\n
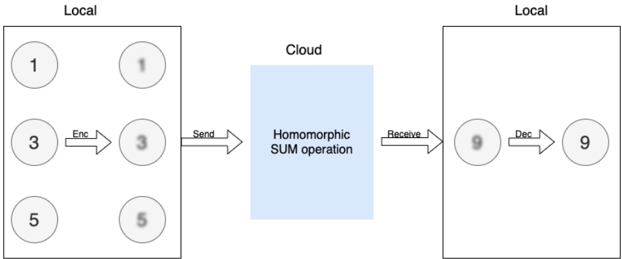
## Diagram: Homomorphic Sum Operation
### Overview
This diagram illustrates a simplified process of performing a homomorphic sum operation, moving data from a "Local" environment to a "Cloud" environment and back. It demonstrates encryption, transmission, computation in the cloud, and decryption.
### Components/Axes
The diagram is divided into three main sections:
1. **Local (Left):** Represents the initial data location. Contains three data points (1, 3, 5) and their encrypted counterparts.
2. **Cloud (Center):** Represents the cloud environment where the homomorphic sum operation is performed.
3. **Local (Right):** Represents the final data location after receiving and decrypting the result. Contains the received encrypted sum and the decrypted result.
Labels present:
* "Local" (appears twice, top-left and top-right)
* "Cloud" (center)
* "Enc" (Encryption)
* "Send"
* "Receive"
* "Dec" (Decryption)
* "Homomorphic SUM operation"
Data points: 1, 3, 5, 9
### Detailed Analysis or Content Details
The diagram shows the following flow:
1. **Local (Left):** Three data points are initially present: 1, 3, and 5.
2. **Encryption:** The data points 1, 3, and 5 are individually encrypted, labeled "Enc".
3. **Transmission:** The encrypted data is sent to the "Cloud". Labeled "Send".
4. **Cloud:** The "Homomorphic SUM operation" is performed on the encrypted data. The result is an encrypted sum.
5. **Reception:** The encrypted sum is received back at the "Local" environment. Labeled "Receive". The received value is 9.
6. **Decryption:** The encrypted sum (9) is decrypted, labeled "Dec", resulting in the final value of 9.
### Key Observations
The diagram demonstrates that the sum of the initial data points (1 + 3 + 5 = 9) is correctly computed in the cloud without decrypting the data. This highlights the core principle of homomorphic encryption – performing operations on encrypted data.
### Interpretation
This diagram illustrates a fundamental concept in privacy-preserving computation. Homomorphic encryption allows computations to be performed on encrypted data without revealing the underlying plaintext. This is crucial for scenarios where data privacy is paramount, such as cloud computing, secure data analysis, and machine learning. The diagram simplifies the process, but it effectively conveys the core idea: data can be processed in the cloud without compromising its confidentiality. The fact that the sum is 9 is a verification that the homomorphic operation worked correctly. The diagram does not provide details about the encryption scheme used or the computational complexity of the homomorphic sum operation. It is a conceptual illustration rather than a detailed technical specification.