\n
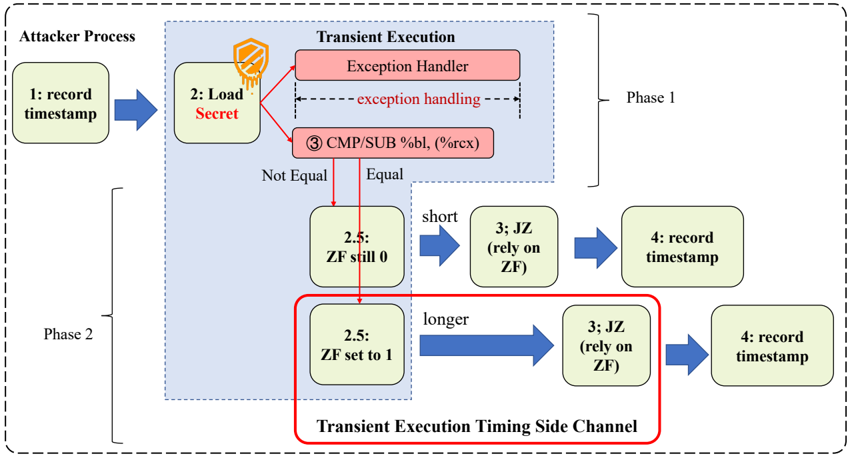
## Diagram: Transient Execution Timing Side Channel
### Overview
This diagram illustrates a transient execution timing side channel attack. It depicts two phases (Phase 1 and Phase 2) of the attack, showing how an attacker process interacts with a transient execution environment to infer information about a secret. The diagram uses a flowchart-style representation with numbered steps and conditional branching based on the Zero Flag (ZF) register.
### Components/Axes
The diagram is divided into three main sections:
* **Attacker Process:** Located on the left side, representing the attacker's actions.
* **Transient Execution:** Occupies the central portion, detailing the execution flow within the target system.
* **Phase Indicators:** "Phase 1" and "Phase 2" are labeled in the top-right and bottom-left corners, respectively, demarcating the two stages of the attack.
Key components within the Transient Execution section include:
* **Exception Handler:** A red rectangle labeled "Exception Handler".
* **CMP/SUB %bl, (%rcx):** A light-orange rectangle representing a comparison and subtraction operation.
* **2.5: ZF still 0 / ZF set to 1:** Two light-green rectangles representing conditional execution paths based on the Zero Flag.
* **3: JZ (rely on ZF):** Two light-blue rectangles representing a conditional jump instruction.
* **4: record timestamp:** Two light-blue rectangles representing the recording of a timestamp.
* **Transient Execution Timing Side Channel:** A red box encompassing the lower portion of the diagram.
The diagram uses arrows to indicate the flow of execution and data. The dashed gray border encompasses the entire process.
### Detailed Analysis or Content Details
The diagram details the following steps:
**Phase 1:**
1. **1: record timestamp:** The attacker process begins by recording an initial timestamp. (Blue arrow)
2. **2: Load Secret:** The attacker triggers a load of a secret value. (Dashed arrow with a shield icon)
3. **Exception Handling:** The load triggers an exception, which is handled by the Exception Handler. (Dashed arrow)
4. **3 CMP/SUB %bl, (%rcx):** A comparison and subtraction operation is performed. The operands are %bl and the value pointed to by %rcx.
5. **Conditional Branching:** The result of the comparison determines the execution path:
* **Not Equal:** If the values are not equal, the execution proceeds to "2.5: ZF still 0".
* **Equal:** If the values are equal, the execution proceeds to "3: JZ (rely on ZF)".
6. **2.5: ZF still 0:** If the Zero Flag is still 0, the execution proceeds to "3: JZ (rely on ZF)".
7. **3: JZ (rely on ZF):** A conditional jump instruction is executed, relying on the Zero Flag.
8. **4: record timestamp:** The attacker process records a second timestamp.
**Phase 2:**
The process repeats steps 1-8, but with a different outcome based on the Zero Flag:
1. **1: record timestamp:** The attacker process begins by recording an initial timestamp. (Blue arrow)
2. **2: Load Secret:** The attacker triggers a load of a secret value. (Dashed arrow with a shield icon)
3. **Exception Handling:** The load triggers an exception, which is handled by the Exception Handler. (Dashed arrow)
4. **3 CMP/SUB %bl, (%rcx):** A comparison and subtraction operation is performed. The operands are %bl and the value pointed to by %rcx.
5. **Conditional Branching:** The result of the comparison determines the execution path:
* **Not Equal:** If the values are not equal, the execution proceeds to "2.5: ZF set to 1".
* **Equal:** If the values are equal, the execution proceeds to "3: JZ (rely on ZF)".
6. **2.5: ZF set to 1:** If the Zero Flag is set to 1, the execution proceeds to "3: JZ (rely on ZF)".
7. **3: JZ (rely on ZF):** A conditional jump instruction is executed, relying on the Zero Flag.
8. **4: record timestamp:** The attacker process records a second timestamp.
The diagram indicates that the "Equal" path is "short" while the "Not Equal" path is "longer".
### Key Observations
The diagram highlights the timing difference between the two execution paths (Equal and Not Equal) as the core of the side channel attack. The attacker leverages the difference in execution time, measured by the timestamps, to infer information about the secret value. The Zero Flag (ZF) is crucial in determining the execution path and, consequently, the timing.
### Interpretation
This diagram illustrates a transient execution timing side channel attack, specifically exploiting the timing differences caused by conditional branching based on the Zero Flag. The attacker initiates a process that triggers an exception, leading to a comparison operation. The outcome of this comparison (Equal or Not Equal) dictates which path the execution takes, resulting in different execution times. By precisely measuring these timing differences, the attacker can deduce information about the secret value being compared. The "Transient Execution Timing Side Channel" label emphasizes that the attack relies on the transient state of the processor during exception handling. The two phases represent the attacker repeating the process to gather enough data for a reliable analysis. The shield icon on the dashed arrow suggests that the secret is protected, but the attack bypasses traditional security measures by exploiting a subtle timing characteristic of the processor.