\n
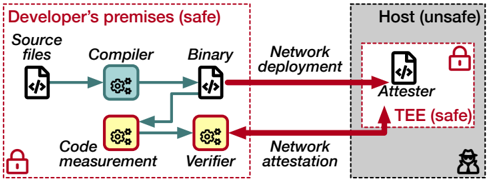
## Diagram: Secure Software Deployment Process
### Overview
This diagram illustrates a secure software deployment process, contrasting a "safe" developer's environment with an "unsafe" host environment. It depicts the flow of code from source files through compilation, verification, and deployment, highlighting security measures like code measurement, attestation, and the use of a Trusted Execution Environment (TEE). The diagram uses arrows to indicate the direction of data flow and color-coding (red, green) to represent potentially insecure and secure pathways, respectively.
### Components/Axes
The diagram is divided into two main sections:
* **Developer's premises (safe):** Enclosed in a dashed red rectangle.
* **Host (unsafe):** Enclosed in a dashed gray rectangle.
Key components within these sections include:
* **Source files:** Represented by a file icon with `< />` inside.
* **Compiler:** Represented by a light blue gear icon.
* **Binary:** Represented by a file icon with `< />` inside.
* **Code measurement:** Represented by a yellow gear icon.
* **Verifier:** Represented by a yellow gear icon.
* **Attester:** Represented by a file icon with `< />` inside.
* **TEE (safe):** Represented by a red triangle pointing upwards.
* **Network deployment:** Label indicating data transfer.
* **Network attestation:** Label indicating data transfer.
* **Lock icons:** Indicate security/trust.
* **Human icon:** Represents a user.
Arrows indicate the flow of data and processes. Red arrows represent network communication, while green arrows represent internal processes within the "safe" developer environment.
### Detailed Analysis or Content Details
The process flow is as follows:
1. **Source files** are fed into the **Compiler**, resulting in a **Binary**. This is a standard software development step.
2. The **Binary** is then sent via **Network deployment** to the **Host (unsafe)** and is received by the **Attester**.
3. The **Binary** is also sent to **Code measurement**, which then sends its output to the **Verifier**.
4. The **Verifier** sends its output via **Network attestation** to the **Host (unsafe)**.
5. The **Attester** communicates with the **TEE (safe)**.
6. The **TEE (safe)** is positioned within the **Host (unsafe)**, suggesting a secure enclave within an otherwise untrusted environment.
The diagram uses lock icons to indicate security. A lock is present at the bottom-left of the "Developer's premises (safe)" and next to the "Attester" in the "Host (unsafe)".
### Key Observations
* The diagram emphasizes the separation between a trusted development environment and an untrusted host environment.
* The use of a TEE suggests a hardware-based security mechanism to protect sensitive operations within the host.
* The network communication (red arrows) is highlighted as a potential vulnerability, requiring attestation and verification.
* The code measurement and verification steps are crucial for ensuring the integrity of the deployed binary.
* The diagram does not provide specific data or numerical values; it is a conceptual illustration of a security process.
### Interpretation
The diagram illustrates a secure remote attestation process. The developer's environment is considered safe, while the host environment is not. The process aims to ensure that the binary deployed on the host is the same as the one compiled by the developer. This is achieved through code measurement, verification, and attestation. The TEE provides a secure environment within the host to perform sensitive operations, such as verifying the attestation.
The red arrows representing network communication highlight the inherent risks of transmitting data over an untrusted network. The attestation process is designed to mitigate these risks by verifying the identity and integrity of the host before deploying the binary.
The diagram suggests a layered security approach, combining code integrity checks, secure enclaves, and network attestation to protect against malicious attacks and ensure the trustworthiness of the deployed software. The placement of the TEE within the Host suggests that it is a component that is trusted, even if the Host itself is not. The diagram is a high-level overview and does not detail the specific algorithms or protocols used for code measurement, verification, or attestation.