## Knowledge Graph and Mitigation Query Diagram
### Overview
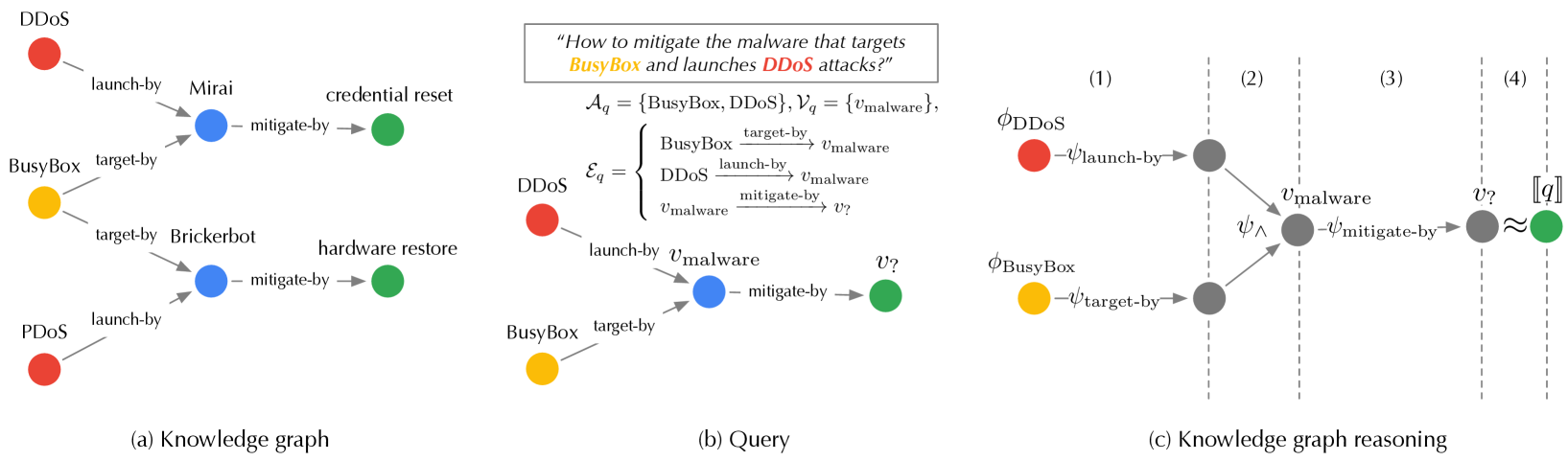
The image presents a three-part technical diagram illustrating malware mitigation strategies through knowledge graph reasoning. It combines entity-relationship mapping, formal query formulation, and logical inference steps to address DDoS attack mitigation targeting BusyBox.
### Components/Axes
**Part (a): Knowledge Graph**
- **Nodes**:
- Red: DDoS (Distributed Denial of Service)
- Yellow: BusyBox
- Blue: Mirai, Brickerbot (malware variants)
- Green: Mitigation outcomes (credential reset, hardware restore)
- **Edges**:
- "launch-by" (red → blue)
- "target-by" (yellow → blue)
- "mitigate-by" (blue → green)
- "credential reset" (blue → green)
- "hardware restore" (blue → green)
**Part (b): Query**
- **Formal Representation**:
- `A_q = {BusyBox, DDoS}`
- `V_q = {v_malware}`
- Edge relationships:
- `BusyBox →target-by→ v_malware`
- `DDoS →launch-by→ v_malware`
- `v_malware →mitigate-by→ v?`
**Part (c): Knowledge Graph Reasoning**
- **Inference Steps**:
1. `φ_DDoS →launch-by→ v_malware`
2. `φ_BusyBox →target-by→ v_malware`
3. `v_malware →mitigate-by→ v?`
4. Conclusion: `≈` (approximate equivalence to mitigation outcome)
### Detailed Analysis
**Part (a) Relationships**:
- DDoS attacks (red) are launched by Mirai/Brickerbot (blue)
- BusyBox (yellow) is targeted by the same malware
- Mitigation pathways exist from malware to credential reset/hardware restore
**Part (b) Query Structure**:
- Sets A_q and V_q define the attack surface and malware variables
- Mathematical notation shows directional relationships between components
**Part (c) Reasoning Flow**:
- Step 1: DDoS attack originates from malware
- Step 2: BusyBox is compromised by malware
- Step 3: Malware mitigation leads to unknown outcome (v?)
- Step 4: Approximate equivalence to mitigation success
### Key Observations
1. **Color Consistency**: Red (DDoS), yellow (BusyBox), blue (malware), green (mitigation) maintain consistent color coding across all parts
2. **Bidirectional Relationships**: Malware acts as both attacker (launch/target) and victim (mitigate)
3. **Mitigation Pathways**: Two distinct mitigation outcomes shown (credential reset/hardware restore)
4. **Logical Inference**: Reasoning steps connect attack vectors to mitigation actions through malware
### Interpretation
This diagram demonstrates a cybersecurity knowledge graph framework for analyzing and mitigating DDoS attacks targeting BusyBox. The malware (Mirai/Brickerbot) serves as both attack vector and attack target, creating complex attack surfaces. The formal query (b) translates real-world relationships into mathematical notation, while the reasoning steps (c) show how to derive mitigation strategies from these relationships. The approximate equivalence symbol (≈) in step 4 suggests probabilistic rather than deterministic mitigation outcomes, acknowledging real-world uncertainty in cybersecurity responses.