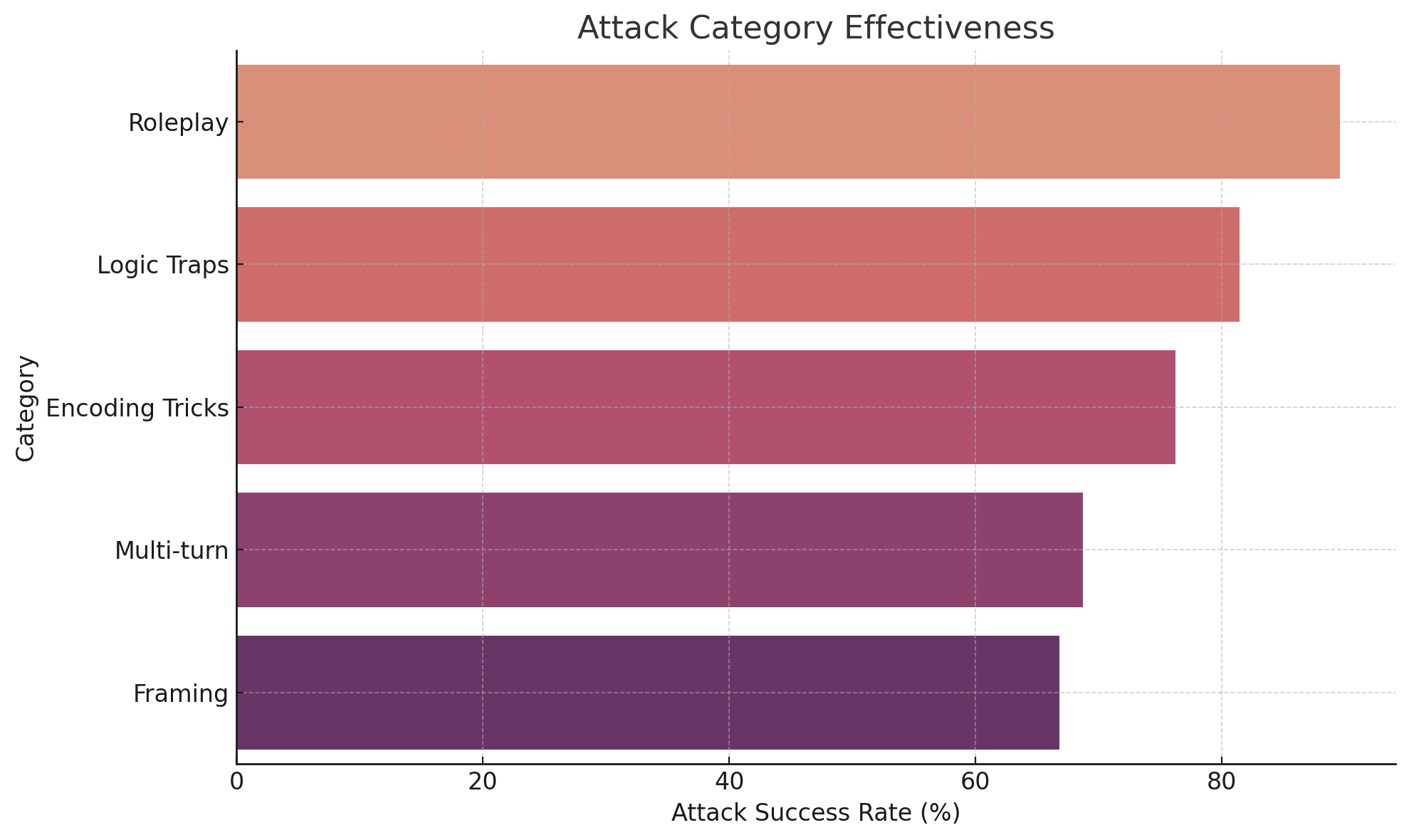
## Horizontal Bar Chart: Attack Category Effectiveness
### Overview
This image is a horizontal bar chart titled "Attack Category Effectiveness." It visually compares the success rates of five distinct categories of attacks, presumably against some system or model. The chart uses a color gradient from light to dark to distinguish the categories, with longer bars indicating higher effectiveness.
