
1. No Setup
2. No Access w/o Authorization
3. No Use w/o Authorization
4. No Send w/o Authorization
* **Second-Level Categories (Sub-branches under the first-level categories):**
* Under "No Setup": **Isolation**
* Under "No Access w/o Authorization": (Directly lists a defense)
* Under "No Use w/o Authorization": **Basic No Use**, **No Sensitive Use**, **Delay**, **Prevent**, **Shadow Structure**, **Roll-back**
* Under "No Send w/o Authorization": **Isolation**
* **Third-Level Items (Specific defenses and citations):** These are listed in boxes at the bottom of each branch.
### Detailed Analysis
The diagram maps specific defense mechanisms to their overarching strategic category. Below is a complete transcription of the text, organized by the hierarchical branches.
**Branch 1: No Setup**
* **Sub-Category:** Isolation
* **Defenses Listed:**
* DAWG [15]
* CSF-clearing [17]
* MI6 [25]
* IRONHIDE [26]
* Predictor state encryption [28]
**Branch 2: No Access w/o Authorization**
* **Defense Listed (Directly under the main category):**
* CSF-LFENCE[17]
**Branch 3: No Use w/o Authorization**
This branch has the most sub-categories.
* **Sub-Category 1: Basic No Use**
* NDA[23]
* SpectreGuard[18]
* ConTExT[27]
* SpecShieldERP[21]
* **Sub-Category 2: No Sensitive Use**
* SpecShield-ERP-[21]
* STI[22]
* **Sub-Category 3: Delay**
* CondSpec[16]
* EfficientSpec [20]
* DOLMA [33]
* **Sub-Category 4: Prevent**
* CSF-CFENCE[17]
* **Sub-Category 5: Shadow Structure**
* InvisiSpec[14]
* SafeSpec[19]
* MuonTrap[29]
* **Sub-Category 6: Roll-back**
* Cleanup-Spec[24]
**Branch 4: No Send w/o Authorization**
* **Sub-Category:** Isolation
* **Defenses Listed:**
* DAWG [15]
* CSF-clearing [17]
* MI6 [25]
* IRONHIDE[26]
### Key Observations
1. **Taxonomy Structure:** The diagram classifies defenses based on the stage of the speculative execution pipeline they aim to interrupt: preventing setup, blocking unauthorized access, preventing unauthorized use of speculatively loaded data, or blocking the exfiltration ("sending") of that data.
2. **Recurring Defenses:** Some defenses appear in multiple categories. For example, "DAWG [15]", "CSF-clearing [17]", "MI6 [25]", and "IRONHIDE[26]" are listed under both the "No Setup -> Isolation" and the "No Send w/o Authorization -> Isolation" branches. This suggests these mechanisms may employ isolation techniques that address multiple attack vectors or are foundational to both prevention strategies.
3. **Citation Density:** The "No Use w/o Authorization" branch is the most populated, containing six sub-categories and thirteen distinct defense citations. This indicates it is a major area of research focus for hardware mitigations.
4. **Specific Mechanism Grouping:** Defenses are grouped by their operational principle (e.g., "Delay," "Roll-back," "Shadow Structure"), providing a clear conceptual map of the solution space.
### Interpretation
This diagram serves as a **conceptual taxonomy for hardware security researchers and engineers**. It organizes a complex field of mitigations into a logical framework based on the *goal* of the defense (preventing setup, access, use, or send).
* **What it demonstrates:** It shows that defending against speculative execution attacks is not a single problem but a multi-faceted one, requiring interventions at different points in the hardware's speculative execution workflow. The proliferation of solutions under "No Use" suggests that completely preventing the speculative use of unauthorized data is particularly challenging and has inspired diverse architectural approaches (delaying, shadowing, rolling back).
* **Relationships:** The hierarchy illustrates a "divide-and-conquer" strategy for defense design. The top-level categories represent high-level security policies, while the lower levels represent the specific architectural techniques (isolation, fencing, encryption, etc.) used to enforce those policies.
* **Notable Pattern:** The repetition of certain defenses (like DAWG, CSF-clearing) across different branches highlights that a single hardware feature can provide defense-in-depth, mitigating threats at multiple stages of an attack chain. This is a desirable property in security design.
* **Limitation:** The diagram is a classification of *approaches* and *research prototypes* (as indicated by the citation numbers). It does not evaluate their effectiveness, performance overhead, or commercial adoption status. It is a map of the academic and research landscape up to its publication date.