## Diagram: Taxonomy of SCA Attacks on DNN Implementations
### Overview
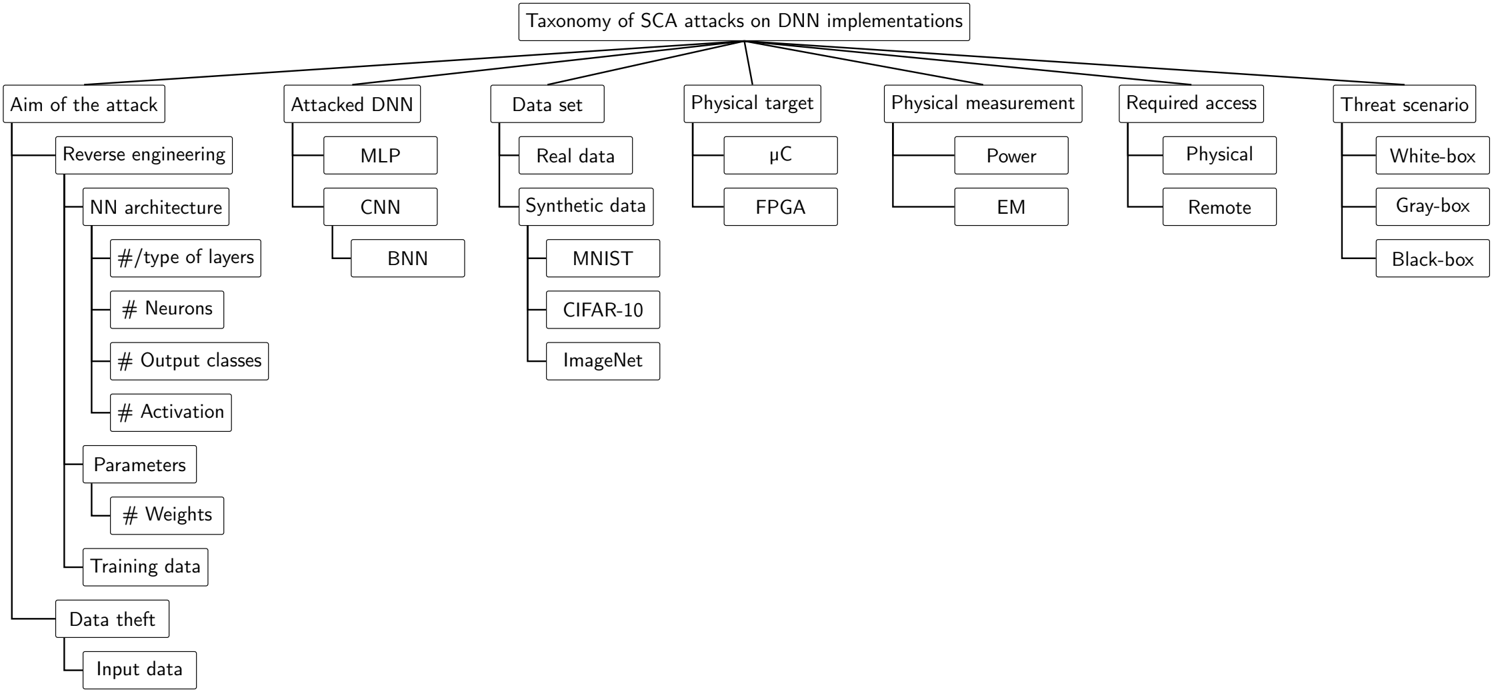
The image presents a hierarchical diagram outlining a taxonomy of Side-Channel Attacks (SCA) on Deep Neural Network (DNN) implementations. The diagram branches out from a central topic into various categories and subcategories, detailing different aspects of such attacks.
### Components/Axes
* **Main Title:** Taxonomy of SCA attacks on DNN implementations
* **Categories (First Level):**
* Aim of the attack
* Attacked DNN
* Data set
* Physical target
* Physical measurement
* Required access
* Threat scenario
### Detailed Analysis
* **Aim of the attack:**
* Reverse engineering
* NN architecture
* #/type of layers
* # Neurons
* # Output classes
* # Activation
* Parameters
* # Weights
* Training data
* Data theft
* Input data
* **Attacked DNN:**
* MLP (Multilayer Perceptron)
* CNN (Convolutional Neural Network)
* BNN (Binary Neural Network)
* **Data set:**
* Real data
* Synthetic data
* MNIST
* CIFAR-10
* ImageNet
* **Physical target:**
* μC (Microcontroller)
* FPGA (Field-Programmable Gate Array)
* **Physical measurement:**
* Power
* EM (Electromagnetic)
* **Required access:**
* Physical
* Remote
* **Threat scenario:**
* White-box
* Gray-box
* Black-box
### Key Observations
* The diagram provides a structured breakdown of SCA attacks, categorizing them based on different attack vectors and targets.
* The "Aim of the attack" category is further subdivided into reverse engineering and data theft, with reverse engineering having more detailed sub-categories related to NN architecture and parameters.
* The "Attacked DNN" category lists common DNN architectures.
* The "Data set" category includes both real and synthetic data, along with specific datasets like MNIST, CIFAR-10, and ImageNet.
* The "Physical target" category focuses on hardware implementations.
* The "Physical measurement" category lists common side-channel signals.
* The "Required access" category distinguishes between physical and remote access.
* The "Threat scenario" category outlines different levels of attacker knowledge.
### Interpretation
The diagram serves as a comprehensive overview of the various dimensions involved in Side-Channel Attacks on DNN implementations. It highlights the different goals of the attacker, the types of DNNs targeted, the data used, the hardware platforms, the measurement techniques, the access requirements, and the threat models. This taxonomy is useful for understanding the landscape of SCA attacks and for developing effective countermeasures. The detailed breakdown of "Aim of the attack" suggests that reverse engineering of the neural network architecture and parameters is a primary concern in SCA attacks.