## Diagram: Attacker Process with Transient Execution Timing Side Channel
### Overview
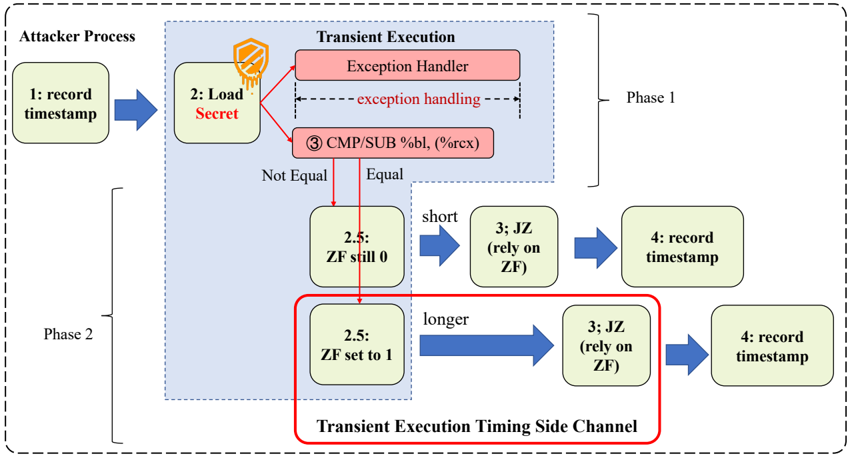
This diagram illustrates an attacker's process to exploit transient execution timing side channels. It is divided into two phases, with decision points based on CPU flags (ZF/Zero Flag) and exception handling. The flow involves recording timestamps, loading secrets, and conditional branching based on CPU operations.
### Components/Axes
- **Phase 1** (dashed box):
- **1: record timestamp** → **2: Load Secret** → **3: JS (rely on ZF)** → **4: record timestamp**
- **Exception Handler** (red box) with **CMP/SUB %bl, (%rcx)** comparison
- **Transient Execution** (blue box) with **ZF (Zero Flag)** checks
- **Phase 2** (solid box):
- **2.5: ZF still 0** (short path) vs. **ZF set to 1** (longer path)
- Arrows labeled **"short"** and **"longer"** indicate timing differences
- **Legend**:
- Red: Exception Handler
- Blue: Transient Execution Timing Side Channel
### Detailed Analysis
1. **Phase 1**:
- **Step 1**: Attacker records a timestamp.
- **Step 2**: Loads a secret into memory.
- **Step 3**: Executes a transient operation (`CMP/SUB %bl, (%rcx)`) to compare values.
- If **CMP/SUB result ≠ 0**, exception handling triggers.
- If **CMP/SUB result = 0**, flow proceeds to Phase 2.
- **Step 4**: Records a second timestamp to measure execution time.
2. **Phase 2**:
- **Step 2.5**:
- If **ZF still 0** (short path), flow proceeds directly to Step 3.
- If **ZF set to 1** (longer path), flow takes a detour, increasing execution time.
- **Step 3**: JS operation relies on ZF state.
- **Step 4**: Final timestamp recorded to infer ZF state via timing differences.
### Key Observations
- **Timing Side Channel**: The attacker infers ZF state by measuring execution time differences between "short" and "longer" paths.
- **Exception Handling**: The red box highlights a critical component where exceptions may leak information.
- **Conditional Branching**: ZF state determines the attack's success, with timing discrepancies revealing secrets.
### Interpretation
This diagram models a **transient execution attack** where the attacker exploits timing variations caused by CPU flag states (ZF) and exception handling. By comparing timestamps before and after transient operations, the attacker deduces whether ZF was set to 0 or 1, indirectly revealing secret data. The red box around Step 2.5 emphasizes the critical decision point where timing differences are maximized. The blue shading of the "Transient Execution Timing Side Channel" box underscores its role as the attack vector. This aligns with real-world side-channel attacks like **Speculative Execution vulnerabilities (e.g., Spectre)**.