## Diagram: Data Flow and Accessibility Between Components A, B, and a Stack of Disks
### Overview
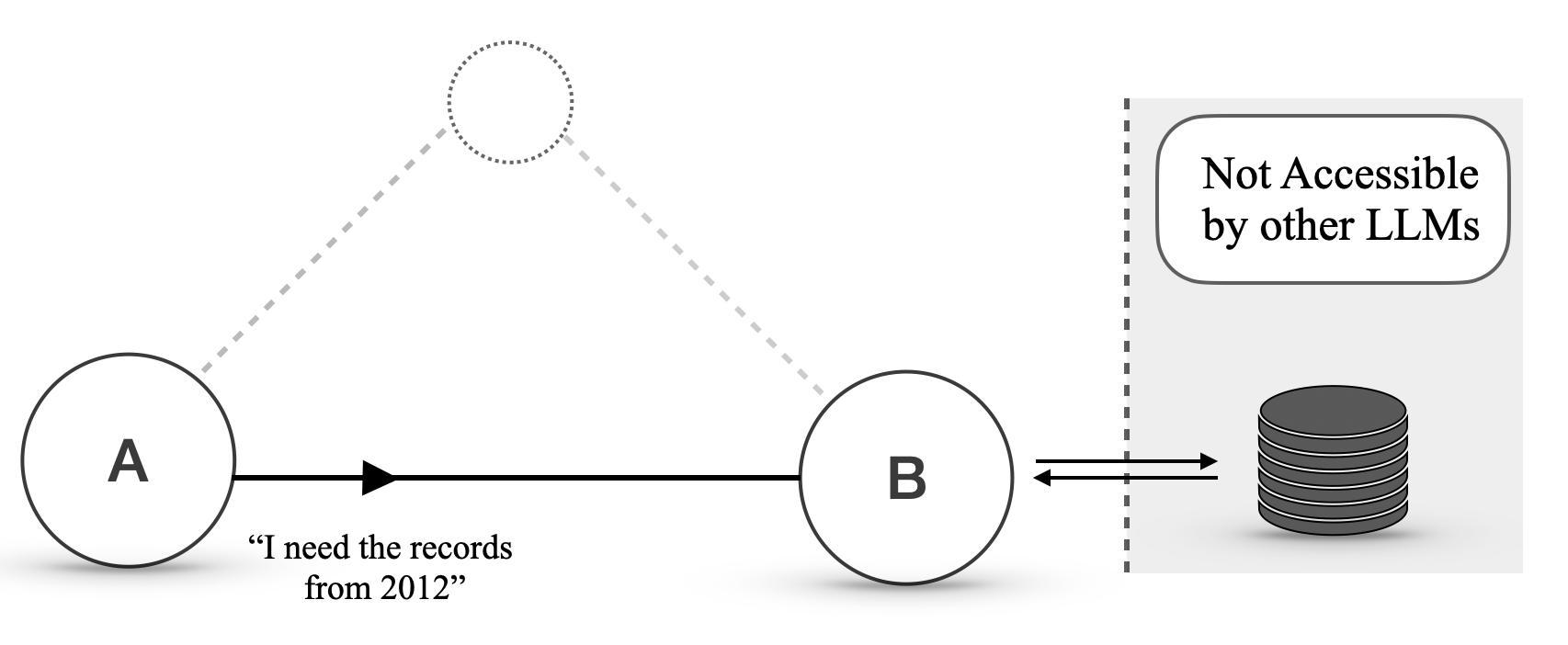
The diagram illustrates a data flow system involving three primary components:
1. **Circle A** (left) with text: *"I need the records from 2012"*.
2. **Circle B** (center-right) connected to A via a solid arrow.
3. A **stack of disks** (right) labeled *"Not Accessible by other LLMs"*.
A dotted line connects an unlabeled third circle (top-center) to both A and B, suggesting an indirect or optional relationship.
### Components/Axes
- **Circles**:
- **A**: Contains textual request for 2012 records.
- **B**: Intermediate node in the data flow.
- **Unlabeled Circle**: Connected via dotted lines to A and B.
- **Arrows**:
- Solid arrow from A → B (unidirectional flow).
- Bidirectional arrows between B and the stack of disks.
- Dotted lines from the unlabeled circle to A and B.
- **Stack of Disks**:
- Labeled *"Not Accessible by other LLMs"*.
- Positioned to the right of B, separated by a dashed vertical boundary.
### Detailed Analysis
- **Textual Content**:
- Circle A explicitly states a need for historical records ("from 2012"), implying a query or data retrieval action.
- The stack of disks is explicitly restricted in accessibility, suggesting it contains sensitive or privileged data.
- **Flow Dynamics**:
- Data flows from A to B, then interacts bidirectionally with the stack.
- The unlabeled circle’s dotted connections may represent auxiliary or conditional interactions (e.g., oversight, logging, or fallback mechanisms).
### Key Observations
1. **Access Restriction**: The stack’s label emphasizes exclusivity, implying B (and possibly A via the dotted line) has privileged access.
2. **Temporal Specificity**: A’s request for 2012 records introduces a time-bound dependency, potentially critical for the system’s purpose.
3. **Bidirectional Interaction**: B’s two-way connection to the stack suggests it acts as a mediator or gateway for the stack’s data.
### Interpretation
- **Functional Role of B**: B serves as a central hub, processing requests from A and managing interactions with the restricted stack. This positions B as a critical node for data integrity and access control.
- **Implications of Accessibility**: The stack’s restriction highlights security or compliance requirements, possibly indicating that other LLMs (Language Learning Models) lack authorization to interact with it.
- **Unlabeled Circle’s Purpose**: The dotted lines suggest the unlabeled circle may represent an external system, audit trail, or error-handling mechanism that influences A and B’s operations.
This diagram likely models a workflow where historical data retrieval (A) triggers a process (B) that interacts with a secure, isolated data repository (stack), emphasizing controlled access and temporal specificity.