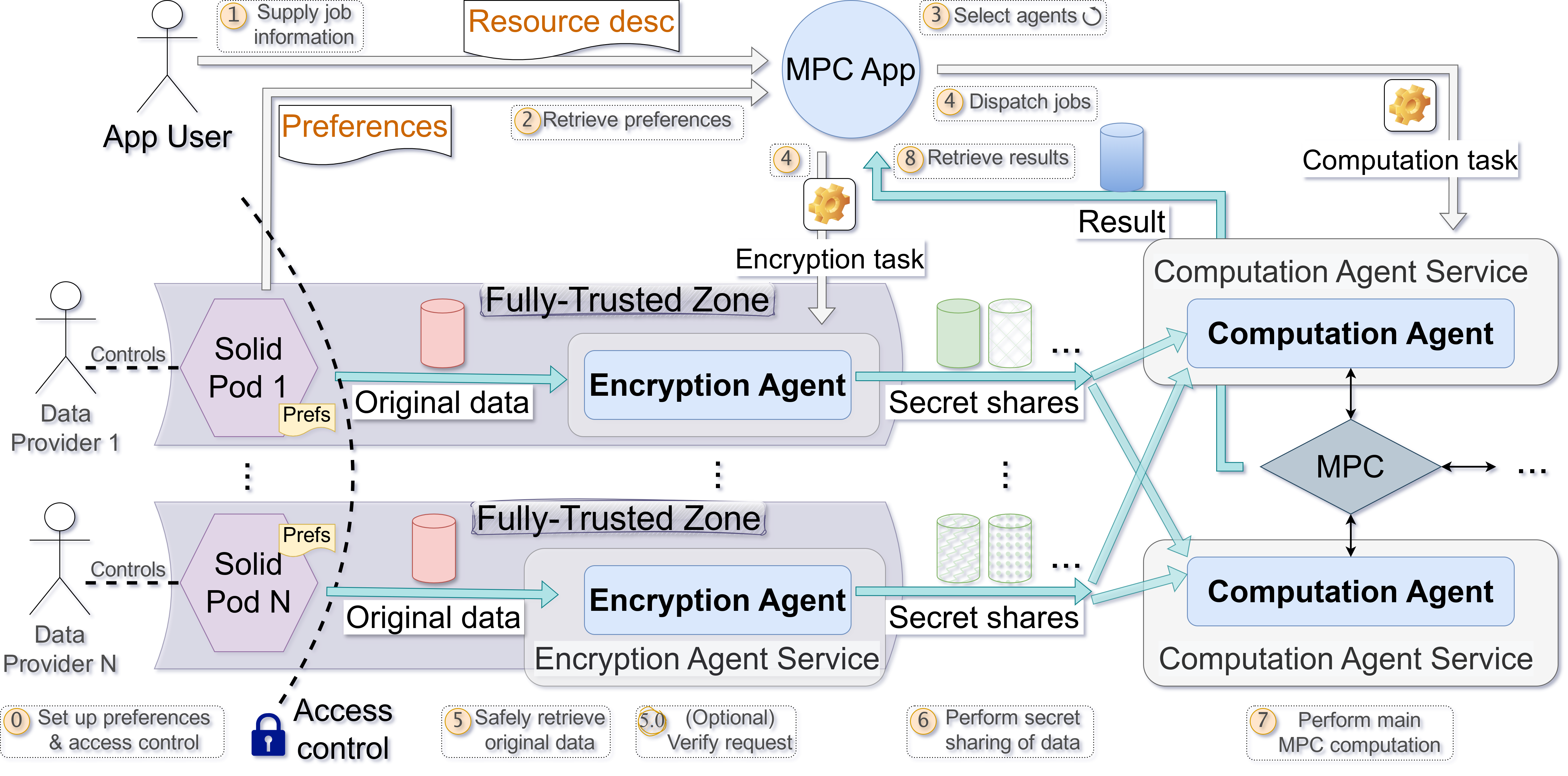
# Technical Document Extraction: Multi-Party Computation (MPC) System Flowchart
## Key Components
1. **App User**
- Initiates the process by supplying job information and retrieving preferences.
- Controls access to Solid Pods (Pod 1 to Pod N).
2. **Data Providers (1 to N)**
- Own and control Solid Pods containing original data.
- Each Pod has a "Prefs" label indicating user preferences.
3. **Fully-Trusted Zone**
- A secure environment where encryption tasks are performed.
- Contains **Encryption Agent Service** and **Computation Agent Service**.
4. **Encryption Agent**
- Performs secret sharing of data (Step 6).
- Outputs "Secret shares" to Computation Agents.
5. **Computation Agent**
- Executes main MPC computation (Step 7).
- Receives secret shares from Encryption Agents.
6. **MPC App**
- Central orchestrator for job dispatching and result retrieval.
- Includes steps for selecting agents (Step 3) and dispatching jobs (Step 4).
7. **Computation Task**
- Represented by a gear icon, indicating computational processing.
8. **Result**
- Output of the MPC computation, retrieved by the App User (Step 8).
---
## Process Flow (Steps 0–8)
1. **Step 0**: *Set up preferences & access control*
- App User configures preferences and access rules.
2. **Step 1**: *Supply job information*
- App User provides job details to the MPC App.
3. **Step 2**: *Retrieve preferences*
- MPC App fetches user preferences from Solid Pods.
4. **Step 3**: *Select agents*
- MPC App chooses Encryption and Computation Agents.
5. **Step 4**: *Dispatch jobs*
- MPC App sends encryption and computation tasks to agents.
6. **Step 5**: *Safely retrieve original data*
- Optional verification of data integrity (marked with "5.0").
7. **Step 6**: *Perform secret sharing of data*
- Encryption Agent splits data into secret shares.
8. **Step 7**: *Perform main MPC computation*
- Computation Agents execute the MPC protocol.
9. **Step 8**: *Retrieve results*
- App User collects final results from the MPC App.
---
## Data Flow Diagram
- **Original Data**
- Flows from Solid Pods (Pod 1 to Pod N) to the Encryption Agent.
- Represented by pink cylinders in the Fully-Trusted Zone.
- **Secret Shares**
- Output of the Encryption Agent, distributed to Computation Agents.
- Depicted as green cylinders with hashed patterns.
- **Computation Task**
- Triggered by the MPC App, leading to the Computation Agent Service.
- **Result**
- Final output of the MPC computation, returned to the App User.
---
## Optional Verification (Step 5.0)
- *Verify request*: Ensures data integrity before encryption.
- Marked as optional in the flowchart.
---
## Color-Coded Elements
- **Pink**: Solid Pods and Fully-Trusted Zone.
- **Blue**: MPC App and Computation Agent Service.
- **Green**: Secret shares and Computation Agent.
- **Yellow**: Gear icon (Computation Task).
---
## Summary
This flowchart illustrates a secure MPC workflow where data is encrypted, shared, and computed across multiple agents while maintaining privacy. The App User interacts with Data Providers via Solid Pods, and the MPC App coordinates agent selection, job dispatching, and result retrieval. Secret sharing and MPC computation occur in a Fully-Trusted Zone to ensure data confidentiality.