## Code Snippet with Critical Steps
### Overview
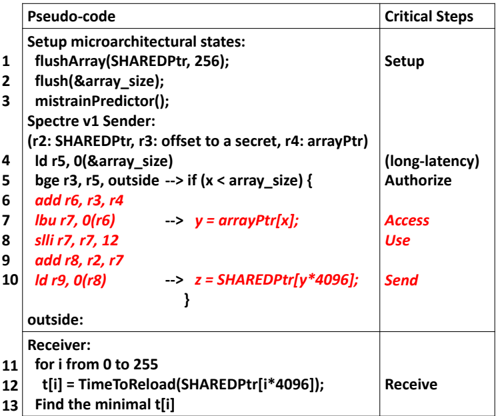
The image presents a code snippet, likely pseudo-code, alongside a description of the critical steps involved in its execution. The code appears to be related to a Spectre v1 vulnerability demonstration. It is divided into sections for setup, sender, and receiver, with corresponding critical steps labeled.
### Components/Axes
The image is structured as a table with two columns: "Pseudo-code" and "Critical Steps".
**Pseudo-code Column:**
* Contains code snippets and comments.
* Line numbers are present on the left side of the code.
**Critical Steps Column:**
* Describes the purpose of the corresponding code section.
### Detailed Analysis or ### Content Details
Here's a breakdown of the code and critical steps:
**Setup:**
* **Line 1:** `flushArray(SHAREDPtr, 256);` - Flushes an array.
* **Line 2:** `flush(&array_size);` - Flushes the address of `array_size`.
* **Line 3:** `mistrainPredictor();` - Mistrains the predictor.
* **Critical Step:** Setup
**Spectre v1 Sender:**
* **Line 4:** `ld r5, 0(&array_size)` - Loads the value of `array_size` into register `r5`.
* Registers used: r2 (SHAREDPtr), r3 (offset to a secret), r4 (arrayPtr)
* **Line 5:** `bge r3, r5, outside --> if (x < array_size) {` - Branch if `r3` is greater than or equal to `r5` to `outside`. This acts as a conditional check, simulating `if (x < array_size)`.
* Critical Step: (long-latency) Authorize
* **Line 6:** `add r6, r3, r4` - Adds the values in registers `r3` and `r4` and stores the result in `r6`.
* **Line 7:** `lbu r7, 0(r6) --> y = arrayPtr[x];` - Loads a byte from the memory location pointed to by `r6` into register `r7`. This is equivalent to `y = arrayPtr[x]`.
* Critical Step: Access
* **Line 8:** `slli r7, r7, 12` - Shifts the value in `r7` left by 12 bits.
* **Line 9:** `add r8, r2, r7` - Adds the values in registers `r2` and `r7` and stores the result in `r8`.
* **Line 10:** `ld r9, 0(r8) --> z = SHAREDPtr[y*4096];` - Loads the value from the memory location pointed to by `r8` into register `r9`. This is equivalent to `z = SHAREDPtr[y*4096]`.
* Critical Step: Send
* `outside:` - Label indicating the target of the branch instruction.
**Receiver:**
* **Line 11:** `for i from 0 to 255` - A loop that iterates from 0 to 255.
* **Line 12:** `t[i] = TimeToReload(SHAREDPtr[i*4096]);` - Measures the time it takes to reload `SHAREDPtr[i*4096]` and stores it in `t[i]`.
* **Line 13:** `Find the minimal t[i]` - Finds the minimum value in the `t[i]` array.
* **Critical Step:** Receive
### Key Observations
* The code simulates a Spectre v1 attack by accessing memory locations based on a potentially out-of-bounds index (`x`).
* The `mistrainPredictor()` function suggests an attempt to manipulate the branch predictor.
* The receiver code measures the time it takes to access different memory locations, which can be used to infer the value of the secret.
* The red text highlights the core operations related to the vulnerability.
### Interpretation
The code demonstrates a simplified version of the Spectre v1 attack. The sender code attempts to read a value from memory based on a potentially out-of-bounds index `x`. The branch predictor might incorrectly predict the branch outcome, allowing the code to access memory locations that it should not be able to access. The receiver code then measures the time it takes to access different memory locations, which can be used to infer the value of the secret. The `TimeToReload` function is crucial as it exploits the cache timing differences to reveal the accessed memory location. The overall goal is to leak information from a protected memory region by exploiting speculative execution and cache timing.