## Diagram: Interaction between LLM Agents and Data Storage
### Overview
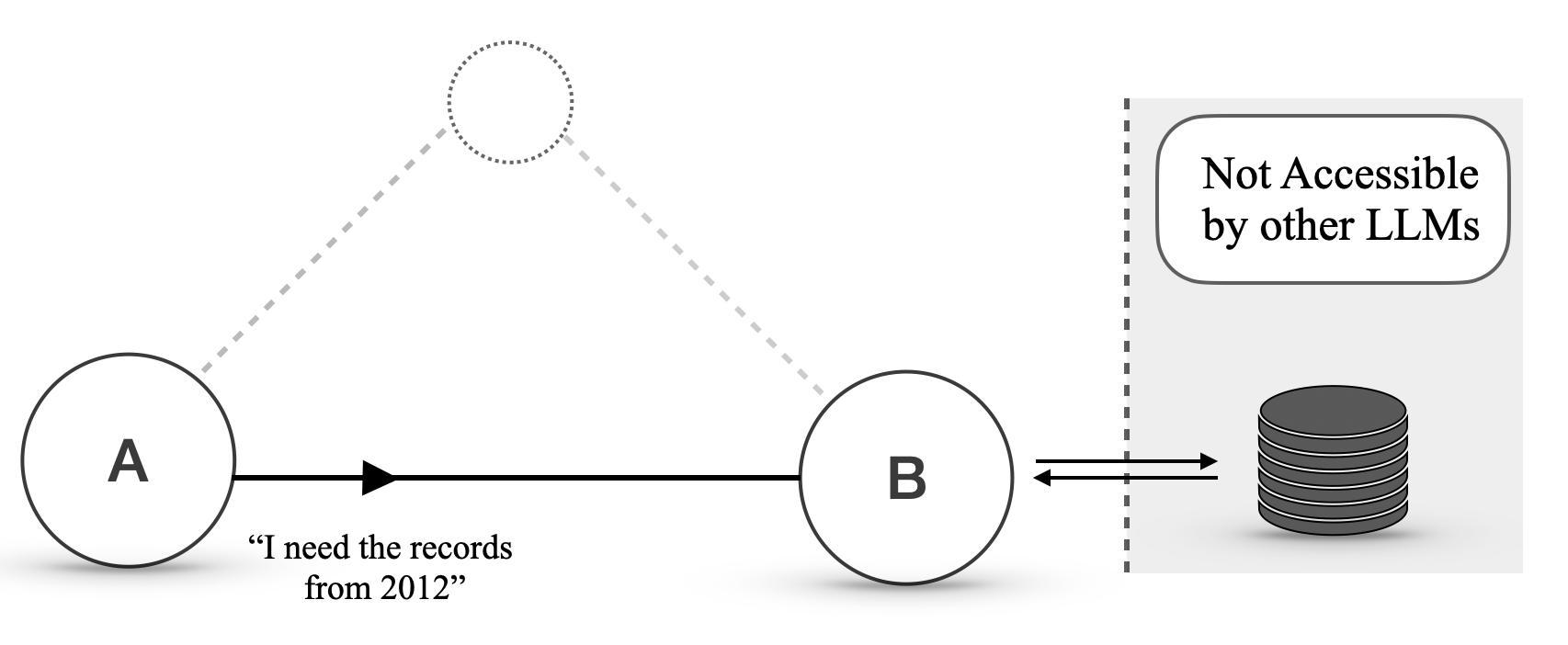
This diagram illustrates a conceptual model of interaction between two Large Language Model (LLM) agents, labeled 'A' and 'B', and a data storage system. Agent A communicates a request to Agent B, which then interacts with a data store. A key aspect highlighted is that the data store is not accessible by other LLMs.
### Components/Axes
* **Agent A**: Represented by a solid circle with the label "A" inside.
* **Agent B**: Represented by a solid circle with the label "B" inside.
* **Dotted Circle**: A dashed circle, positioned above and between Agents A and B, with a dotted outline. This element is not explicitly labeled but suggests a potential or indirect connection.
* **Arrow from A to B**: A solid black arrow pointing from Agent A to Agent B, indicating a flow of information or a request.
* **Text below Arrow**: The text "“I need the records from 2012”" is positioned below the arrow originating from Agent A, representing a specific query or instruction.
* **Double-headed Arrow between B and Data Store**: A double-headed black arrow connecting Agent B to the data storage icon, indicating bidirectional communication or data transfer.
* **Data Storage Icon**: A stacked cylinder icon representing a database or data repository.
* **Dashed Vertical Line**: A dashed vertical line to the right of Agent B, separating the agent interaction area from the data storage area.
* **Rounded Rectangle with Text**: A rounded rectangle positioned to the top-right of the dashed vertical line, containing the text "Not Accessible by other LLMs". This indicates a restriction on access to the data store.
### Detailed Analysis or Content Details
* **Agent A to Agent B Communication**: Agent A initiates a communication with Agent B. The content of this communication is a specific request: "“I need the records from 2012”". This implies Agent A is delegating a task or seeking information from Agent B.
* **Agent B to Data Store Interaction**: Agent B interacts with the data storage system. The double-headed arrow suggests that Agent B can both read from and potentially write to this data store.
* **Data Store Accessibility**: The data storage system is explicitly marked as "Not Accessible by other LLMs". This suggests a controlled access mechanism, where only specific agents (in this case, likely Agent B, and indirectly Agent A through B) can interact with it.
* **Dotted Connection**: The dashed lines and dotted circle suggest a potential, but not direct or active, connection or relationship between Agent A and a hypothetical entity, or perhaps a less defined interaction path.
### Key Observations
* **Hierarchical or Delegated Interaction**: The diagram suggests a pattern where Agent A relies on Agent B to access specific data.
* **Controlled Data Access**: The data store is a protected resource, not openly available to all LLMs. This implies a security or architectural design choice.
* **Specific Data Request**: The explicit request from Agent A ("records from 2012") indicates that LLMs can make specific, context-aware queries.
### Interpretation
This diagram illustrates a common pattern in distributed AI systems or multi-agent architectures. Agent A, perhaps a user-facing LLM or a different functional agent, requires specific data that it cannot directly access. It delegates this request to Agent B, which is designed to interact with a specialized, secured data store.
The "Not Accessible by other LLMs" label is crucial. It implies that the data store contains sensitive information, proprietary data, or data that requires specific processing or authorization that only Agent B possesses. This architecture prevents unauthorized access and ensures data integrity and security. The dotted connection might represent a fallback mechanism, a less common interaction path, or a conceptual link that is not actively utilized in this specific scenario. The overall system demonstrates a modular approach to LLM interaction, where specialized agents handle specific tasks like data retrieval from restricted sources. This design promotes efficiency and security by isolating critical data access.