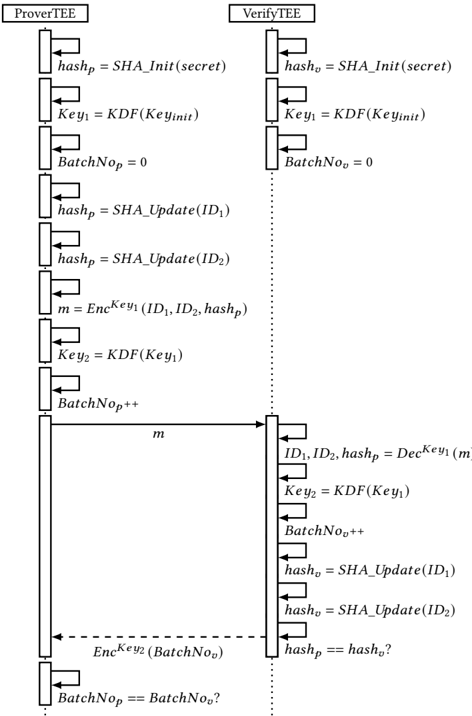
## Flowchart: Secure Communication Protocol (ProveTee & VerifyTee)
### Overview
The diagram illustrates a cryptographic protocol for secure communication between a prover (ProveTee) and a verifier (VerifyTee). It involves hash generation, key derivation, encryption/decryption, and batch number synchronization to ensure data integrity and authenticity.
### Components/Axes
- **Sections**:
- **ProveTee**: Left-side process for generating cryptographic proofs.
- **VerifyTee**: Right-side process for validating proofs.
- **Key Variables**:
- `hash_p`, `hash_v`: Hash values for prover and verifier.
- `Key1`, `Key2`: Derived keys for encryption/decryption.
- `BatchNo_p`, `BatchNo_v`: Batch numbers for synchronization.
- **Functions**:
- `SHA_Init(secret)`: Initializes a hash with a secret.
- `KDF(Key_init)`: Key derivation function.
- `SHA_Update(ID)`: Updates hash with identity data.
- `Enc^Key1(...)`: Encryption using Key1.
- `Dec^Key1(...)`: Decryption using Key1.
### Detailed Analysis
1. **ProveTee Workflow**:
- `hash_p = SHA_Init(secret)`: Initializes hash with a secret.
- `Key1 = KDF(Key_init)`: Derives Key1 from Key_init.
- `BatchNo_p = 0`: Initializes batch number.
- `hash_p = SHA_Update(ID1)`: Updates hash with ID1.
- `hash_p = SHA_Update(ID2)`: Updates hash with ID2.
- `m = Enc^Key1(ID1, ID2, hash_p)`: Encrypts data with Key1.
- `Key2 = KDF(Key1)`: Derives Key2 from Key1.
- `BatchNo_p++`: Increments batch number.
2. **VerifyTee Workflow**:
- `hash_v = SHA_Init(secret)`: Initializes hash with the same secret.
- `Key1 = KDF(Key_init)`: Derives Key1 (same as ProveTee).
- `BatchNo_v = 0`: Initializes batch number.
- `hash_v = SHA_Update(ID1)`: Updates hash with ID1.
- `hash_v = SHA_Update(ID2)`: Updates hash with ID2.
- `ID1, ID2, hash_p = Dec^Key1(m)`: Decrypts received data.
- `Key2 = KDF(Key1)`: Derives Key2 (same as ProveTee).
- `BatchNo_v++`: Increments batch number.
- `hash_p == hash_v?`: Compares hashes for integrity.
- `BatchNo_p == BatchNo_v?`: Validates batch synchronization.
### Key Observations
- **Synchronization**: Batch numbers (`BatchNo_p`, `BatchNo_v`) ensure both parties process data in the same order.
- **Cryptographic Integrity**: SHA hashing and KDF ensure data authenticity and key security.
- **Encryption**: Data (`m`) is encrypted with Key1 to prevent tampering.
- **Validation**: VerifyTee checks hash equality and batch number consistency to confirm validity.
### Interpretation
This protocol ensures secure communication by:
1. **Binding Data to Identity**: SHA updates with `ID1` and `ID2` tie the hash to specific identities.
2. **Key Management**: KDF derives keys hierarchically, reducing exposure of the master key.
3. **Tamper Detection**: Hash comparison (`hash_p == hash_v?`) detects unauthorized modifications.
4. **Replay Protection**: Batch numbers prevent reuse of old data.
The protocol assumes both parties share `secret` and `Key_init`, enabling secure collaboration without exposing sensitive data. The dashed line between ProveTee and VerifyTee indicates conditional validation, where VerifyTee only proceeds if hashes and batch numbers match.