## Diagram: Taxonomy of SCA attacks on DNN implementations
### Overview
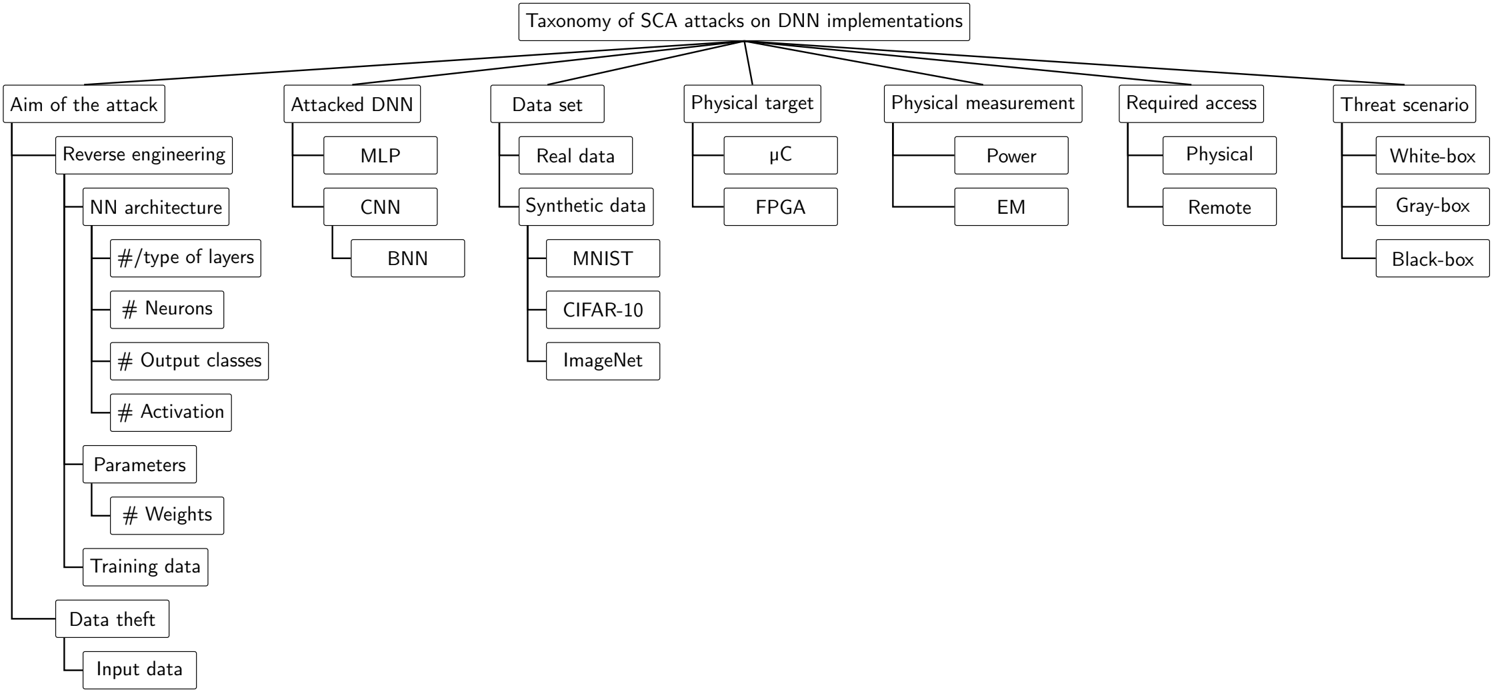
The image displays a hierarchical taxonomy diagram titled "Taxonomy of SCA attacks on DNN implementations." It classifies Side-Channel Analysis (SCA) attacks targeting Deep Neural Network (DNN) implementations across seven primary categorical dimensions. The structure is a top-down tree, with the main title at the top center, branching into seven main categories, each of which further subdivides into specific sub-categories or examples.
### Components/Axes
The diagram is organized into a tree structure with the following main branches, listed from left to right:
1. **Aim of the attack**
2. **Attacked DNN**
3. **Data set**
4. **Physical target**
5. **Physical measurement**
6. **Required access**
7. **Threat scenario**
Each main branch is contained within a rectangular box and connects to its sub-categories via lines.
### Detailed Analysis
**1. Aim of the attack**
This branch has two primary sub-branches:
* **Reverse engineering**: This further decomposes into three detailed sub-categories:
* **NN architecture**: This includes the specific attributes:
* `#/type of layers`
* `# Neurons`
* `# Output classes`
* `# Activation`
* **Parameters**: This includes the specific attribute:
* `# Weights`
* **Training data**
* **Data theft**: This has one sub-category:
* `Input data`
**2. Attacked DNN**
This branch lists three types of neural network architectures:
* `MLP` (Multi-Layer Perceptron)
* `CNN` (Convolutional Neural Network)
* `BNN` (Binary Neural Network)
**3. Data set**
This branch splits into two main types:
* `Real data`
* `Synthetic data`: This sub-branch further lists three specific, well-known datasets:
* `MNIST`
* `CIFAR-10`
* `ImageNet`
**4. Physical target**
This branch lists two types of hardware targets:
* `μC` (Microcontroller)
* `FPGA` (Field-Programmable Gate Array)
**5. Physical measurement**
This branch lists two types of side-channel signals:
* `Power`
* `EM` (Electromagnetic)
**6. Required access**
This branch lists two levels of attacker access:
* `Physical`
* `Remote`
**7. Threat scenario**
This branch lists three standard attacker knowledge models:
* `White-box`
* `Gray-box`
* `Black-box`
### Key Observations
* The taxonomy is comprehensive, covering the attack's goal, the target system (both software model and hardware), the data involved, the measurement method, the access required, and the threat model.
* The "Aim of the attack" branch is the most deeply nested, indicating that reverse engineering is a complex goal with many extractable attributes (architecture details, parameters, training data).
* The diagram uses consistent visual language: rectangular boxes for categories and straight lines for hierarchical relationships.
* All text is in English. No other languages are present.
### Interpretation
This taxonomy provides a structured framework for analyzing and categorizing side-channel attacks against neural network implementations. It serves as a reference for researchers and security engineers to:
1. **Classify Existing Attacks:** Any given SCA attack on a DNN can be described by selecting one option from each of the seven main branches (e.g., an attack aiming for *Data theft* of *Input data* from a *CNN* running on an *FPGA*, using *Power* analysis, requiring *Physical* access in a *Gray-box* scenario).
2. **Identify Attack Vectors:** It highlights the multiple dimensions of vulnerability in a DNN deployment stack—from the abstract model architecture down to the physical hardware and its measurable emissions.
3. **Guide Defense Strategy:** By understanding the taxonomy, defenders can identify which aspects of their system (e.g., the physical target, the measurement leakage, the access controls) need hardening against specific attack aims and threat scenarios.
4. **Systematize Research:** It offers a common vocabulary and structure for comparing different attacks and identifying gaps in the current landscape (e.g., are *Remote* attacks on *BNNs* using *EM* measurements under-explored?).
The diagram effectively communicates that an SCA attack is not a monolithic concept but a combination of choices across these seven dimensions, which collectively define the attack's profile, complexity, and potential impact.