## Security Architecture Comparison: Intel SGX, Arm TrustZone, AMD SEV
### Overview
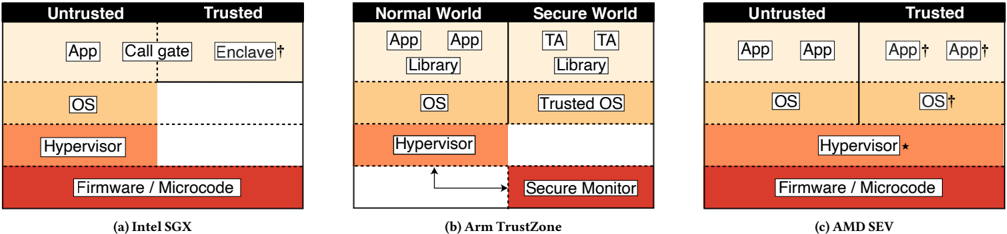
The image presents a comparative diagram illustrating the security architectures of Intel SGX, Arm TrustZone, and AMD SEV. Each architecture is depicted as a layered stack, differentiating between trusted and untrusted environments or normal and secure worlds. The diagram highlights the placement of key components such as applications, operating systems, hypervisors, and firmware within these security domains.
### Components/Axes
* **General Structure:** Each architecture (Intel SGX, Arm TrustZone, AMD SEV) is represented by a vertical stack divided into layers.
* **Intel SGX (a):**
* **Top Layer:** Divided into "Untrusted" and "Trusted" regions.
* Untrusted: Contains "App".
* Trusted: Contains "Call gate" and "Enclave†".
* **Second Layer:** "OS" spans partially into the "Untrusted" region.
* **Third Layer:** "Hypervisor" spans partially into the "Untrusted" region.
* **Bottom Layer:** "Firmware / Microcode" spans the entire width.
* **Arm TrustZone (b):**
* Divided into "Normal World" and "Secure World".
* **Top Layer:**
* Normal World: Contains "App" and "Library".
* Secure World: Contains "TA" (Trusted Application) and "Library".
* **Second Layer:**
* Normal World: Contains "OS".
* Secure World: Contains "Trusted OS".
* **Third Layer:** "Hypervisor" in the "Normal World".
* **Bottom Layer:** "Secure Monitor" in the "Secure World". An arrow points from the "Hypervisor" to the "Secure Monitor".
* **AMD SEV (c):**
* Divided into "Untrusted" and "Trusted" regions.
* **Top Layer:**
* Untrusted: Contains "App".
* Trusted: Contains "App†" (appears twice).
* **Second Layer:**
* Untrusted: Contains "OS".
* Trusted: Contains "OS†".
* **Third Layer:** "Hypervisor*" spans the entire width.
* **Bottom Layer:** "Firmware / Microcode" spans the entire width.
### Detailed Analysis
* **Intel SGX:** The SGX architecture isolates a portion of the application ("Enclave") and related functions ("Call gate") into a trusted region, while the OS and Hypervisor are partially untrusted. The Firmware/Microcode forms the base layer.
* **Arm TrustZone:** TrustZone separates the system into "Normal World" and "Secure World". Applications and libraries exist in both worlds, with a "Trusted OS" in the "Secure World". The "Hypervisor" in the "Normal World" communicates with the "Secure Monitor" in the "Secure World".
* **AMD SEV:** SEV architecture places the "Hypervisor*" and "Firmware/Microcode" as the foundation, with applications and OS components split between "Untrusted" and "Trusted" regions.
### Key Observations
* **Trust Boundaries:** Each architecture defines clear boundaries between trusted and untrusted environments, albeit with different approaches.
* **Component Placement:** The placement of components like the OS and Hypervisor varies significantly across the architectures, reflecting different security models.
* **Secure Monitor:** Arm TrustZone explicitly includes a "Secure Monitor" for managing the transition between the normal and secure worlds.
* **Annotations:** The dagger symbol "†" appears next to "Enclave" in Intel SGX, "App" and "OS" in AMD SEV. The asterisk symbol "*" appears next to "Hypervisor" in AMD SEV.
### Interpretation
The diagram provides a high-level overview of the security architectures of Intel SGX, Arm TrustZone, and AMD SEV. It highlights the different approaches each architecture takes to isolate sensitive code and data from potentially malicious software. Intel SGX focuses on creating secure enclaves within the CPU, Arm TrustZone separates the system into normal and secure worlds, and AMD SEV encrypts virtual machine memory to protect it from the hypervisor. The placement of components like the OS and Hypervisor within these architectures reflects the different trust models and security goals of each system. The annotations (dagger and asterisk symbols) likely indicate specific features or limitations of each architecture, but without further context, their exact meaning is unclear.