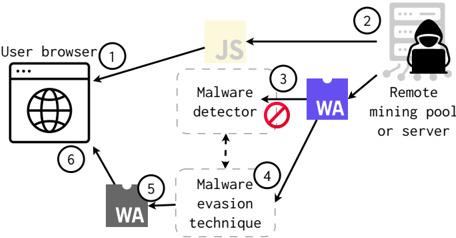
## Diagram: Malware Evasion Technique
### Overview
The image is a diagram illustrating a malware evasion technique involving a user browser, a remote mining pool/server, a malware detector, and a malware evasion technique. The diagram shows the flow of data and actions between these components, numbered 1 through 6.
### Components/Axes
* **User browser:** Represents the user's web browser.
* **JS:** Represents JavaScript code.
* **Remote mining pool or server:** Represents the attacker's server.
* **Malware detector:** Represents a system designed to detect malware.
* **WA (Blue):** Represents a WebAssembly module.
* **Malware evasion technique:** Represents a method used to bypass malware detection.
* **WA (Gray):** Represents a WebAssembly module.
* **Numbers 1-6:** Indicate the sequence of actions or data flow.
### Detailed Analysis
1. **(1) User browser to JS:** The user browser initiates a request that leads to the execution of JavaScript code.
2. **(2) JS to Remote mining pool or server:** The JavaScript code communicates with a remote mining pool or server.
3. **(3) Remote mining pool or server to Malware detector:** The remote mining pool or server sends a WebAssembly module (WA - Blue) to the malware detector, which is blocked (indicated by a red circle with a line through it).
4. **(4) Remote mining pool or server to Malware evasion technique:** The remote mining pool or server sends the WebAssembly module (WA - Blue) to the malware evasion technique.
5. **(5) Malware evasion technique to WA (Gray):** The malware evasion technique transforms the WebAssembly module (WA - Blue) into a modified WebAssembly module (WA - Gray).
6. **(6) WA (Gray) to User browser:** The modified WebAssembly module (WA - Gray) is sent to the user browser.
### Key Observations
* The diagram illustrates a process where a WebAssembly module is used for malicious purposes (mining).
* The malware detector attempts to block the initial WebAssembly module.
* A malware evasion technique is used to modify the WebAssembly module to bypass detection.
* The modified WebAssembly module is then sent to the user browser.
### Interpretation
The diagram depicts a scenario where an attacker attempts to use a user's browser to mine cryptocurrency by injecting a WebAssembly module. The malware detector attempts to block this activity, but the attacker employs a malware evasion technique to modify the WebAssembly module, allowing it to bypass the detector and reach the user's browser. This highlights the ongoing arms race between malware developers and security systems, where evasion techniques are constantly evolving to bypass detection mechanisms. The use of WebAssembly in this context demonstrates how modern web technologies can be exploited for malicious purposes.