## Scatter Plot Series: Timing Side-Channel Analysis of Cookie Byte Guesses
### Overview
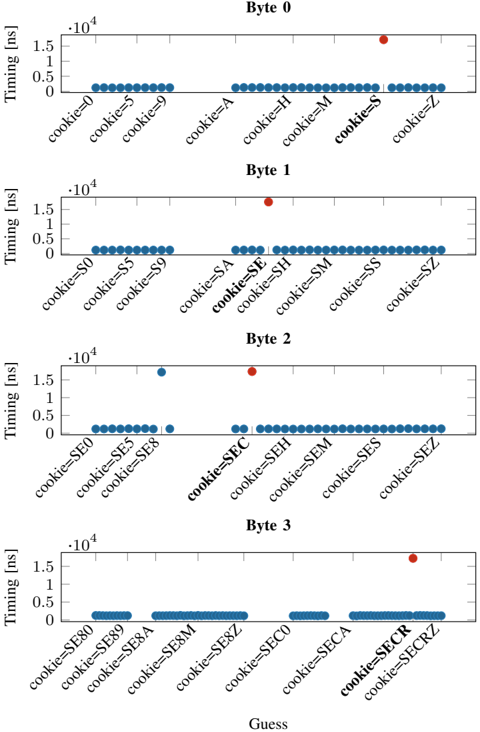
The image displays a series of four vertically stacked scatter plots, each representing a timing analysis for guessing a single byte of a secret cookie. The plots are labeled "Byte 0" through "Byte 3" from top to bottom. Each plot shows the measured timing (in nanoseconds) for various guesses of that byte's value. A single data point in each plot is colored red, indicating the correct guess for that byte position, while all other (incorrect) guesses are colored blue. The overall pattern demonstrates a timing side-channel vulnerability where the correct byte guess results in a significantly higher processing time.
### Components/Axes
* **Chart Type:** Four vertically aligned scatter plots.
* **Y-Axis (All Plots):** Labeled "Timing [ns]". The scale is linear, ranging from 0 to 1.5 x 10⁴ ns (15,000 nanoseconds). Major tick marks are at 0, 0.5, 1, and 1.5 (all multiplied by 10⁴).
* **X-Axis (All Plots):** Labeled "Guess" at the very bottom of the entire figure. Each subplot has its own x-axis with categorical labels representing specific byte guesses.
* **Data Series:**
* **Blue Dots:** Represent timing measurements for incorrect guesses of the byte value.
* **Red Dot:** Represents the timing measurement for the correct guess of the byte value. Its placement is specific to each subplot.
* **Subplot Titles:** "Byte 0", "Byte 1", "Byte 2", "Byte 3" (centered above each respective plot).
### Detailed Analysis
**Byte 0 (Top Plot):**
* **X-Axis Labels (Guesses):** `cookie=0`, `cookie=5`, `cookie=9`, `cookie=A`, `cookie=H`, `cookie=M`, `cookie=S`, `cookie=Z`.
* **Data Distribution:** All blue dots (incorrect guesses) are clustered very close to 0 ns timing.
* **Red Dot (Correct Guess):** Positioned above the label `cookie=S`. Its y-value is approximately 1.5 x 10⁴ ns (15,000 ns).
* **Trend:** A single, dramatic outlier (red) at a high timing value, with all other points forming a flat baseline near zero.
**Byte 1 (Second Plot):**
* **X-Axis Labels (Guesses):** `cookie=S0`, `cookie=S5`, `cookie=S9`, `cookie=SA`, `cookie=SE`, `cookie=SH`, `cookie=SM`, `cookie=SS`, `cookie=SZ`.
* **Data Distribution:** Blue dots are again clustered near 0 ns.
* **Red Dot (Correct Guess):** Positioned above the label `cookie=SE`. Its y-value is approximately 1.5 x 10⁴ ns.
* **Trend:** Identical pattern to Byte 0: one high-timing outlier (red) corresponding to the correct guess.
**Byte 2 (Third Plot):**
* **X-Axis Labels (Guesses):** `cookie=SE0`, `cookie=SE5`, `cookie=SE8`, `cookie=SEC`, `cookie=SEH`, `cookie=SEM`, `cookie=SES`, `cookie=SEZ`.
* **Data Distribution:** Most blue dots are near 0 ns. There is one blue dot with a notably higher timing (approx. 1.2 x 10⁴ ns) located above `cookie=SE8`.
* **Red Dot (Correct Guess):** Positioned above the label `cookie=SEC`. Its y-value is approximately 1.5 x 10⁴ ns.
* **Trend:** The correct guess (`SEC`) is the highest point. An incorrect guess (`SE8`) also shows elevated timing, but is still lower than the correct guess.
**Byte 3 (Bottom Plot):**
* **X-Axis Labels (Guesses):** `cookie=SE80`, `cookie=SE89`, `cookie=SE8A`, `cookie=SE8M`, `cookie=SE8Z`, `cookie=SEC0`, `cookie=SECA`, `cookie=SECR`, `cookie=SECRZ`.
* **Data Distribution:** All blue dots are clustered near 0 ns.
* **Red Dot (Correct Guess):** Positioned above the label `cookie=SECR`. Its y-value is approximately 1.5 x 10⁴ ns.
* **Trend:** