## System Architecture Diagram: Cloud-Local Emulator Interaction
### Overview
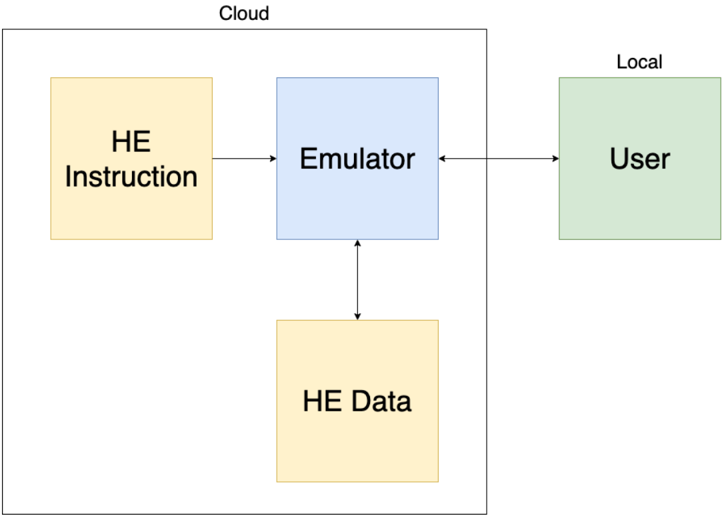
The image is a block diagram illustrating a system architecture that separates components between a "Cloud" environment and a "Local" environment. The diagram shows the flow of instructions and data between four primary components, with an "Emulator" acting as the central hub.
### Components/Axes
The diagram is divided into two main regions:
1. **Cloud Region:** A large, black-outlined rectangle labeled "Cloud" at the top center. It contains three component blocks.
2. **Local Region:** A smaller, black-outlined rectangle labeled "Local" at the top center, positioned to the right of the Cloud region. It contains one component block.
**Component Blocks (with color coding):**
* **HE Instruction:** A yellow rectangle located in the top-left quadrant of the Cloud region.
* **Emulator:** A blue rectangle located in the center of the Cloud region.
* **HE Data:** A yellow rectangle located in the bottom-center of the Cloud region.
* **User:** A green rectangle located in the center of the Local region.
**Flow Indicators (Arrows):**
* A single-headed arrow points from **HE Instruction** to **Emulator**.
* A double-headed arrow connects **Emulator** and **User**.
* A double-headed arrow connects **Emulator** and **HE Data**.
### Detailed Analysis
The diagram defines a clear data and control flow:
1. **Instruction Flow:** The "HE Instruction" component sends instructions (unidirectional flow) to the "Emulator."
2. **User Interaction:** The "User" in the local environment has a bidirectional interaction with the "Emulator" in the cloud. This suggests the user sends requests/inputs and receives outputs/responses.
3. **Data Access:** The "Emulator" has bidirectional access to "HE Data," indicating it can both read from and write to this data store.
The color coding groups components: yellow for "HE" (likely Homomorphic Encryption or a similar proprietary/technical term) related components (Instruction and Data), blue for the processing component (Emulator), and green for the end-user component.
### Key Observations
* **Centralized Emulator:** The Emulator is the sole connector between all other components. It is the architectural pivot point.
* **Environment Separation:** The diagram explicitly separates cloud-based processing and data from the local user interface.
* **Asymmetric Data Flow:** The flow from "HE Instruction" to "Emulator" is one-way, while all other connections are two-way. This implies instructions are provided to the system but not typically returned or confirmed in the same channel.
* **Component Grouping:** The use of the same yellow color for "HE Instruction" and "HE Data" strongly suggests they are part of the same subsystem or share a common characteristic (e.g., encrypted).
### Interpretation
This diagram depicts a **client-server or cloud-based processing architecture** where sensitive operations or data are handled remotely.
* **System Purpose:** The system appears designed to allow a local user to interact with a remote emulator that processes instructions and accesses a specific dataset ("HE Data"). The "HE" prefix is critical; if it stands for **Homomorphic Encryption**, this diagram illustrates a system where a user can perform computations (via the Emulator) on encrypted data (HE Data) without decrypting it, using encrypted instructions (HE Instruction). This would be a privacy-preserving architecture.
* **Relationships:** The User is decoupled from the raw data and instruction logic. All interaction is mediated by the Emulator, which could provide an abstraction layer, security, or computational offloading.
* **Notable Anomaly/Design Choice:** The unidirectional flow from "HE Instruction" to "Emulator" is interesting. It may indicate that instructions are pre-compiled, uploaded in batches, or form a one-way command stream, unlike the interactive dialogue with the user or the data access pattern.
* **Underlying Message:** The architecture prioritizes security and separation of concerns. The user never directly accesses "HE Data" or "HE Instruction"; the Emulator is the gatekeeper and processor, which is a common pattern in secure or resource-constrained computing environments.