## Horizontal Bar Chart: Attack Type vs. RtA
### Overview
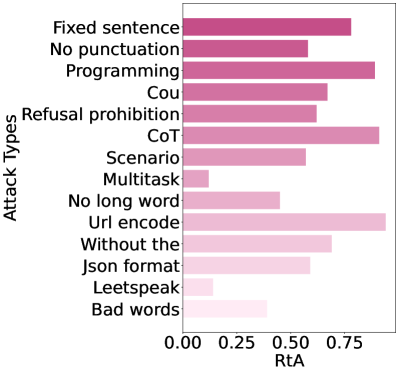
The image is a horizontal bar chart comparing different attack types based on their RtA (likely representing some kind of success rate or effectiveness). The y-axis lists the attack types, and the x-axis represents the RtA value, ranging from 0.00 to 0.75. The bars are colored in shades of pink, with darker shades indicating higher RtA values.
### Components/Axes
* **Y-axis (Vertical):** "Attack Types"
* Categories (from top to bottom): Fixed sentence, No punctuation, Programming, Cou, Refusal prohibition, CoT, Scenario, Multitask, No long word, Url encode, Without the, Json format, Leetspeak, Bad words
* **X-axis (Horizontal):** "RtA"
* Scale: 0.00, 0.25, 0.50, 0.75
### Detailed Analysis
Here's a breakdown of the RtA values for each attack type, along with the trend for each bar:
* **Fixed sentence:** RtA ≈ 0.78.
* **No punctuation:** RtA ≈ 0.68.
* **Programming:** RtA ≈ 0.79.
* **Cou:** RtA ≈ 0.65.
* **Refusal prohibition:** RtA ≈ 0.60.
* **CoT:** RtA ≈ 0.82.
* **Scenario:** RtA ≈ 0.58.
* **Multitask:** RtA ≈ 0.15.
* **No long word:** RtA ≈ 0.48.
* **Url encode:** RtA ≈ 0.85.
* **Without the:** RtA ≈ 0.65.
* **Json format:** RtA ≈ 0.55.
* **Leetspeak:** RtA ≈ 0.12.
* **Bad words:** RtA ≈ 0.30.
### Key Observations
* The "Url encode" attack type has the highest RtA value, followed closely by "CoT" and "Programming".
* "Multitask" and "Leetspeak" attack types have the lowest RtA values.
* There is a significant range in RtA values across the different attack types, indicating varying degrees of effectiveness.
### Interpretation
The chart suggests that certain attack types are more effective than others, as measured by the RtA metric. "Url encode", "CoT", and "Programming" attacks appear to be particularly successful, while "Multitask" and "Leetspeak" attacks are less so. This information could be valuable for understanding the strengths and weaknesses of different attack strategies and for developing more robust defense mechanisms. The variation in RtA values highlights the importance of considering a diverse range of attack types when evaluating system security.