\n
## Diagram: Secure Computing Architectures Comparison
### Overview
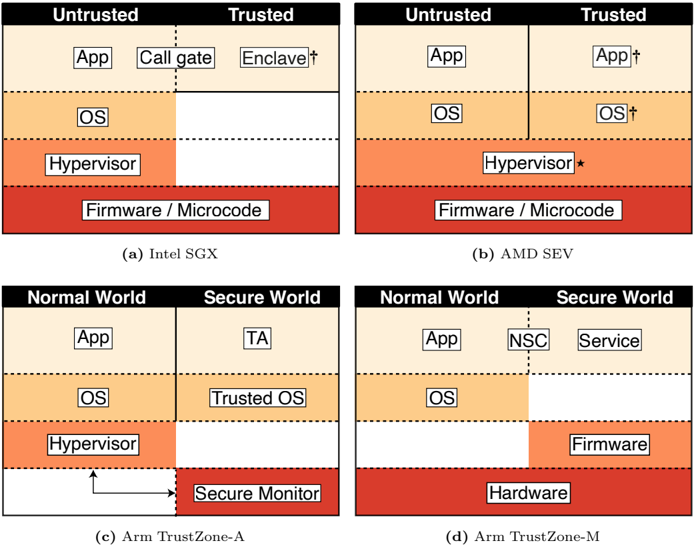
The image presents a comparative diagram illustrating the architectural differences between four secure computing technologies: Intel SGX, AMD SEV, Arm TrustZone-A, and Arm TrustZone-M. Each technology is represented as a stacked block diagram, visually partitioning the system into untrusted and trusted regions. The diagram highlights the placement of key components like Applications (App), Operating Systems (OS), Hypervisors, Firmware/Microcode, Enclaves, Trusted OS, Secure Monitor, and Services within each architecture.
### Components/Axes
The diagram is divided into four quadrants, each representing a different secure computing architecture. Each quadrant is labeled:
* (a) Intel SGX
* (b) AMD SEV
* (c) Arm TrustZone-A
* (d) Arm TrustZone-M
Each quadrant is further divided into layers, from bottom to top:
* Firmware / Microcode (Red)
* Hypervisor (Orange)
* OS (Yellow)
* App (White/Black)
Each architecture defines a boundary between "Untrusted" and "Trusted" regions. Specific components within the trusted regions are labeled as follows:
* Intel SGX: "Call gate", "Enclave"
* AMD SEV: "App", "OS"
* Arm TrustZone-A: "TA" (Trusted Application), "Secure Monitor"
* Arm TrustZone-M: "NSC" (Non-Secure Component), "Service"
Arrows indicate flow or interaction between components.
### Detailed Analysis or Content Details
**Intel SGX (a):**
* The diagram shows a clear separation between "Untrusted" and "Trusted" regions.
* The "App" resides in the untrusted region, interacting with a "Call gate" to access the "Enclave" within the trusted region.
* The "OS", "Hypervisor", and "Firmware/Microcode" layers span both untrusted and trusted regions.
* The "Enclave" is positioned above the "OS" and "Hypervisor" within the trusted region.
**AMD SEV (b):**
* Similar to Intel SGX, there's a separation between "Untrusted" and "Trusted" regions.
* The "App" resides entirely in the untrusted region.
* The "OS" is partially in the untrusted region and partially in the trusted region.
* The "Hypervisor" is partially in the untrusted region and partially in the trusted region, marked with an asterisk (*).
* The "Firmware/Microcode" layer spans both regions.
**Arm TrustZone-A (c):**
* This architecture defines "Normal World" (Untrusted) and "Secure World" (Trusted).
* The "App" resides in the "Normal World".
* A "Trusted Application" (TA) resides in the "Secure World".
* The "OS" and "Hypervisor" layers are in the "Normal World".
* A "Secure Monitor" is positioned below the "Hypervisor" in the "Secure World", with an arrow indicating a flow from the "Secure Monitor" to the "Hypervisor".
**Arm TrustZone-M (d):**
* This architecture also defines "Normal World" and "Secure World".
* The "App" resides in the "Normal World".
* A "Service" resides in the "Secure World".
* The "OS" is in the "Normal World".
* "Firmware" and "Hardware" layers are in the "Secure World".
* A "Non-Secure Component" (NSC) is positioned above the "Service" in the "Secure World".
### Key Observations
* Intel SGX and AMD SEV focus on creating isolated enclaves within the existing system architecture, while Arm TrustZone-A and TrustZone-M implement a more fundamental hardware-based separation into "Normal" and "Secure" worlds.
* The placement of the "Hypervisor" differs significantly between the architectures. In AMD SEV, it's partially in both regions, while in Arm TrustZone-A, it's entirely in the untrusted region.
* The level of hardware involvement varies. Arm TrustZone-M explicitly includes "Hardware" as a core component of the secure world.
* The diagrams use color-coding to represent different layers of the system stack, aiding in visual comparison.
### Interpretation
The diagram effectively illustrates the diverse approaches to secure computing. Intel SGX and AMD SEV aim to protect specific code segments (enclaves) from a potentially compromised OS and hypervisor. This is a software-centric approach, relying on hardware support for isolation. Arm TrustZone, in both its A and M variants, takes a more holistic hardware-based approach, creating a physically separated secure environment.
The differences in hypervisor placement suggest varying levels of trust in the hypervisor itself. AMD SEV's partial placement in the trusted region implies a degree of trust, while Arm TrustZone-A's complete placement in the untrusted region suggests a more skeptical approach.
The inclusion of "Hardware" in Arm TrustZone-M highlights the importance of dedicated hardware security features in this architecture. The arrows in Arm TrustZone-A indicate a controlled interaction between the secure and normal worlds, mediated by the Secure Monitor.
The diagram doesn't provide quantitative data, but it offers a valuable qualitative comparison of these secure computing technologies, revealing their architectural strengths and weaknesses. It suggests that the choice of architecture depends on the specific security requirements and threat model. The diagram is a high-level overview and doesn't delve into the complexities of implementation or the specific security guarantees offered by each technology.