## Horizontal Bar Chart: Attack Types vs. RtA Score
### Overview
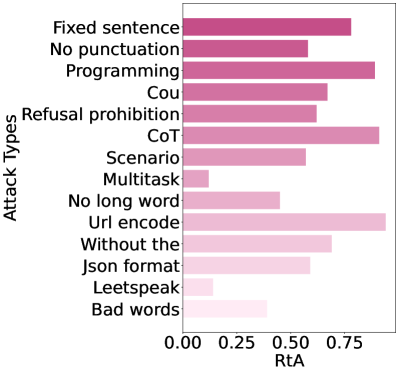
This image is a horizontal bar chart displaying the performance or effectiveness of various "Attack Types" measured by a metric called "RtA" (likely an acronym for a specific evaluation metric, such as "Rate of Attack Success" or similar). The chart compares 13 distinct attack categories. The bars are colored in a gradient from dark pink (higher RtA) to very light pink (lower RtA), visually reinforcing the numerical value.
### Components/Axes
* **Chart Type:** Horizontal Bar Chart.
* **Y-Axis (Vertical):** Labeled **"Attack Types"**. It lists 13 categorical items. From top to bottom:
1. Fixed sentence
2. No punctuation
3. Programming
4. Cou (Note: This label appears truncated. It may stand for "Counterfactual" or another term.)
5. Refusal prohibition
6. CoT (Note: Commonly stands for "Chain-of-Thought")
7. Scenario
8. Multitask
9. No long word
10. Url encode
11. Without the
12. Json format
13. Leetspeak
14. Bad words
* **X-Axis (Horizontal):** Labeled **"RtA"**. It is a linear numerical scale with major tick marks at **0.00, 0.25, 0.50, and 0.75**. The axis extends slightly beyond 0.75.
* **Legend/Color Key:** There is no separate legend box. The color of each bar is directly tied to its value, using a sequential pink color scale where darker shades correspond to higher RtA values.
### Detailed Analysis
Below is an analysis of each data series (attack type), including its visual trend (bar length) and the approximate RtA value extracted by aligning the end of the bar with the x-axis scale.
1. **Fixed sentence:** Bar extends to approximately **0.78**. (Trend: Long bar, high value).
2. **No punctuation:** Bar extends to approximately **0.58**. (Trend: Medium-length bar).
3. **Programming:** Bar extends to approximately **0.88**. (Trend: Very long bar, one of the highest values).
4. **Cou:** Bar extends to approximately **0.68**. (Trend: Medium-long bar).
5. **Refusal prohibition:** Bar extends to approximately **0.60**. (Trend: Medium-length bar).
6. **CoT:** Bar extends to approximately **0.88**. (Trend: Very long bar, appears tied with "Programming" for the highest value).
7. **Scenario:** Bar extends to approximately **0.58**. (Trend: Medium-length bar, similar to "No punctuation").
8. **Multitask:** Bar extends to approximately **0.12**. (Trend: Very short bar, one of the lowest values).
9. **No long word:** Bar extends to approximately **0.48**. (Trend: Medium-short bar).
10. **Url encode:** Bar extends to approximately **0.92**. (Trend: The longest bar, indicating the highest RtA value on the chart).
11. **Without the:** Bar extends to approximately **0.70**. (Trend: Medium-long bar).
12. **Json format:** Bar extends to approximately **0.60**. (Trend: Medium-length bar, similar to "Refusal prohibition").
13. **Leetspeak:** Bar extends to approximately **0.15**. (Trend: Very short bar, similar to "Multitask").
14. **Bad words:** Bar extends to approximately **0.40**. (Trend: Short bar).
### Key Observations
* **Highest Effectiveness:** "Url encode" has the highest RtA (~0.92), followed closely by "Programming" and "CoT" (both ~0.88). This suggests these methods are the most successful according to this metric.
* **Lowest Effectiveness:** "Multitask" (~0.12) and "Leetspeak" (~0.15) have the lowest scores, indicating they are the least effective attack types in this evaluation.
* **Clustering:** Several attack types cluster in the middle range (0.55 - 0.70), including "Fixed sentence," "Cou," "Refusal prohibition," "Scenario," "Without the," and "Json format."
* **Visual Encoding:** The color gradient effectively reinforces the data, with the longest bars ("Url encode," "Programming," "CoT") being the darkest pink and the shortest bars ("Multitask," "Leetspeak") being the lightest pink.
* **Label Ambiguity:** The label "Cou" is truncated and its full meaning is unclear from the image alone.
### Interpretation
This chart provides a comparative analysis of different adversarial or testing techniques ("Attack Types") against a system, quantified by the "RtA" score. The data suggests a significant variance in the effectiveness of these techniques.
* **Technical & Encoding-Based Attacks are Highly Effective:** The top-performing methods—"Url encode," "Programming," and "CoT" (Chain-of-Thought)—are all related to technical formatting, code, or structured reasoning prompts. This implies that attacks leveraging the system's own processing of code, encoded data, or logical chains are particularly potent.
* **Simple Linguistic Modifications are Less Effective:** Attacks based on simpler linguistic changes, such as using "Bad words," "Leetspeak," or imposing constraints like "No long word," show markedly lower success rates. The "Multitask" attack is notably ineffective.
* **Implication for Robustness:** The results highlight potential vulnerabilities in systems when processing technically formatted inputs or complex reasoning prompts. Conversely, the system appears more robust against straightforward lexical or stylistic manipulations. The high score for "Url encode" is particularly notable, suggesting that obfuscation through standard encoding schemes is a major attack vector.
* **Investigative Note:** The near-identical high scores for "Programming" and "CoT" might indicate a correlation or overlap in how these attack types are constructed or evaluated. Further investigation would be needed to understand the relationship between these categories. The truncated label "Cou" also requires clarification for a complete understanding.