## Flowchart: Malware Evasion Process in Browser Environment
### Overview
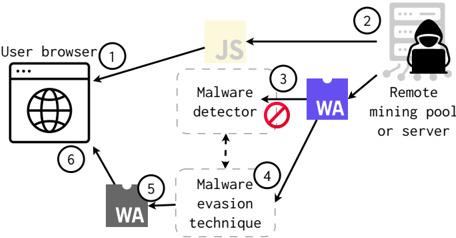
The diagram illustrates a sequential process of malware interaction within a user's browser environment, showing how malicious code bypasses detection mechanisms to connect to remote mining infrastructure. The flow progresses through six distinct stages, with visual indicators of evasion success and final malicious payload delivery.
### Components/Axes
1. **Nodes**:
- Six labeled boxes (1-6) representing process stages
- Arrows indicating directional flow between components
- Color-coded elements (yellow, purple, gray) for categorical differentiation
2. **Key Elements**:
- User browser (1)
- JavaScript (JS) resource (2)
- Malware detector (3)
- Evasion technique (4)
- WebAssembly (WA) module (5)
- Remote mining pool/server (6)
### Detailed Analysis
1. **Stage 1**: User browser initiates connection to JS resource (yellow box)
2. **Stage 2**: JS executes, triggering malware detector (3) with red prohibition symbol indicating detection attempt
3. **Stage 3**: Malware employs evasion technique (4) to bypass detection
4. **Stage 4**: Successful evasion leads to WebAssembly (WA) module deployment (5)
5. **Stage 5**: WA module establishes connection to remote mining pool/server (6)
6. **Final Connection**: Purple box (WA) directly links to mining infrastructure
### Key Observations
- Malware detector (3) is explicitly blocked (red prohibition symbol)
- Evasion technique (4) acts as critical pivot point between detection attempt and successful execution
- WebAssembly (WA) serves as intermediary between browser and mining infrastructure
- Final connection (6) bypasses all security checks shown in earlier stages
### Interpretation
This diagram demonstrates a sophisticated malware delivery chain where:
1. Initial detection attempts are actively thwarted through evasion techniques
2. WebAssembly (WA) acts as a stealthy delivery mechanism for mining malware
3. The flow suggests a multi-stage attack where each component (JS, WA) serves specific roles in bypassing security
4. The prohibition symbol on the malware detector indicates this is a known evasion pattern
5. The direct connection from WA to mining pool suggests resource exploitation as final payload
The process highlights the cat-and-mouse game between browser security mechanisms and malware developers, with WebAssembly emerging as a key vector for bypassing traditional detection methods in modern browser environments.