## Process Diagram: Malware Detection and Evasion Cycle
### Overview
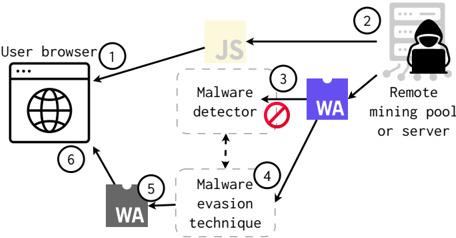
The image is a technical flowchart illustrating a cyclical process involving a user's browser, a remote server, and a malware detection system that incorporates WebAssembly (WA). The diagram depicts a six-step sequence showing how malicious code might be delivered, detected, and subsequently evaded.
### Components/Axes
The diagram consists of the following labeled components and flow arrows:
**Components (with approximate positions):**
1. **User browser** (Left side): Represented by a browser window icon with a globe.
2. **JS** (Top center): A beige box labeled "JS" (JavaScript).
3. **Remote mining pool or server** (Top right): Depicted as a server rack icon with a hooded figure (hacker symbol).
4. **Malware detector** (Center): A dashed-line box containing the text "Malware detector" and a red "prohibited" symbol (circle with a diagonal line).
5. **Malware evasion technique** (Bottom center): A dashed-line box labeled "Malware evasion technique".
6. **WA** (Two instances):
* A blue box labeled "WA" (Right side, connected to the remote server).
* A dark grey box labeled "WA" (Bottom left, connected to the evasion technique box).
**Flow Arrows (Numbered Steps):**
The process is connected by numbered arrows indicating the sequence:
1. Arrow from **User browser** to **JS**.
2. Arrow from **JS** to **Remote mining pool or server**.
3. Arrow from **Remote mining pool or server** to **Malware detector** (via the blue WA box).
4. Arrow from **Malware detector** to **Malware evasion technique**.
5. Arrow from **Malware evasion technique** to the dark grey **WA** box.
6. Arrow from the dark grey **WA** box back to the **User browser**.
**Legend/Key:**
* **WA**: This acronym is used in two boxes. Based on common cybersecurity context, it most likely stands for **WebAssembly**.
### Detailed Analysis
The diagram outlines a specific attack and defense cycle:
1. **Step 1 & 2 (Delivery):** The process begins at the **User browser**. JavaScript (JS) code is sent to a **Remote mining pool or server**. This suggests the initial payload might be a cryptominer.
2. **Step 3 (Detection):** The remote server interacts with a **Malware detector**. This interaction is mediated by a component labeled **WA** (blue box). The detector has a "prohibited" symbol, indicating its function is to block malicious activity.
3. **Step 4 (Evasion):** Upon detection, the flow moves to a **Malware evasion technique**. This implies the malware has a built-in mechanism to react to being detected.
4. **Step 5 & 6 (Re-infection/Loop):** The evasion technique utilizes another **WA** component (dark grey box), which then sends a payload back to the **User browser**, completing the cycle. This suggests the evasion method itself leverages WebAssembly to bypass the detector and re-establish the malicious connection.
### Key Observations
* **Cyclical Nature:** The process is a closed loop (steps 1-6), indicating an ongoing, automated battle between detection and evasion.
* **Central Role of WebAssembly (WA):** WA is implicated in both the initial malicious communication (blue box) and the subsequent evasion technique (dark grey box). This highlights its dual-use potential in cybersecurity—as a tool for both attackers and defenders.
* **Reactive Evasion:** The malware does not simply hide; it actively responds to the **Malware detector** (step 4) by triggering an evasion technique. This indicates a more sophisticated, adaptive threat.
* **Target:** The initial target is the **User browser**, and the ultimate goal, implied by the "mining pool" label, is likely resource hijacking for cryptocurrency mining.
### Interpretation
This diagram illustrates a sophisticated malware lifecycle designed to persist despite detection efforts. It demonstrates a **cat-and-mouse game** where:
1. **Attack Vector:** Malicious JavaScript is initially served from a remote server, likely injected into or downloaded by the user's browser.
2. **Defense Mechanism:** A security tool (Malware detector) identifies the malicious activity, potentially flagging the WebAssembly module used in the attack.
3. **Adversarial Response:** Instead of failing, the malware system pivots. It employs a pre-programmed "evasion technique" that likely involves obfuscation, code transformation, or using a different WA module (the dark grey box) with a signature the detector does not recognize.
4. **Persistence:** The successful evasion allows the malware to re-establish communication with the user's browser, potentially restarting the mining operation or deploying a new payload.
The key takeaway is the **adaptive nature of modern threats**. The malware is not a static file but a system with conditional logic that changes its behavior in response to defensive measures. The repeated use of WebAssembly suggests it is a preferred vehicle for such attacks due to its performance, near-native execution in browsers, and potential complexity which can hinder analysis. The diagram serves as a conceptual model for understanding how detection alone is insufficient without considering the adversary's capacity for automated response and evasion.