\n
## Diagram: Knowledge Graph for Malware Mitigation
### Overview
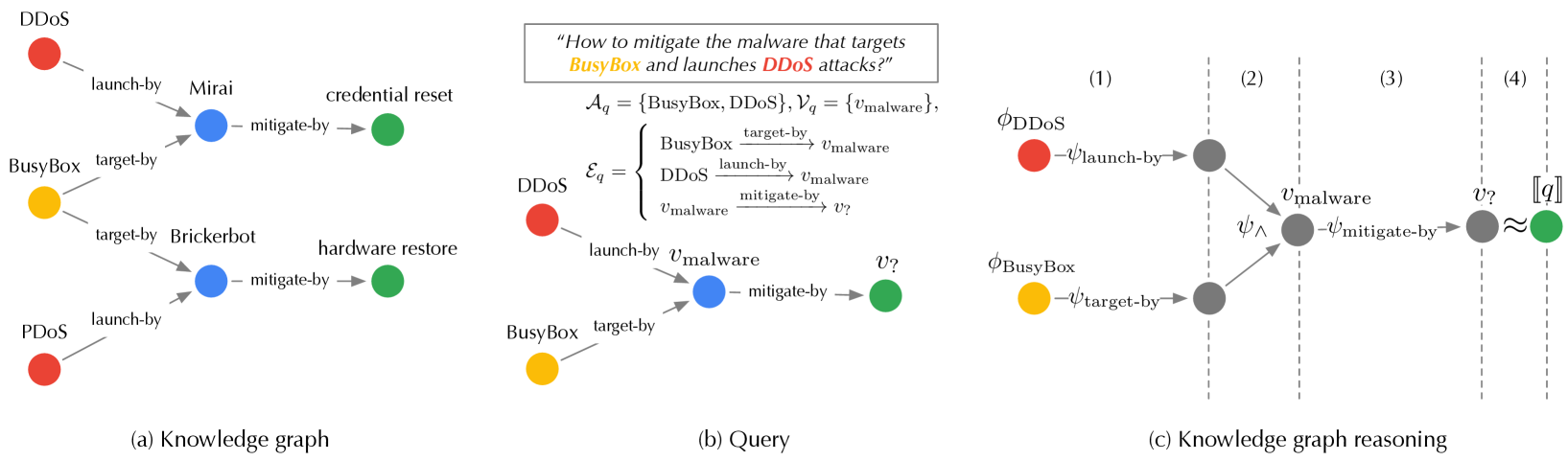
The image presents a diagram illustrating a knowledge graph and its application to a malware mitigation query. It is divided into three main sections: (a) a knowledge graph representing relationships between malware and targets, (b) a formal query representation, and (c) a step-by-step visualization of knowledge graph reasoning to answer the query.
### Components/Axes
The diagram consists of nodes representing entities (e.g., DDoS, BusyBox, Mirai) and directed edges representing relationships between them (e.g., "launch-by", "target-by", "mitigate-by"). The query section includes mathematical notation and variable definitions. The reasoning section shows a series of graph transformations.
### Detailed Analysis or Content Details
**(a) Knowledge Graph:**
* **Nodes:**
* DDoS (Red)
* BusyBox (Yellow)
* Mirai (Green)
* Brickerbot (Green)
* PDoS (Red)
* `vmalware` (Variable, not colored)
* **Edges:**
* DDoS `launch-by` Mirai
* Mirai `target-by` BusyBox
* BusyBox `target-by` Brickerbot
* Brickerbot `mitigate-by` hardware restore
* PDoS `launch-by` BusyBox
* BusyBox `target-by` PDoS
* DDoS `mitigate-by` credential reset
* The graph shows a chain of attacks: DDoS launched by Mirai targeting BusyBox, and PDoS launched by BusyBox targeting PDoS. Mitigation strategies are also shown.
**(b) Query:**
* **Text:** "How to mitigate the malware that targets BusyBox and launches DDoS attacks?"
* **Mathematical Formulation:**
* `Aq = {BusyBox, DDoS}, Vq = {vmalware}`
* `E'q =` (Equation showing relationships between BusyBox, DDoS, and `vmalware` with edges labeled "target-by", "launch-by", and "mitigate-by")
* The equation shows a relationship between BusyBox, DDoS, and a variable `vmalware` representing the malware.
**(c) Knowledge Graph Reasoning:**
This section shows a series of graph transformations, numbered (1) through (4).
* **(1):** `ΦDDoS` with an edge `vlaunch-by` pointing to `vmalware`.
* **(2):** `Ψ` (conjunction symbol) with edges `vlaunch-by` from `DDoS` to `vmalware` and `vtarget-by` from `BusyBox` to `vmalware`.
* **(3):** `vmalware` with an edge `vmitigate-by` pointing to `?`.
* **(4):** `?` (variable) with a bracket `[q]`. The bracket suggests the result of the query.
### Key Observations
* The knowledge graph represents a network of cyberattacks and mitigation strategies.
* The query aims to find a mitigation strategy for malware that both targets BusyBox and launches DDoS attacks.
* The reasoning process involves identifying the malware (`vmalware`) that satisfies the query conditions and then finding a mitigation strategy for that malware.
* The use of mathematical notation formalizes the query and reasoning process.
### Interpretation
The diagram demonstrates a knowledge graph-based approach to cybersecurity threat mitigation. The knowledge graph stores information about attacks, targets, and mitigation strategies. A formal query is constructed to represent the mitigation goal. The reasoning process then traverses the knowledge graph to identify the relevant malware and its corresponding mitigation strategy.
The diagram highlights the power of knowledge graphs in representing complex relationships and enabling automated reasoning for cybersecurity tasks. The use of mathematical notation provides a precise and unambiguous way to define queries and reasoning steps. The reasoning process shown in (c) is a simplified illustration of how a knowledge graph can be used to answer complex security questions. The final result, represented by "?", indicates the mitigation strategy that satisfies the query conditions.
The diagram suggests a system where security analysts can formulate queries in natural language, which are then translated into formal queries that can be executed on the knowledge graph to identify appropriate mitigation strategies. This approach can help to automate the threat response process and improve the efficiency of security operations.