\n
## Diagram: Secure Multi-Party Computation Protocol Flow
### Overview
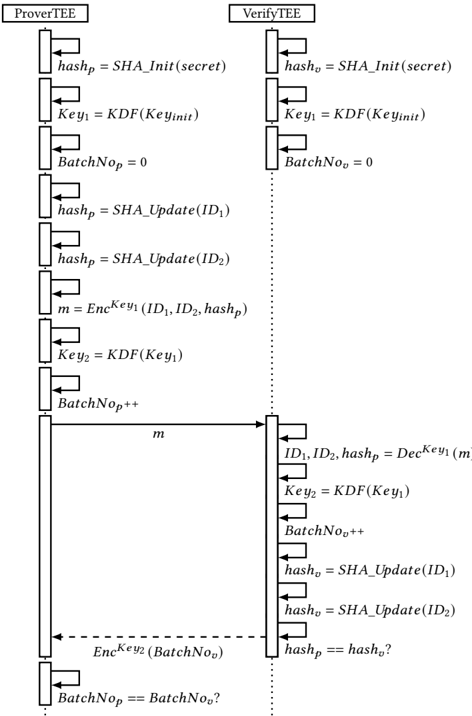
The image depicts a sequence diagram illustrating a secure multi-party computation protocol between two entities: a "ProverTEE" and a "VerifyTEE". The diagram shows the flow of messages and operations performed by each entity to verify a batch of data. The diagram uses boxes to represent operations and arrows to represent message passing.
### Components/Axes
The diagram consists of two vertical columns representing the "ProverTEE" (left) and "VerifyTEE" (right). Each column contains a series of rectangular boxes representing operations, connected by arrows indicating the flow of data or control. The diagram also includes dashed arrows to indicate conditional operations.
### Detailed Analysis or Content Details
**ProverTEE (Left Column):**
1. `hashp = SHA_Init(secret)`
2. `Key1 = KDF(Keyinit)`
3. `BatchNop = 0`
4. `hashp = SHA_Update(ID1)`
5. `hashp = SHA_Update(ID2)`
6. `m = EncKey1(ID1, ID2, hashp)`
7. `Key2 = KDF(Key1)`
8. `BatchNop++`
9. Message `m` is sent to VerifyTEE.
10. `EncKey2(BatchNop)` is sent to VerifyTEE (dashed arrow, conditional).
11. `BatchNop == BatchNo?` (conditional, end of flow)
**VerifyTEE (Right Column):**
1. `hasho = SHA_Init(secret)`
2. `Key1 = KDF(Keyinit)`
3. `BatchNoo = 0`
4. `hasho = SHA_Update(ID1)`
5. `hasho = SHA_Update(ID2)`
6. Message `m` is received from ProverTEE.
7. `ID1, ID2, hashp = DecKey1(m)`
8. `Key2 = KDF(Key1)`
9. `BatchNoo++`
10. `hasho = SHA_Update(ID1)`
11. `hasho = SHA_Update(ID2)`
12. `hashp == hasho?` (conditional)
**Variables and Functions:**
* `hashp`, `hasho`: Hash values.
* `Key1`, `Key2`: Keys derived using a Key Derivation Function (KDF).
* `BatchNop`, `BatchNoo`: Batch numbers.
* `ID1`, `ID2`: Identifiers.
* `m`: Encrypted message.
* `SHA_Init(secret)`: Initializes a SHA hash with a secret.
* `KDF(Keyinit)`: Key Derivation Function.
* `SHA_Update(ID)`: Updates the SHA hash with an identifier.
* `EncKey1(ID1, ID2, hashp)`: Encrypts data using Key1.
* `DecKey1(m)`: Decrypts data using Key1.
* `EncKey2(BatchNop)`: Encrypts the batch number using Key2.
### Key Observations
The diagram illustrates a protocol where the ProverTEE proves the correctness of a batch of data (represented by `ID1` and `ID2`) to the VerifyTEE. The protocol uses encryption, hashing, and key derivation to ensure security and integrity. The conditional checks (`BatchNop == BatchNo?` and `hashp == hasho?`) are crucial for verifying the batch and the hash values. The use of `SHA_Update` suggests that the hash is being incrementally built.
### Interpretation
This diagram represents a secure computation protocol likely used in a Trusted Execution Environment (TEE) setting, as indicated by the "TEE" suffix in the entity names. The protocol aims to verify data integrity and authenticity. The ProverTEE generates a proof (`m`) based on the data and a secret, and the VerifyTEE verifies this proof. The use of KDFs ensures that keys are derived securely from initial secrets. The batch numbers (`BatchNop` and `BatchNoo`) suggest that the protocol can handle multiple data items in a batch. The conditional checks at the end ensure that the batch number and hash values match, confirming the validity of the proof. The dashed arrow indicates a conditional message exchange, likely triggered by a successful verification. The protocol appears to be designed to prevent the VerifyTEE from learning the secret used by the ProverTEE, while still allowing it to verify the data's integrity. The use of SHA hashing provides collision resistance and ensures data integrity. The overall design suggests a commitment-and-verification scheme.