\n
## Table: Spectre v1 Sender/Receiver Pseudo-code
### Overview
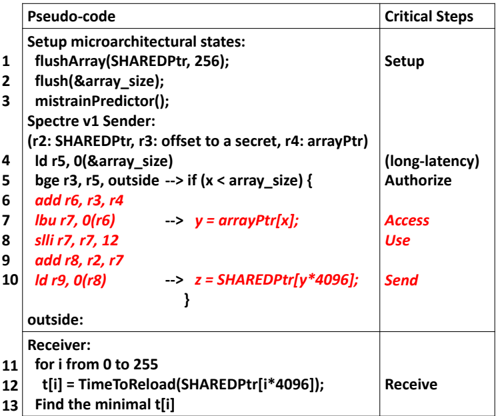
The image presents a table detailing pseudo-code for a Spectre v1 attack, outlining the steps involved in both the sender and receiver components. The table is divided into two main columns: "Pseudo-code" and "Critical Steps". The pseudo-code is numbered from 1 to 13, and the "Critical Steps" column provides a high-level description of the corresponding action.
### Components/Axes
The table has two columns:
* **Pseudo-code:** Contains the lines of code representing the attack sequence.
* **Critical Steps:** Describes the purpose of the corresponding pseudo-code lines.
### Detailed Analysis or Content Details
Here's a transcription of the pseudo-code and associated critical steps:
| Line | Pseudo-code | Critical Steps |
|------|-------------------------------------------|----------------|
| 1 | Setup microarchitectural states: | Setup |
| 2 | flushArray(SHAREDPtr, 256); | |
| 3 | flush(&array_size); | |
| 4 | mistrainPredictor(); | |
| 5 | Spectre v1 Sender: | |
| 6 | (r2: SHAREDPtr, r3: offset to a secret, r4: arrayPtr) | |
| 7 | ld r5, 0(array_size) | (long-latency) |
| 8 | bge r3, r5, outside -> if (x < array_size) { | Authorize |
| 9 | add r6, r3, r4 | |
| 10 | lbu r7, 0(r6) -> y = arrayPtr[x]; | Access |
| 11 | slli r7, 7, 12 | Use |
| 12 | add r8, r2, r7 | |
| 13 | ld r9, 0(r8) -> z = SHAREDPtr[y*4096]; | Send |
| 14 | } | |
| 15 | outside: | |
| 16 | Receiver: | |
| 17 | for i from 0 to 255 | |
| 18 | t[i] = TimeToReload(SHAREDPtr[i*4096]); | Receive |
| 19 | Find the minimal t[i] | |
**Notes on Pseudo-code:**
* `SHAREDPtr` appears to be a memory address.
* `array_size` is likely the size of an array.
* `x` is an offset into the array.
* `y` is the value read from the array at index `x`.
* `z` is a value read from memory based on `y`.
* `TimeToReload` is a function that measures the time it takes to access a memory location.
* `slli` is a shift left logical immediate instruction.
* `lbu` is a load byte unsigned instruction.
* `ld` is a load instruction.
* `bge` is a branch if greater or equal instruction.
* `add` is an add instruction.
### Key Observations
The pseudo-code outlines a side-channel attack (Spectre v1) that exploits speculative execution. The sender attempts to influence the processor's speculative execution path based on a secret value. The receiver measures the time it takes to access different memory locations to infer the secret. The `flushArray` and `mistrainPredictor` functions are used to control the processor's cache and branch prediction behavior. The `bge` instruction is a conditional branch that determines whether to proceed with the speculative execution.
### Interpretation
This pseudo-code demonstrates the core principles of the Spectre v1 attack. The attack relies on the fact that processors speculatively execute instructions before knowing whether they are valid. By carefully crafting the code, the attacker can cause the processor to speculatively execute instructions that access sensitive data. The attacker can then measure the time it takes to access different memory locations to infer the value of the sensitive data. The "Critical Steps" column highlights the key stages of the attack: setup, authorization, access, use, and send/receive. The use of `SHAREDPtr` suggests a shared memory region is being targeted. The multiplication by 4096 in the receiver's `TimeToReload` function suggests that the memory is being accessed in 4096-byte chunks, potentially corresponding to cache line size. The minimal time `t[i]` will correspond to the cache line containing the secret value. This is a classic example of a timing attack leveraging microarchitectural side channels.