\n
## Diagram: Deep Learning Model Identification via Side-Channel Attack
### Overview
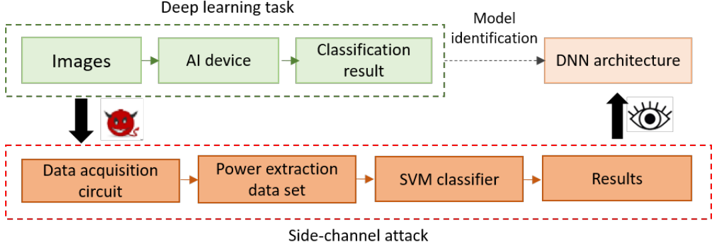
This diagram illustrates a system for identifying the architecture of a Deep Neural Network (DNN) used in a deep learning task through a side-channel attack. The diagram is divided into two main sections: a "Deep learning task" section (top, green dashed border) and a "Side-channel attack" section (bottom, red dashed border). Data flows from left to right within each section, and a connection exists between the output of the deep learning task and the input of the side-channel attack.
### Components/Axes
The diagram consists of the following components:
* **Deep learning task:**
* "Images" (input)
* "AI device" (processing unit)
* "Classification result" (output)
* "DNN architecture" (target of identification)
* **Side-channel attack:**
* "Data acquisition circuit" (input)
* "Power extraction data set" (intermediate data)
* "SVM classifier" (processing unit)
* "Results" (output)
* **Arrows:** Indicate the flow of data and information.
* **Icons:** A devil face icon is positioned above the arrow connecting "Images" to "Data acquisition circuit", and an eye icon is positioned above the arrow connecting "Classification result" to "Results".
* **Labels:** "Deep learning task" (top), "Model identification" (connecting the two sections), "Side-channel attack" (bottom).
### Detailed Analysis or Content Details
The diagram shows a process where images are fed into an AI device, which produces a classification result. The underlying DNN architecture is the target of identification. Simultaneously, a side-channel attack is performed. The data acquisition circuit captures power consumption data during the deep learning task, creating a power extraction data set. This data set is then fed into an SVM classifier, which produces results that are used to identify the DNN architecture.
The flow of information is as follows:
1. Images enter the "AI device" and are processed.
2. The "AI device" outputs a "Classification result".
3. The "Classification result" is used to identify the "DNN architecture".
4. The "Data acquisition circuit" monitors the "AI device" during processing.
5. The "Data acquisition circuit" generates a "Power extraction data set".
6. The "Power extraction data set" is input into the "SVM classifier".
7. The "SVM classifier" outputs "Results".
The devil face icon suggests a malicious intent or attack on the system, while the eye icon suggests observation or monitoring.
### Key Observations
The diagram highlights the vulnerability of deep learning models to side-channel attacks. The attacker doesn't directly access the model parameters but infers them by analyzing the power consumption of the device during operation. The use of an SVM classifier suggests a machine learning approach to analyze the power data and identify patterns related to the DNN architecture.
### Interpretation
This diagram demonstrates a security threat to deep learning systems. The attacker leverages the physical characteristics of the hardware (power consumption) to gain information about the model's internal structure. This is a significant concern, as it could allow an adversary to reverse-engineer a proprietary model or compromise its security. The diagram suggests a two-pronged approach: a standard deep learning task and a parallel side-channel attack. The attacker aims to correlate the classification results with the power consumption patterns to deduce the DNN architecture. The use of an SVM classifier indicates that the attacker is employing machine learning techniques to analyze the side-channel data. The icons of the devil and the eye emphasize the adversarial nature of the attack and the monitoring aspect, respectively. This diagram is a conceptual illustration of a potential attack vector and doesn't provide specific data or numerical values. It serves as a high-level overview of the attack process.