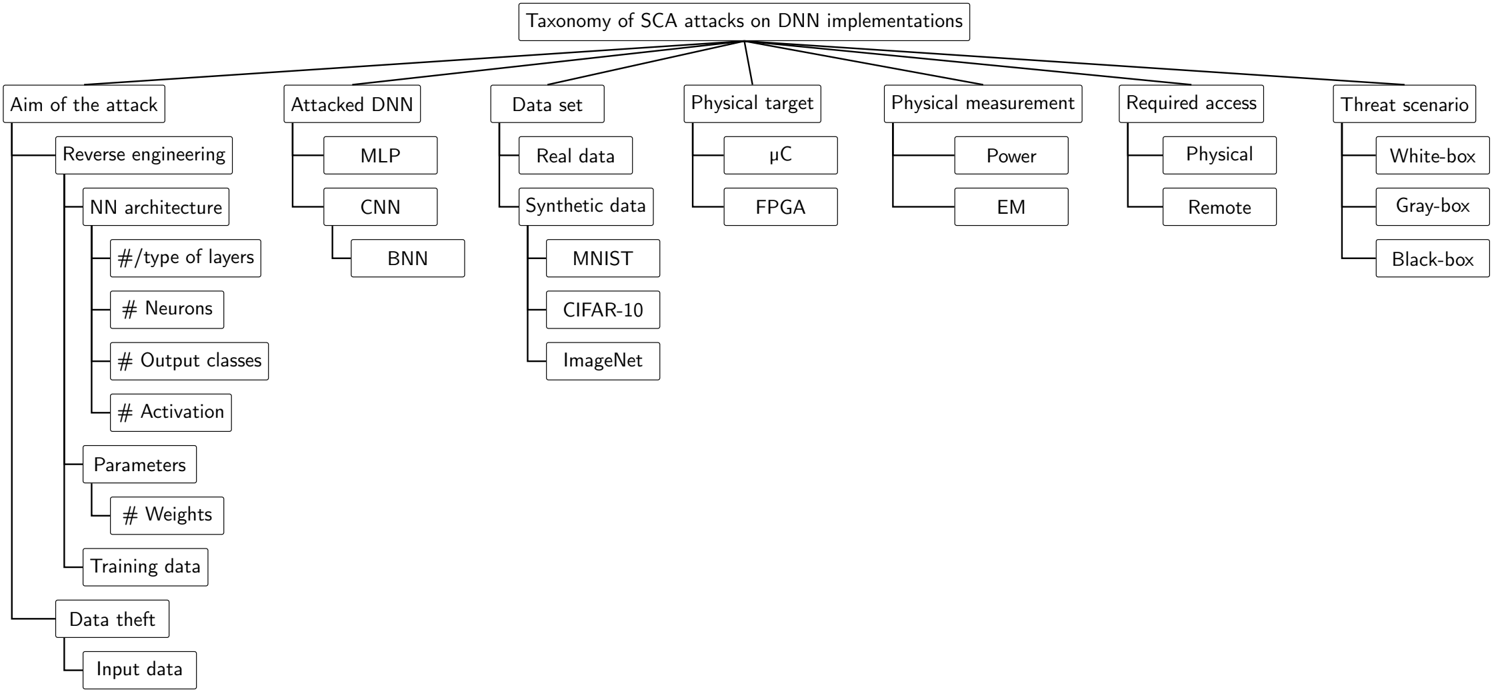
## Flowchart: Taxonomy of SCA attacks on DNN implementations
### Overview
The diagram illustrates a hierarchical taxonomy of side-channel attacks (SCA) targeting deep neural network (DNN) implementations. It categorizes attack methodologies, targets, and scenarios into interconnected branches, emphasizing technical and operational dimensions of SCA.
### Components/Axes
1. **Central Node**: "Taxonomy of SCA attacks on DNN implementations"
2. **Primary Branches**:
- Aim of the attack
- Attacked DNN
- Data set
- Physical target
- Physical measurement
- Required access
- Threat scenario
3. **Subcategories**:
- **Aim of the attack**:
- Reverse engineering
- NN architecture (e.g., #/type of layers, # Neurons, # Output classes, # Activation)
- Parameters (e.g., # Weights)
- Training data
- Data theft (Input data)
- **Attacked DNN**:
- MLP, CNN, BNN
- **Data set**:
- Real data
- Synthetic data (e.g., MNIST, CIFAR-10, ImageNet)
- **Physical target**:
- μC (microcontroller)
- FPGA (Field-Programmable Gate Array)
- **Physical measurement**:
- Power
- EM (Electromagnetic)
- **Required access**:
- Physical
- Remote
- **Threat scenario**:
- White-box
- Gray-box
- Black-box
### Detailed Analysis
- **Hierarchical Structure**: The taxonomy is organized as a tree, with the central node branching into seven primary categories. Each primary category further subdivides into specific technical attributes (e.g., "NN architecture" includes layers, neurons, activation functions).
- **Technical Focus**: Subcategories emphasize hardware (μC, FPGA), data types (real vs. synthetic), and attack objectives (e.g., reverse engineering parameters).
- **Threat Scenarios**: The "Threat scenario" branch explicitly defines attack perspectives (White-box, Gray-box, Black-box), critical for assessing attack feasibility.
### Key Observations
- **Interconnectedness**: The diagram links attack aims (e.g., reverse engineering) to specific DNN components (e.g., CNN layers) and physical targets (e.g., μC power measurements).
- **Data Diversity**: The "Data set" branch highlights both real-world datasets (MNIST, CIFAR-10) and synthetic data, reflecting varied attack contexts.
- **Access Requirements**: The "Required access" branch distinguishes between physical proximity (Physical) and remote execution (Remote), impacting attack complexity.
### Interpretation
This taxonomy provides a structured framework for analyzing SCA vulnerabilities in DNN implementations. It emphasizes:
1. **Attack Objectives**: Reverse engineering parameters (weights, layers) and data theft are central aims, suggesting attackers prioritize model intellectual property and training data.
2. **Hardware-Software Interplay**: Physical targets (μC, FPGA) and measurements (Power, EM) underscore hardware vulnerabilities in DNN deployments.
3. **Attack Feasibility**: Threat scenarios (White-box vs. Black-box) determine the attacker’s knowledge of the system, influencing the choice of attack vectors (e.g., side-channel leakage vs. brute-force).
The diagram highlights the multidimensional nature of SCA, where attackers exploit hardware leakage, data integrity, and model architecture to compromise DNNs. It serves as a reference for designing countermeasures (e.g., masking power traces, encrypting data) and assessing risk across different attack scenarios.