### Components/Axes
* **Chart Title:** "Attack Category Effectiveness" (centered at the top).
* **Y-Axis (Vertical):** Labeled "Category." It lists five categorical variables from top to bottom:
1. Roleplay
2. Logic Traps
3. Encoding Tricks
4. Multi-turn
5. Framing
* **X-Axis (Horizontal):** Labeled "Attack Success Rate (%)". The axis has numerical markers at 0, 20, 40, 60, and 80. The scale appears linear.
* **Data Series:** Five horizontal bars, each corresponding to a category on the Y-axis. The bars are colored with a gradient:
* Roleplay: Light salmon/peach color.
* Logic Traps: Medium reddish-brown.
* Encoding Tricks: Darker mauve.
* Multi-turn: Dark purple.
* Framing: Darkest purple/indigo.
* **Grid:** Light, dashed vertical grid lines extend from the x-axis markers (20, 40, 60, 80) to aid in reading values.
### Detailed Analysis
The chart presents the following approximate "Attack Success Rate (%)" values for each category, determined by visually aligning the end of each bar with the x-axis scale:
1. **Roleplay (Top bar, light salmon):** The bar extends past the 80% mark. **Approximate Value: 88%** (Uncertainty: ±2%).
2. **Logic Traps (Second bar, reddish-brown):** The bar extends just past the 80% mark. **Approximate Value: 81%** (Uncertainty: ±1%).
3. **Encoding Tricks (Third bar, mauve):** The bar ends between the 60% and 80% grid lines, closer to 80%. **Approximate Value: 76%** (Uncertainty: ±2%).
4. **Multi-turn (Fourth bar, dark purple):** The bar ends between the 60% and 80% grid lines, closer to 60%. **Approximate Value: 68%** (Uncertainty: ±2%).
5. **Framing (Bottom bar, darkest purple):** The bar ends just past the 60% grid line. **Approximate Value: 66%** (Uncertainty: ±2%).
**Trend Verification:** The visual trend is a clear, stepwise decrease in bar length from top to bottom. The "Roleplay" bar is the longest, and the "Framing" bar is the shortest, confirming a descending order of effectiveness.
### Key Observations
* **Highest Effectiveness:** "Roleplay" is the most effective attack category by a significant margin, with a success rate approaching 90%.
* **Lowest Effectiveness:** "Framing" is the least effective among the shown categories, with a success rate in the mid-60s.
* **Color Gradient:** The chart employs a deliberate color gradient where lighter, warmer colors correspond to higher success rates, and darker, cooler colors correspond to lower success rates. This provides a secondary visual cue for the ranking.
* **Clustering:** "Logic Traps" and "Encoding Tricks" form a middle tier with success rates in the 70s. "Multi-turn" and "Framing" form a lower tier with success rates in the 60s.
* **No Zero Baseline Issue:** The x-axis correctly starts at 0, allowing for an accurate visual comparison of the bar lengths.
### Interpretation
This chart demonstrates a clear hierarchy in the effectiveness of different adversarial attack strategies. The data suggests that attacks based on **"Roleplay"**—likely involving the model adopting a specific persona or scenario to bypass safety guidelines—are currently the most potent threat vector, succeeding nearly 9 times out of 10.
The significant drop-off to the next category ("Logic Traps") indicates that while logical paradoxes or constrained scenarios are effective, they are less reliable than narrative-based manipulation. The lower effectiveness of "Multi-turn" attacks is noteworthy, as it suggests that prolonged, conversational attacks may be less successful than well-crafted single prompts, possibly due to model safeguards that activate over longer interactions.
The color gradient reinforces the narrative: the "hotter" (lighter) the attack category, the more "effective" it is. From a security perspective, this chart prioritizes where defensive efforts should be focused. Mitigating roleplay-based vulnerabilities would yield the greatest improvement in overall system robustness. The chart does not provide context on the target system, the sample size, or the timeframe of the tests, which are critical for a full assessment.