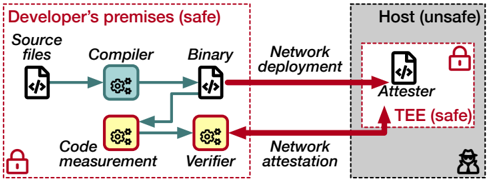
## Flowchart: Secure Software Deployment Process
### Overview
The diagram illustrates a secure software deployment workflow between a developer's premises (safe environment) and an untrusted host. It emphasizes code integrity verification through cryptographic attestation and trusted execution environments (TEE). The process involves multiple security checks, including code measurement, verification, and network attestation, to ensure safe deployment to an unsafe host.
### Components/Axes
1. **Developer's Premises (Safe)**
- Source files (icon: document with code)
- Compiler (gear icon)
- Binary (document icon)
- Code measurement (gear icon)
- Verifier (gear icon)
- Lock icon (security emphasis)
2. **Host (Unsafe)**
- Attester (document icon)
- TEE (lock icon)
- Briefcase with lock icon (data security)
3. **Network Elements**
- Network deployment (red arrow)
- Network attestation (red arrow)
4. **Flow Arrows**
- Green arrows: Internal development process
- Red arrows: Network transmission between environments
### Detailed Analysis
- **Development Flow**:
- Source files → Compiler → Binary (green arrow)
- Binary undergoes Code measurement and Verification (yellow components)
- **Deployment Flow**:
- Verified binary → Network deployment (red arrow) → Host
- Host contains Attester and TEE components
- Network attestation (red arrow) connects Verifier to Attester
- **Security Markers**:
- Lock icons on Developer's premises and TEE
- Briefcase with lock icon on Host (data protection)
- Red dashed borders demarcate safe/unsafe zones
### Key Observations
1. **Environment Segmentation**:
- Clear physical separation between safe (Developer) and unsafe (Host) environments
- Red dashed borders visually reinforce security boundaries
2. **Verification Process**:
- Code measurement and Verifier act as gatekeepers before network deployment
- Attestation occurs post-deployment to validate execution environment
3. **Cryptographic Elements**:
- Multiple lock icons indicate cryptographic protection at multiple stages
- TEE (Trusted Execution Environment) explicitly marked as safe component
### Interpretation
This diagram demonstrates a defense-in-depth approach to secure software deployment:
1. **Pre-Deployment Security**:
- Code is compiled and verified locally before leaving the developer's premises
- Code measurement creates cryptographic proofs of integrity
2. **Network Security**:
- Red arrows indicate potential attack surfaces during transmission
- Network attestation ensures remote verification of deployed code
3. **Host Security**:
- TEE provides a secure execution environment despite the host being generally unsafe
- Attester validates the integrity of the execution environment
The process reflects modern secure development practices combining:
- Local code verification
- Remote attestation
- Hardware-enforced secure execution contexts
- Network security controls
Notably absent are quantitative metrics, suggesting this is a conceptual rather than statistical representation of secure deployment workflows.