## Diagram: Secure Software Deployment and Attestation Flow
### Overview
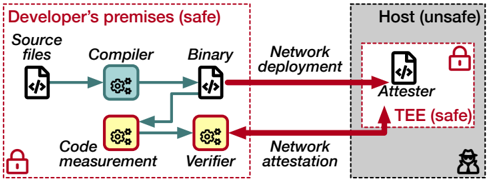
This diagram illustrates a secure software development and deployment pipeline that separates a trusted developer environment from an untrusted host environment, using a Trusted Execution Environment (TEE) for remote attestation. The process ensures that only verified, measured code runs on the host.
### Components/Axes
The diagram is divided into two primary zones:
1. **Left Zone: "Developer's premises (safe)"**
* Enclosed by a red dashed border with a red lock icon in the bottom-left corner.
* Contains the following components (from left to right):
* **Source files**: Represented by a document icon with code symbols (`</>`).
* **Compiler**: Represented by a gear icon inside a rounded square.
* **Binary**: Represented by a document icon with code symbols (`</>`).
* **Code measurement**: Represented by a gear icon inside a rounded square with a yellow background.
* **Verifier**: Represented by a gear icon inside a rounded square with a yellow background.
2. **Right Zone: "Host (unsafe)"**
* A grey box with a red dashed border.
* Contains a red lock icon in the top-right corner and a black spy/agent icon in the bottom-right corner.
* Contains one main component:
* **Attester**: Represented by a document icon with code symbols (`</>`), located within a smaller, inner box labeled **"TEE (safe)"**. This inner box has a green lock icon in its top-right corner.
**Flow Arrows & Labels:**
* **Solid Teal Arrows**: Indicate the local development and measurement flow within the safe developer premises.
* **Solid Red Arrows**: Indicate network-based interactions between the safe and unsafe zones.
* **Top Red Arrow**: Labeled **"Network deployment"**, pointing from the "Binary" (developer side) to the "Attester" (host side).
* **Bottom Red Arrow**: Labeled **"Network attestation"**, pointing from the "Attester" (host side) back to the "Verifier" (developer side).
### Detailed Analysis
The process flow is as follows:
1. **Development & Measurement (Safe Zone):**
* **Source files** are fed into the **Compiler**.
* The **Compiler** produces a **Binary**.
* A parallel process performs **Code measurement** on the binary or related artifacts.
* The output of the **Code measurement** is sent to the **Verifier**.
2. **Deployment & Attestation (Cross-Zone):**
* The **Binary** is sent via **Network deployment** to the **Attester** running on the untrusted **Host**.
* The **Attester** operates within a **TEE (safe)**, a hardware-isolated secure environment on the host.
* The **Attester** generates a cryptographic attestation (proof of its state and the code it's running) and sends it back via **Network attestation** to the **Verifier** on the developer's premises.
3. **Verification Loop:**
* The **Verifier** compares the received attestation from the host's TEE against the original **Code measurement** taken during development.
* This creates a closed loop of trust: the developer can verify that the exact, unaltered binary they compiled is running securely inside the TEE on the remote, untrusted host.
### Key Observations
* **Trust Boundary**: The diagram explicitly marks the developer's premises as "safe" and the host as "unsafe," with the TEE being a "safe" enclave within the unsafe host.
* **Security Indicators**: Lock icons (red for overall zones, green for the TEE) and a spy icon visually reinforce the security context.
* **Asymmetric Flow**: Deployment is a one-way push (binary to host), while attestation is a return communication (proof back to verifier).
* **Component Isolation**: The "Code measurement" and "Verifier" are distinct from the "Compiler," emphasizing that verification is a separate, critical step.
### Interpretation
This diagram depicts a **Remote Attestation** protocol, a cornerstone of confidential computing and zero-trust architectures. Its purpose is to solve the problem of trusting software running on a remote machine you do not physically control or fully trust.
* **How it works**: The system establishes a hardware-rooted chain of trust. The TEE on the host can cryptographically prove its identity and the integrity of the code it is executing. The developer's verifier holds the "ground truth" (the measurement of the code they built) and checks the remote proof against it.
* **Why it matters**: This allows sensitive workloads to be deployed on potentially compromised or multi-tenant infrastructure (like public clouds) while maintaining strong security guarantees. The "unsafe" host operator cannot tamper with the code running in the TEE without detection.
* **Underlying Principle**: The model shifts trust from the host operator to the hardware (the TEE) and the cryptographic verification process. The red "spy" icon on the host underscores that the threat model includes a malicious host administrator. The entire flow ensures that despite this threat, the integrity of the deployed binary can be verified remotely.