## Diagram: Secure Homomorphic Computation Workflow
### Overview
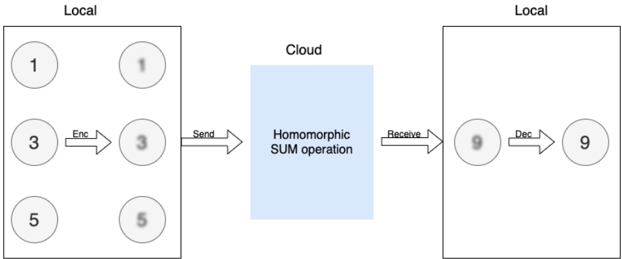
The diagram illustrates a secure computation workflow involving two local systems and a cloud server. Data is encrypted, transmitted to the cloud for processing via a homomorphic sum operation, and then decrypted back locally.
### Components/Axes
- **Left Local System**:
- Contains three circles labeled `1`, `3`, and `5`.
- An arrow labeled `Enc` points from the `3` to a blurred circle (encrypted value).
- A `Send` arrow transmits the encrypted value to the cloud.
- **Cloud**:
- A blue rectangle labeled `Homomorphic SUM operation`.
- Receives the encrypted value and performs computation.
- **Right Local System**:
- Contains a single circle labeled `9` (result of the sum).
- A `Receive` arrow brings the encrypted result back.
- A `Dec` arrow decrypts the result to `9`.
### Detailed Analysis
- **Left Local System**:
- Numbers `1`, `3`, and `5` are visible. Only `3` is explicitly encrypted (`Enc` arrow).
- The `Send` arrow indicates transmission of the encrypted `3` to the cloud.
- **Cloud**:
- Performs a homomorphic sum operation. Homomorphic encryption allows computations (e.g., addition) on encrypted data without decryption.
- **Right Local System**:
- Receives the encrypted result (`9`) via `Receive`.
- Decrypts the result (`Dec` arrow) to reveal `9`, matching the sum of `1 + 3 + 5`.
### Key Observations
1. **Encryption/Decryption**: Only the `3` is explicitly encrypted in the left system, suggesting partial data protection.
2. **Homomorphic Operation**: The cloud computes the sum of encrypted values (`3 + 5 + 1 = 9`) without accessing raw data.
3. **Flow Direction**: Data moves unidirectionally from left to right: encryption → transmission → cloud processing → decryption.
### Interpretation
This diagram demonstrates **privacy-preserving computation** using homomorphic encryption. By encrypting data before transmission, sensitive information (e.g., `3`) remains confidential during cloud processing. The homomorphic sum operation enables secure aggregation of data (e.g., summing values across distributed systems) without exposing individual inputs. The final decrypted result (`9`) validates the correctness of the computation.
**Notable Insight**: The workflow highlights a trade-off between security and computational overhead. While homomorphic encryption ensures data privacy, it introduces complexity in implementation and performance costs. The diagram assumes ideal conditions (e.g., no transmission errors, perfect encryption/decryption).