## Hardware Defenses of Speculative Execution Attacks
### Overview
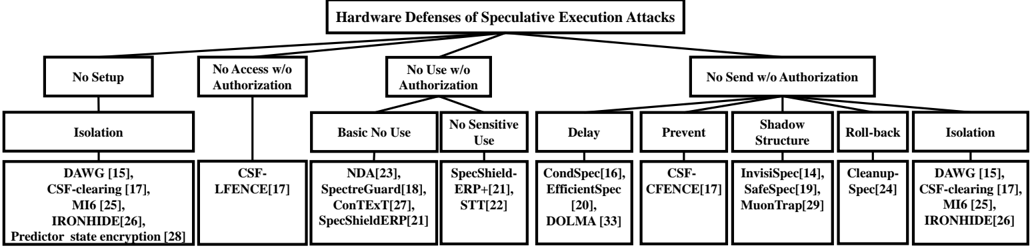
The diagram illustrates various hardware defenses against speculative execution attacks. These attacks occur when a processor executes instructions before the expected outcome is known, potentially leading to security vulnerabilities. The diagram categorizes defenses into four main types: No Setup, No Access w/o Authorization, No Use w/o Authorization, and No Send w/o Authorization. Each type is further divided into specific defenses such as Isolation, Delay, Prevent, Shadow Structure, Roll-back, and Cleanup.
### Components/Axes
- **No Setup**: This category includes defenses that do not require any setup, such as Isolation and Cleanup.
- **No Access w/o Authorization**: This category includes defenses that prevent unauthorized access, such as Basic No Use, No Sensitive Use, Delay, Prevent, Shadow Structure, and Roll-back.
- **No Use w/o Authorization**: This category includes defenses that prevent the use of certain instructions, such as SpecShield-ERP, CondSpec, EfficientSpec, and InvisiSpec.
- **No Send w/o Authorization**: This category includes defenses that prevent unauthorized sending of data, such as CSF-LFENCE, SpecShield-ERP, and MuonTrap.
### Detailed Analysis or ### Content Details
- **Isolation**: This defense involves isolating the speculative execution environment from the rest of the system to prevent unauthorized access and execution.
- **Delay**: This defense involves delaying the execution of instructions to prevent speculative execution.
- **Prevent**: This defense involves preventing the execution of certain instructions to prevent speculative execution.
- **Shadow Structure**: This defense involves creating a shadow structure to prevent unauthorized access and execution.
- **Roll-back**: This defense involves rolling back the state of the system to prevent unauthorized access and execution.
- **Cleanup**: This defense involves cleaning up the state of the system to prevent unauthorized access and execution.
### Key Observations
- **Isolation** and **Cleanup** are the most common defenses against speculative execution attacks.
- **Delay**, **Prevent**, **Shadow Structure**, and **Roll-back** are less common but still effective defenses.
- **SpecShield-ERP**, **CondSpec**, **EfficientSpec**, and **InvisiSpec** are specific defenses that target certain types of speculative execution attacks.
### Interpretation
The data suggests that hardware defenses against speculative execution attacks are crucial for maintaining the security of computer systems. The defenses illustrated in the diagram are effective in preventing unauthorized access, execution, and sending of data. The use of isolation, delay, prevent, shadow structure, roll-back, and cleanup can help prevent speculative execution attacks. The specific defenses such as SpecShield-ERP, CondSpec, EfficientSpec, and InvisiSpec are targeted at specific types of speculative execution attacks. Overall, the data highlights the importance of implementing effective hardware defenses against speculative execution attacks to ensure the security of computer systems.