## Code Snippet: Assembly Instructions
### Overview
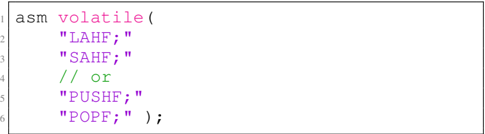
The image presents a code snippet, likely C or C++, embedding assembly instructions. The assembly code appears to involve stack manipulation and flag register operations.
### Components/Axes
The code snippet consists of the following elements:
* **asm volatile ( ... );**: This construct indicates an inline assembly block, marked as volatile to prevent compiler optimizations.
* **"LAHF;"**: Assembly instruction to Load AH from Flags.
* **"SAHF;"**: Assembly instruction to Store AH into Flags.
* **"PUSHF;"**: Assembly instruction to push flags onto the stack.
* **"POPF;"**: Assembly instruction to pop flags from the stack.
* **// or**: A comment indicating an alternative instruction sequence.
### Detailed Analysis or Content Details
The code snippet contains the following lines:
1. `asm volatile (`
2. `"LAHF;"`
3. `"SAHF;"`
4. `// or`
5. `"PUSHF;"`
6. `"POPF;" );`
The assembly instructions are enclosed in double quotes, indicating they are string literals passed to the `asm` statement. The `volatile` keyword ensures that the compiler does not optimize away the assembly code.
### Key Observations
The code snippet presents two alternative ways to achieve a similar outcome:
1. Using `LAHF` and `SAHF` to manipulate the AH register and then transfer it to the flags register.
2. Using `PUSHF` and `POPF` to directly push and pop the flags register from the stack.
### Interpretation
The code snippet demonstrates how to embed assembly instructions within C/C++ code. The `LAHF` and `SAHF` instructions are older methods for manipulating the flags register, while `PUSHF` and `POPF` offer a more direct approach. The choice between the two may depend on the specific requirements of the code and the target architecture. The comment `// or` suggests that either the `LAHF`/`SAHF` sequence or the `PUSHF`/`POPF` sequence can be used, implying they achieve a similar effect in this context.