## [Technical Diagram]: Knowledge Graph, Query, and Reasoning Process
### Overview
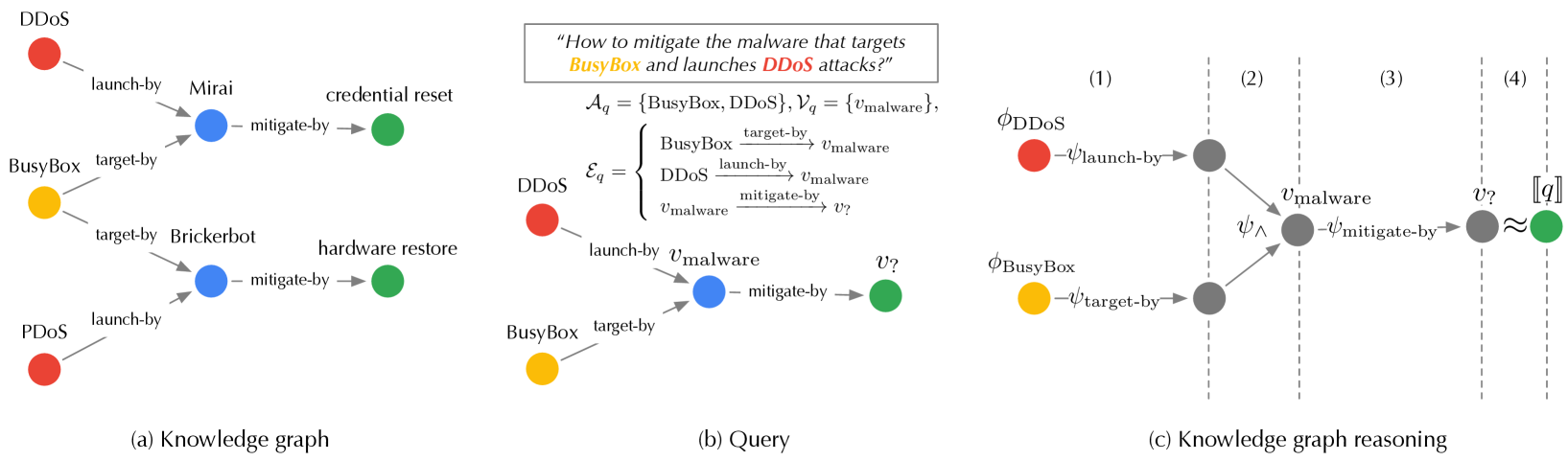
The image is a technical diagram illustrating a **knowledge graph**, a **formal query**, and a **reasoning process** to answer the query. It has three labeled sub-diagrams: (a) Knowledge graph, (b) Query, and (c) Knowledge graph reasoning. The diagram uses color-coded nodes (red, yellow, blue, green) and labeled edges to represent entities (e.g., attacks, malware, mitigations) and their relationships, with a structured query and step-by-step reasoning.
### Components/Elements
#### Section (a): Knowledge Graph
- **Nodes (Entities)**:
- Red: `DDoS`, `PDoS` (attack types).
- Yellow: `BusyBox` (target system).
- Blue: `Mirai`, `Brickerbot` (malware).
- Green: `credential reset`, `hardware restore` (mitigation actions).
- **Edges (Relationships)**:
- `launch-by`: `DDoS` → `Mirai`; `PDoS` → `Brickerbot` (attacks launch malware).
- `target-by`: `BusyBox` → `Mirai`; `BusyBox` → `Brickerbot` (malware targets `BusyBox`).
- `mitigate-by`: `Mirai` → `credential reset`; `Brickerbot` → `hardware restore` (malware mitigated by actions).
#### Section (b): Query
- **Text Query**: *“How to mitigate the malware that targets BusyBox and launches DDoS attacks?”*
- **Formal Query (Set Notation)**:
- \( \mathcal{A}_q = \{\text{BusyBox}, \text{DDoS}\} \) (entities in the query).
- \( \mathcal{V}_q = \{v_{\text{malware}}\} \) (variable for the malware).
- \( \mathcal{E}_q = \left\{ \text{BusyBox} \xrightarrow{\text{target-by}} v_{\text{malware}}, \text{DDoS} \xrightarrow{\text{launch-by}} v_{\text{malware}}, v_{\text{malware}} \xrightarrow{\text{mitigate-by}} v? \right\} \) (relationships defining the problem).
- **Diagram**:
- `DDoS` (red) → `launch-by` → \( v_{\text{malware}} \) (blue).
- `BusyBox` (yellow) → `target-by` → \( v_{\text{malware}} \) (blue).
- \( v_{\text{malware}} \) (blue) → `mitigate-by` → \( v? \) (green, unknown mitigation).
#### Section (c): Knowledge Graph Reasoning
- **Steps (1)–(4)**:
1. **Step (1)**: \( \phi_{\text{DDoS}} \) (red) → \( \psi_{\text{launch-by}} \) → gray node; \( \phi_{\text{BusyBox}} \) (yellow) → \( \psi_{\text{target-by}} \) → gray node.
2. **Step (2)**: Two gray nodes → \( \psi_{\land} \) (logical AND) → \( v_{\text{malware}} \) (gray, combined condition).
3. **Step (3)**: \( v_{\text{malware}} \) (gray) → \( \psi_{\text{mitigate-by}} \) → \( v? \) (gray, mitigation candidate).
4. **Step (4)**: \( v? \) (gray) ≈ \( \llbracket q \rrbracket \) (green, answer to the query).
### Detailed Analysis
- **Section (a)**: The knowledge graph models security relationships: attacks (red) launch malware (blue), which targets `BusyBox` (yellow) and is mitigated by actions (green).
- **Section (b)**: The query formalizes the problem: find the mitigation for malware that targets `BusyBox` and launches `DDoS`. The diagram visualizes the relationships needed to solve it.
- **Section (c)**: The reasoning process combines the two conditions (DDoS launch-by and BusyBox target-by) to identify the malware, then finds its mitigation—matching the query’s answer.
### Key Observations
- **Color Consistency**: Red (attacks), yellow (target), blue (malware), green (mitigations) are consistent across sections.
- **Formalization**: The query uses set notation (\( \mathcal{A}_q, \mathcal{V}_q, \mathcal{E}_q \)) to structure the problem, enabling automated reasoning.
- **Logical Combination**: Step (2) uses \( \psi_{\land} \) (AND) to combine the two conditions, showing how the knowledge graph resolves the query.
### Interpretation
This diagram demonstrates a **knowledge graph-based approach** to security analysis. The knowledge graph (a) models complex relationships between attacks, targets, malware, and mitigations. The query (b) formalizes the problem, and the reasoning (c) shows how to combine graph relationships to answer the query. This is valuable for automated threat analysis, where knowledge graphs enable structured reasoning about security events. The color coding and logical steps make it easy to trace how the query is resolved, highlighting the power of graph-based reasoning in cybersecurity.
(Note: All text and relationships are transcribed directly from the image. The diagram uses formal logic and set notation to structure the problem, with color-coded nodes for clarity.)