\n
## Diagram: Web Attack Flow
### Overview
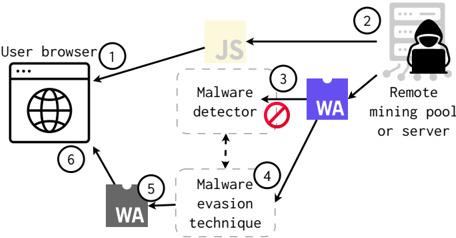
This diagram illustrates the flow of a web-based attack involving JavaScript (JS) and WebAssembly (WA), targeting a user browser and ultimately connecting to a remote mining pool or server controlled by an attacker. The diagram depicts the interaction between the user browser, malware detection systems, and the attacker's infrastructure, highlighting evasion techniques.
### Components/Axes
The diagram consists of the following components, numbered 1 through 6:
1. **User Browser:** Represented by a browser window icon with a globe inside. Labeled "user browser".
2. **Attacker/Remote Server:** Represented by a silhouette of a person wearing a hoodie, labeled "Remote mining pool or server".
3. **Malware Detector:** Represented by a red circle with a diagonal line through it (indicating detection/blocking), labeled "Malware detector".
4. **Malware Evasion Technique:** Represented by a dashed rectangle, labeled "Malware evasion technique".
5. **WebAssembly (WA) - Evasive Code:** Represented by a purple square, labeled "WA".
6. **WebAssembly (WA) - Executed Code:** Represented by a purple circle, labeled "WA".
Arrows indicate the flow of data and control between these components. The text "JS" is positioned between the user browser and the attacker/remote server.
### Detailed Analysis or Content Details
The diagram shows the following flow:
* **Step 1-2:** JavaScript (JS) is delivered from the "Remote mining pool or server" (2) to the "user browser" (1).
* **Step 2-3:** The JS attempts to deliver WebAssembly (WA) code to the "Malware detector" (3).
* **Step 3-4:** The "Malware evasion technique" (4) is employed to bypass the "Malware detector" (3).
* **Step 4-5:** The bypassed WA code (5) is then delivered to the "user browser" (6).
* **Step 1-6:** The "user browser" (1) receives the WA code (6).
* **Step 2-3:** The "Remote mining pool or server" (2) also receives the WA code (3).
The diagram highlights that the malware utilizes a "Malware evasion technique" to avoid detection by the "Malware detector". The use of WebAssembly (WA) is central to this evasion strategy.
### Key Observations
The diagram emphasizes the use of JavaScript as the initial delivery mechanism for the malicious WebAssembly code. The "Malware evasion technique" is a critical component, suggesting that the attacker is actively attempting to bypass security measures. The diagram does not provide specific details about the evasion technique itself, but it indicates its importance in the attack chain. The use of WebAssembly is notable, as it can be used to obfuscate malicious code and make it more difficult to detect.
### Interpretation
This diagram illustrates a common attack vector where JavaScript is used to deliver malicious code (WebAssembly) to a user's browser. The attacker aims to bypass malware detection systems using an "evasion technique," ultimately gaining control of the user's browser resources for purposes such as cryptocurrency mining (as suggested by the "Remote mining pool or server" label). The diagram suggests a sophisticated attack, as it involves the use of WebAssembly, which requires a degree of technical expertise to implement. The diagram is a high-level overview and does not provide details about the specific vulnerabilities exploited or the nature of the evasion technique. It serves as a conceptual illustration of the attack flow, highlighting the key components and their interactions. The diagram is a simplified representation of a complex process, and real-world attacks may involve additional steps and complexities.