## Diagram: Trusted Execution Environments (TEEs) Architecture Comparison
### Overview
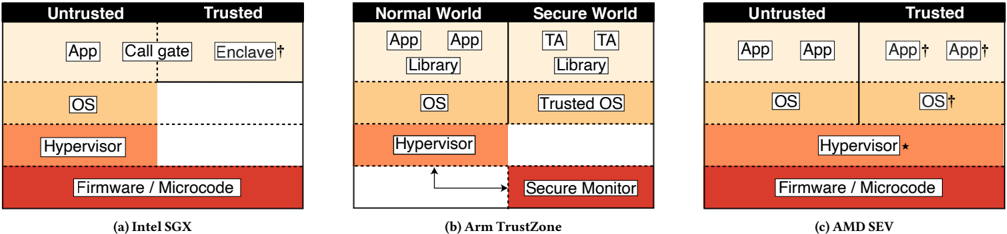
The image compares three Trusted Execution Environment (TEE) architectures: **Intel SGX**, **Arm TrustZone**, and **AMD SEV**. Each diagram is divided into **Untrusted** and **Trusted** layers, with components stacked vertically. Colors denote trust levels (red = Firmware/Microcode, orange = Hypervisor, etc.), and symbols (†, *) indicate footnotes or special states.
---
### Components/Axes
#### Labels and Sections
1. **Intel SGX (a)**
- **Untrusted**: App, Call gate, Enclave†
- **Trusted**: OS, Hypervisor, Firmware/Microcode
- **Color Coding**:
- Red: Firmware/Microcode
- Orange: Hypervisor
- Beige: OS/App/Enclave
2. **Arm TrustZone (b)**
- **Normal World**: App, Library, OS, Hypervisor
- **Secure World**: TA, Library, Trusted OS, Secure Monitor
- **Color Coding**:
- Red: Secure Monitor
- Orange: Hypervisor
- Beige: OS/App/Library
3. **AMD SEV (c)**
- **Untrusted**: App, OS, Hypervisor
- **Trusted**: App†, OS†, Hypervisor*, Firmware/Microcode
- **Color Coding**:
- Red: Firmware/Microcode
- Orange: Hypervisor
- Beige: OS/App
#### Spatial Grounding
- All diagrams use **vertical stacking** to represent trust levels.
- **Legends**: Implicit via color coding (no explicit legend box).
- **Symbols**:
- †: Appears in Intel SGX (Enclave) and AMD SEV (App/OS).
- *: Appears in AMD SEV (Hypervisor).
---
### Detailed Analysis
#### Intel SGX (a)
- **Untrusted Layer**:
- Apps run in the **Enclave** (isolated memory regions).
- **Call gate** mediates communication between untrusted and trusted layers.
- **Trusted Layer**:
- **OS** and **Hypervisor** manage resources.
- **Firmware/Microcode** (red) forms the base layer.
#### Arm TrustZone (b)
- **Normal World**:
- Standard OS and apps operate here.
- **Hypervisor** bridges Normal and Secure Worlds.
- **Secure World**:
- **Trusted OS** and **TA** (Trusted Applications) run in isolation.
- **Secure Monitor** (red) acts as a privileged layer for secure operations.
#### AMD SEV (c)
- **Untrusted Layer**:
- Apps and OS run in non-isolated memory.
- **Hypervisor** manages memory allocation.
- **Trusted Layer**:
- **App†** and **OS†** indicate isolated or encrypted memory regions.
- **Hypervisor*** may denote a modified or enhanced role compared to Intel/Arm.
---
### Key Observations
1. **Trust Boundaries**:
- Intel SGX and AMD SEV separate apps into explicit **Untrusted/Trusted** zones.
- Arm TrustZone uses **Normal World** (untrusted) and **Secure World** (trusted).
2. **Footnotes/Symbols**:
- † in Intel/AMD diagrams likely denotes **enclave-specific** or **encrypted** components.
- * in AMD SEV suggests a **hypervisor variant** optimized for SEV.
3. **Secure Monitor**: Unique to Arm TrustZone, acting as a privileged layer for secure operations.
---
### Interpretation
- **Intel SGX** emphasizes **enclave-based isolation**, with a clear call gate for secure communication.
- **Arm TrustZone** focuses on **world separation**, with a dedicated **Secure Monitor** for low-level security.
- **AMD SEV** extends trust to apps and OS via encrypted memory (denoted by †), with a hypervisor adapted for SEV.
- **Commonality**: All architectures rely on **Firmware/Microcode** (red) as the foundational trust layer.
- **Divergence**: Arm’s **Secure Monitor** and AMD’s **Hypervisor*** highlight architectural differences in managing trust.
This comparison underscores how TEEs balance isolation, performance, and security across hardware vendors.