## Cryptographic Reduction Diagram: RLWE to DRLWE Reduction Chain
### Overview
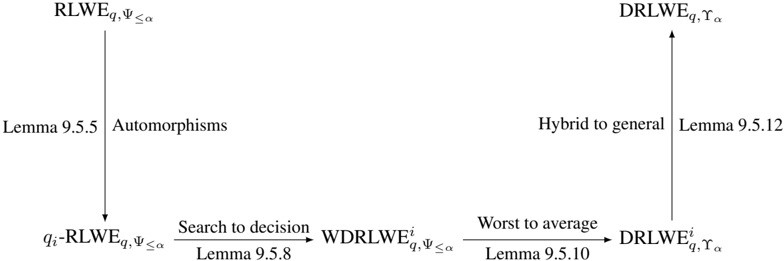
The image displays a formal cryptographic reduction diagram, illustrating a chain of theoretical reductions between variants of the Ring Learning With Errors (RLWE) problem. It maps the logical steps from a search-type RLWE problem to a decision-type Distributed RLWE (DRLWE) problem, with each transformation justified by a cited lemma. The diagram is a flowchart of implications, not a data chart.
### Components/Axes
The diagram consists of five text-based nodes representing cryptographic problems, connected by four directional arrows representing reductions or transformations. Each arrow is annotated with the type of reduction and a lemma reference.
**Nodes (Problems):**
1. **Top-Left:** `RLWE_{q, Ψ≤α}`
2. **Bottom-Left:** `q_i-RLWE_{q, Ψ≤α}`
3. **Bottom-Center:** `WDRLWE^i_{q, Ψ≤α}`
4. **Bottom-Right:** `DRLWE^i_{q, γ_α}`
5. **Top-Right:** `DRLWE_{q, γ_α}`
**Arrows (Reductions):**
1. **Vertical Downward Arrow (Left):** From `RLWE_{q, Ψ≤α}` to `q_i-RLWE_{q, Ψ≤α}`.
* **Annotation (Left of arrow):** `Lemma 9.5.5`
* **Annotation (Right of arrow):** `Automorphisms`
2. **Horizontal Rightward Arrow (Bottom-Left):** From `q_i-RLWE_{q, Ψ≤α}` to `WDRLWE^i_{q, Ψ≤α}`.
* **Annotation (Above arrow):** `Search to decision`
* **Annotation (Below arrow):** `Lemma 9.5.8`
3. **Horizontal Rightward Arrow (Bottom-Right):** From `WDRLWE^i_{q, Ψ≤α}` to `DRLWE^i_{q, γ_α}`.
* **Annotation (Above arrow):** `Worst to average`
* **Annotation (Below arrow):** `Lemma 9.5.10`
4. **Vertical Upward Arrow (Right):** From `DRLWE^i_{q, γ_α}` to `DRLWE_{q, γ_α}`.
* **Annotation (Left of arrow):** `Hybrid to general`
* **Annotation (Right of arrow):** `Lemma 9.5.12`
### Detailed Analysis
The diagram outlines a specific proof strategy in lattice-based cryptography:
1. **Starting Point:** The chain begins with the standard search variant of RLWE (`RLWE_{q, Ψ≤α}`), defined over a ring with modulus `q` and error distribution `Ψ` bounded by parameter `α`.
2. **First Reduction (Automorphisms):** Using properties of automorphisms (Lemma 9.5.5), the problem is reduced to a "quotient" or indexed version, `q_i-RLWE_{q, Ψ≤α}`.
3. **Second Reduction (Search to Decision):** A standard cryptographic technique (Lemma 9.5.8) transforms the search problem into its corresponding decisional problem, `WDRLWE^i_{q, Ψ≤α}`. The "W" likely denotes a "worst-case" or specific variant.
4. **Third Reduction (Worst to Average):** Lemma 9.5.10 facilitates a shift from a worst-case hardness assumption to an average-case one, resulting in `DRLWE^i_{q, γ_α}`. Note the parameter changes from `α` to `γ_α`, indicating a potential change in the error bound or distribution parameter for the decisional problem.
5. **Final Reduction (Hybrid to General):** The last step (Lemma 9.5.12) generalizes from an indexed or hybrid version (`^i`) of the Distributed RLWE problem to the general `DRLWE_{q, γ_α}` problem.
### Key Observations
* **Directional Flow:** The reduction path is not linear. It moves down, then right twice, then up, forming a "U" shape or a hook. This visually separates the initial transformations (left side) from the final generalization (right side).
* **Parameter Evolution:** The error parameter evolves from `α` in the first three nodes to `γ_α` in the final two nodes, suggesting the reductions may involve a tightening or redefinition of the noise bound.
* **Problem Type Shift:** The chain explicitly shows the transition from a **search** problem (`RLWE`, `q_i-RLWE`) to a **decisional** problem (`WDRLWE`, `DRLWE`), which is a fundamental step in many cryptographic security proofs.
* **Lemma Citations:** Each step is rigorously justified by a specific lemma number (9.5.5, 9.5.8, 9.5.10, 9.5.12), indicating this diagram is part of a larger, structured academic text (likely a thesis or research paper).
### Interpretation
This diagram is a **proof roadmap**. It does not present empirical data but rather the logical structure of a theoretical argument in cryptography.
* **What it Demonstrates:** It shows that if one can solve the general Distributed RLWE (`DRLWE`) problem, then—by reversing the arrows—one could solve the foundational Ring Learning With Errors (`RLWE`) problem. This establishes that `DRLWE` is at least as hard as `RLWE`, providing a security foundation for cryptographic protocols based on `DRLWE`.
* **Relationships:** The arrows represent "reductions." In complexity theory, a reduction from Problem A to Problem B means that an efficient solver for B could be used to solve A. Therefore, the diagram asserts: `RLWE ≤ q_i-RLWE ≤ WDRLWE^i ≤ DRLWE^i ≤ DRLWE`. The hardness propagates from the bottom-left to the top-right.
* **Significance:** Such reduction chains are the bedrock of modern provable security. They allow cryptographers to base the security of new, potentially more efficient or functional primitives (like distributed or functional encryption schemes built on `DRLWE`) on well-studied, hard problems (`RLWE`). The specific techniques cited (Automorphisms, Search-to-Decision, Worst-to-Average, Hybrid Arguments) are standard tools in the lattice cryptography toolkit.
* **Notable Structure:** The separation of the "Hybrid to general" step as a final, upward move highlights that generalizing from a restricted (indexed/hybrid) setting to the full problem is a distinct and significant step in the proof, often requiring its own lemma.