## Diagram: System Interaction and Data Access Flow
### Overview
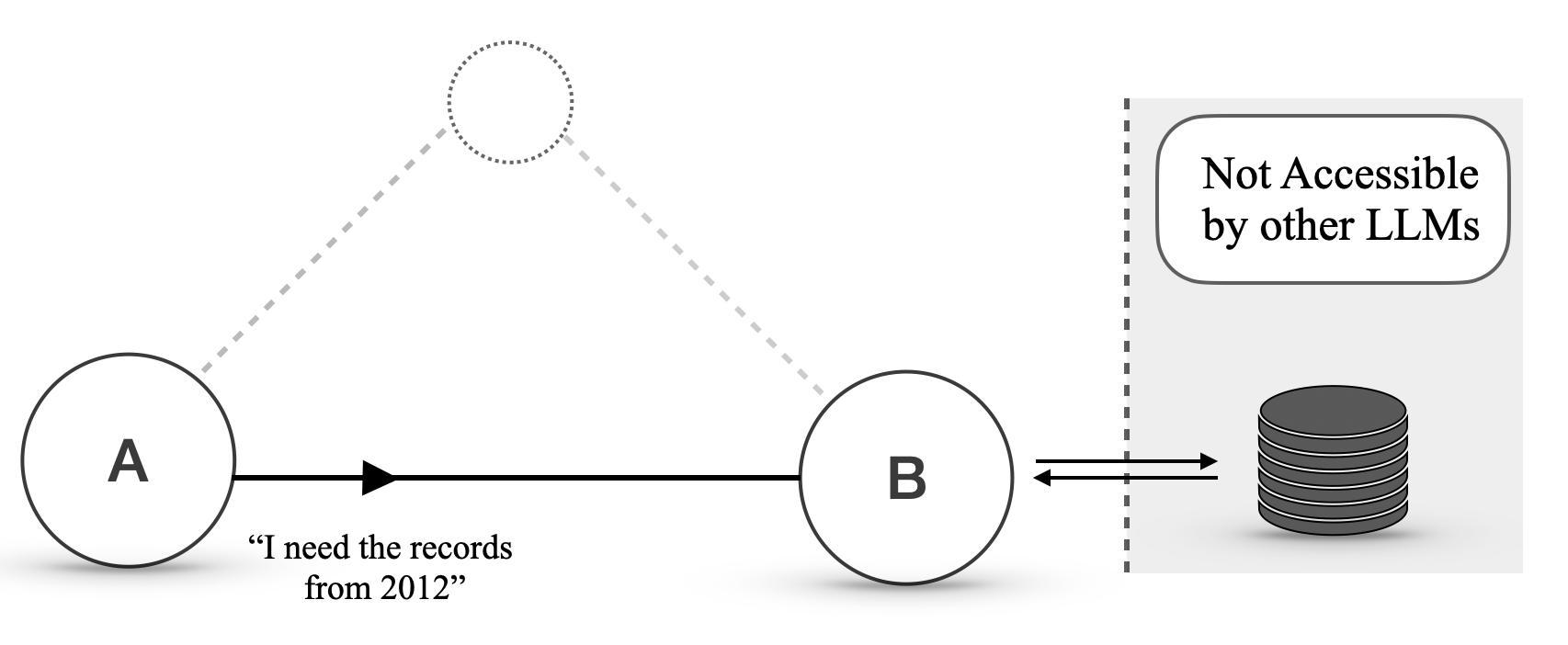
The image is a technical diagram illustrating a communication and data retrieval process between two entities (labeled A and B) and a database. The diagram emphasizes a restricted access model, where the database is explicitly marked as inaccessible to other Large Language Models (LLMs).
### Components/Axes
The diagram consists of the following visual elements and text labels:
1. **Entity A**: A circle on the left side containing the label **"A"**.
2. **Entity B**: A circle in the center containing the label **"B"**.
3. **Database**: A cylindrical database icon on the right side.
4. **Communication Arrow**: A solid black arrow pointing from A to B.
5. **Request Text**: Text positioned below the arrow from A to B, reading: **"I need the records from 2012"**.
6. **Bidirectional Arrows**: Two parallel, horizontal arrows between B and the database, indicating a two-way data exchange.
7. **Access Restriction Zone**: A shaded gray rectangle on the right, containing the database. A vertical dashed line separates this zone from the rest of the diagram.
8. **Access Restriction Label**: Text inside a rounded rectangle within the shaded zone, reading: **"Not Accessible by other LLMs"**.
9. **Dotted Path**: A faint, dotted circle positioned above and between A and B. Dotted lines connect this circle to both A and B, suggesting an alternative, indirect, or potential communication path.
### Detailed Analysis
The diagram depicts a specific sequence and set of relationships:
* **Primary Flow**: The main interaction is a direct, linear request. Entity **A** sends a specific query (**"I need the records from 2012"**) to Entity **B** via a solid arrow.
* **Data Retrieval**: Entity **B** then engages in a bidirectional exchange with the database, as shown by the two parallel arrows. This implies B has the capability to query the database and receive data.
* **Spatial Grounding & Access Control**: The database and the bidirectional arrows are contained within a shaded gray box on the right side of the image. This box is demarcated by a vertical dashed line. The label **"Not Accessible by other LLMs"** is placed directly above the database icon within this zone, clearly defining the access boundary.
* **Alternative Path**: A dotted circle with dotted lines to both A and B suggests a secondary or potential connection that is not the primary focus of this specific interaction flow.
### Key Observations
1. **Exclusive Access**: The most prominent feature is the explicit restriction on the database. The system is designed so that only Entity **B** (or the system it represents) can directly access the data store. Other LLMs are barred from this access.
2. **Role Specialization**: Entity **A** acts as a requester or client, while Entity **B** acts as a gateway, intermediary, or privileged agent with exclusive data retrieval rights.
3. **Specific Data Request**: The query is not generic; it specifies a temporal filter (**"from 2012"**), indicating the system handles structured or time-series data.
4. **Visual Hierarchy**: The solid lines and central placement of the A->B->Database flow establish it as the primary process. The dotted path is visually subordinate.
### Interpretation
This diagram illustrates a **secure data access architecture** for an AI or LLM-based system. The core message is one of **controlled privilege**.
* **What it demonstrates**: It shows a pattern where a user or front-end agent (A) cannot directly query a sensitive or proprietary database. Instead, it must route its request through a specialized, authorized component (B). This component (B) likely has the necessary credentials, API keys, or embedded logic to safely interact with the database.
* **Why it matters**: This design enhances security and control. It prevents unauthorized or unvetted LLMs from directly accessing raw data, reducing risks of data leakage, corruption, or misuse. It centralizes data access logic within component B, which can enforce validation, logging, and compliance rules.
* **Underlying Principle**: The diagram advocates for or describes a system where valuable data assets are shielded behind a dedicated access layer. The phrase "Not Accessible by other LLMs" suggests this might be a proprietary setup or a method to maintain a competitive advantage by keeping a specific dataset exclusive to one's own models. The dotted path might represent a future capability, a monitoring channel, or an administrative backdoor not used in standard operation.