## Sequence Diagram: ProverTEE and VerifyTEE Interaction
### Overview
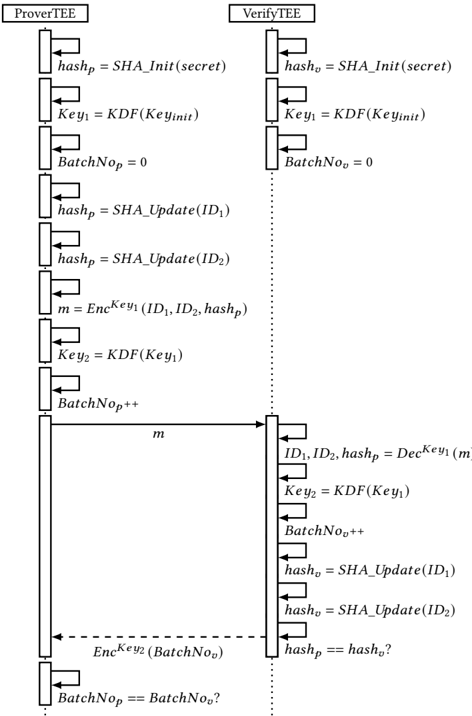
The image is a sequence diagram illustrating the interaction between two entities, ProverTEE and VerifyTEE. It outlines the steps involved in a process that includes initialization, hashing, encryption, decryption, and verification.
### Components/Axes
* **Entities:**
* ProverTEE (left side)
* VerifyTEE (right side)
* **Messages:** Arrows indicate the flow of information between the entities.
* **Operations:** Text labels describe the operations performed by each entity.
### Detailed Analysis
The diagram describes the following sequence of operations:
1. **Initialization:**
* ProverTEE initializes `hashp` with `SHA_Init(secret)`.
* ProverTEE derives `Key1` using `KDF(Keyinit)`.
* ProverTEE sets `BatchNop = 0`.
* VerifyTEE initializes `hashv` with `SHA_Init(secret)`.
* VerifyTEE derives `Key1` using `KDF(Keyinit)`.
* VerifyTEE sets `BatchNov = 0`.
2. **Hashing and Encryption (ProverTEE):**
* ProverTEE updates `hashp` with `SHA_Update(ID1)`.
* ProverTEE updates `hashp` with `SHA_Update(ID2)`.
* ProverTEE encrypts `ID1`, `ID2`, and `hashp` using `Key1` to produce `m`: `m = EncKey1(ID1, ID2, hashp)`.
* ProverTEE derives `Key2` using `KDF(Key1)`.
* ProverTEE increments `BatchNop`.
3. **Message Transmission:**
* ProverTEE sends the encrypted message `m` to VerifyTEE.
4. **Decryption and Verification (VerifyTEE):**
* VerifyTEE decrypts `m` using `Key1` to obtain `ID1`, `ID2`, and `hashp`: `ID1, ID2, hashp = DecKey1(m)`.
* VerifyTEE derives `Key2` using `KDF(Key1)`.
* VerifyTEE increments `BatchNov`.
* VerifyTEE updates `hashv` with `SHA_Update(ID1)`.
* VerifyTEE updates `hashv` with `SHA_Update(ID2)`.
* VerifyTEE encrypts `BatchNov` using `Key2` and sends it back to ProverTEE: `EncKey2(BatchNov)`.
* VerifyTEE checks if `hashp == hashv`.
5. **Final Verification (ProverTEE):**
* ProverTEE checks if `BatchNop == BatchNov`.
### Key Observations
* The diagram illustrates a secure communication protocol between two trusted execution environments (TEEs).
* Hashing, encryption, and decryption are used to ensure data integrity and confidentiality.
* Batch numbers are used to maintain synchronization between the two entities.
### Interpretation
The sequence diagram depicts a process where ProverTEE sends data to VerifyTEE in a secure manner. The use of hashing and encryption ensures that the data is not tampered with during transmission and that only the intended recipient can access it. The batch numbers help to ensure that the two entities are in sync and that no messages are lost or duplicated. The final verification steps confirm the integrity of the process.