## Diagram: Homomorphic Encryption Data Flow Process
### Overview
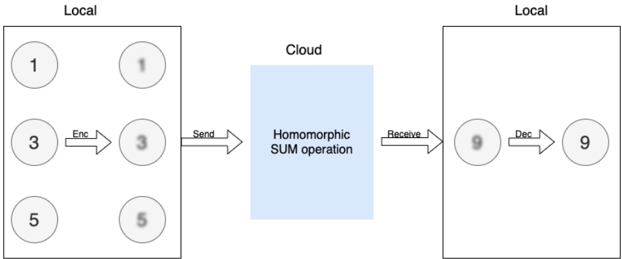
The image is a technical process diagram illustrating a homomorphic encryption workflow. It depicts data originating in a local environment, being encrypted and sent to a cloud service for a computation (a SUM operation), and the result being returned and decrypted back in a local environment. The diagram uses circles to represent data states and arrows to indicate operations and data flow.
### Components/Axes
The diagram is divided into three primary regions arranged horizontally:
1. **Left Region (Local Environment):** A rectangular box labeled "Local" at the top. It contains three rows of paired circles.
2. **Center Region (Cloud Environment):** A light blue rectangular box labeled "Cloud" at the top. It contains the text "Homomorphic SUM operation".
3. **Right Region (Local Environment):** A rectangular box labeled "Local" at the top. It contains a single row of paired circles.
**Labels and Text Elements:**
* **Region Labels:** "Local" (appears twice, top-left and top-right), "Cloud" (top-center).
* **Operation Labels:** "Enc" (on an arrow), "Send" (on an arrow), "Receive" (on an arrow), "Dec" (on an arrow).
* **Process Label:** "Homomorphic SUM operation" (inside the Cloud box).
* **Data Values:** The numbers "1", "3", "5", and "9" are displayed inside circles.
### Detailed Analysis
**Spatial Layout and Data Flow:**
The process flows from left to right.
1. **Left "Local" Box (Source Data):**
* Contains three vertically stacked rows.
* **Top Row:** A clear circle with the number `1` on the left. An arrow labeled `Enc` points to a blurred circle on the right containing a blurred representation of `1`.
* **Middle Row:** A clear circle with the number `3` on the left. An arrow labeled `Enc` points to a blurred circle on the right containing a blurred representation of `3`.
* **Bottom Row:** A clear circle with the number `5` on the left. An arrow labeled `Enc` points to a blurred circle on the right containing a blurred representation of `5`.
* **Interpretation:** The clear circles represent plaintext data (`1`, `3`, `5`). The `Enc` (Encrypt) operation transforms them into ciphertext, represented by the blurred circles.
2. **Data Transmission to Cloud:**
* A single arrow labeled `Send` originates from the general area of the three blurred circles in the left "Local" box and points to the "Cloud" box.
3. **"Cloud" Box (Computation):**
* Contains the text "Homomorphic SUM operation".
* **Interpretation:** This indicates that a computation (summation) is performed directly on the encrypted data (ciphertext) without decryption, which is the core property of homomorphic encryption.
4. **Data Transmission from Cloud:**
* An arrow labeled `Receive` originates from the "Cloud" box and points to the right "Local" box.
5. **Right "Local" Box (Result):**
* Contains one row.
* A blurred circle on the left contains a blurred representation of the number `9`.
* An arrow labeled `Dec` (Decrypt) points from this blurred circle to a clear circle on the right containing the number `9`.
* **Interpretation:** The result of the homomorphic SUM operation (`9`) is received in encrypted form (blurred circle) and then decrypted (`Dec`) to yield the final plaintext result (`9`).
### Key Observations
* **Mathematical Consistency:** The plaintext inputs are `1`, `3`, and `5`. Their sum is `9`, which matches the final decrypted output. This visually validates the correctness of the homomorphic SUM operation.
* **Visual Metaphor for Encryption:** The diagram uses a consistent visual metaphor: clear circles represent plaintext (readable data), and blurred circles represent ciphertext (obfuscated data).
* **Process Isolation:** The cloud only ever handles blurred (encrypted) data. The plaintext numbers `1`, `3`, `5`, and `9` are only ever visible within the "Local" boxes, emphasizing data privacy.
* **Simplified Model:** The diagram abstracts away complexities like key management, multiple ciphertexts being sent as a single batch, or the specific type of homomorphic encryption (e.g., partial, fully).
### Interpretation
This diagram serves as a pedagogical or conceptual illustration of **additive homomorphic encryption**. It demonstrates the fundamental value proposition: a client (Local) can offload a computation (SUM) to an untrusted server (Cloud) without revealing the underlying data.
* **What it demonstrates:** The system allows the cloud to compute on encrypted data (`Enc(1)`, `Enc(3)`, `Enc(5)`) and produce an encrypted result (`Enc(9)`), which only the client can decrypt. The cloud learns nothing about the inputs (`1,3,5`) or the output (`9`).
* **Relationships:** The "Local" entity is the data owner and holds the decryption key. The "Cloud" is a computational resource that is trusted to perform the operation correctly but not trusted with the data itself. The arrows (`Send`, `Receive`) represent the network interface between these two parties.
* **Notable Implication:** The core anomaly or "magic" highlighted is the `Homomorphic SUM operation` box. It performs a meaningful mathematical function (summation) on data it cannot read, which is a powerful primitive for privacy-preserving computation, secure auctions, or confidential machine learning. The diagram successfully isolates and explains this single, critical concept.