\n
## Diagram: Foundation Model Lifecycle & Risks
### Overview
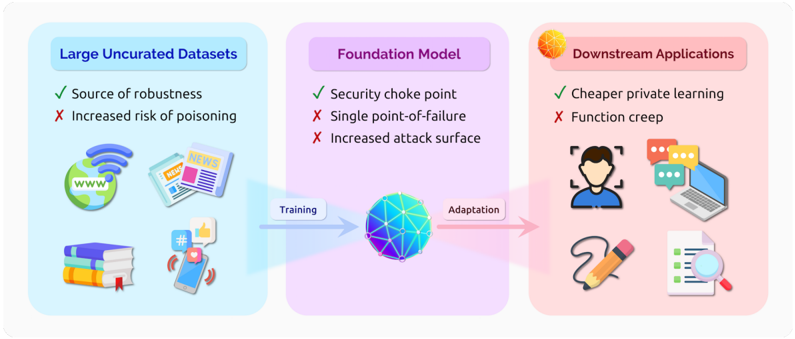
The image is a diagram illustrating the lifecycle of a foundation model, from large uncurated datasets through the foundation model itself, to downstream applications. It highlights both the benefits and risks associated with each stage. The diagram uses a left-to-right flow to represent the process of training and adaptation.
### Components/Axes
The diagram is divided into three main sections, each represented by a rounded rectangle with a light color background:
1. **Large Uncurated Datasets** (Left, light blue background): This section represents the initial data source.
2. **Foundation Model** (Center, light purple background): This section represents the core model being trained.
3. **Downstream Applications** (Right, light orange background): This section represents the applications built upon the foundation model.
An arrow connects the "Large Uncurated Datasets" section to the "Foundation Model" section, labeled "Training". Another arrow connects the "Foundation Model" section to the "Downstream Applications" section, labeled "Adaptation".
Each section contains a list of bullet points with checkmarks (✓) indicating benefits and crosses (✗) indicating risks. Icons are used to visually represent the data sources and applications.
### Detailed Analysis or Content Details
**Large Uncurated Datasets:**
* ✓ Source of robustness
* ✗ Increased risk of poisoning
* Icons present: Globe with wifi signal, Newspaper, Book Stack, Smartphone with hashtag.
**Foundation Model:**
* ✓ Security choke point
* ✗ Single point-of-failure
* ✗ Increased attack surface
* Central element: A spherical, wireframe globe with interconnected nodes, colored in shades of blue.
**Downstream Applications:**
* ✓ Cheaper private learning
* ✗ Function creep
* Icons present: Person, Laptop, Pencil, Magnifying Glass over Document.
### Key Observations
The diagram emphasizes the trade-offs inherent in using large, uncurated datasets and powerful foundation models. While these approaches offer benefits like robustness and cost-effectiveness, they also introduce significant risks related to security, reliability, and unintended consequences. The central "Foundation Model" is visually depicted as a complex network, highlighting its intricate nature and potential vulnerabilities. The flow from data to model to application is clear and linear.
### Interpretation
This diagram illustrates a common pattern in machine learning: the tension between openness and control. Utilizing large, readily available datasets (uncurated) provides robustness but introduces risks of data poisoning and security vulnerabilities. The foundation model acts as a central point of control (security choke point) but also becomes a single point of failure and a larger attack surface. Finally, downstream applications benefit from cheaper learning but are susceptible to "function creep" – the tendency for models to be used for purposes beyond their original intent.
The diagram suggests that careful consideration must be given to data quality, model security, and responsible deployment when building and using foundation models. The visual representation of the foundation model as a complex network underscores the difficulty of fully understanding and controlling these systems. The diagram is a cautionary tale, highlighting the need for proactive risk mitigation strategies throughout the entire lifecycle of a foundation model.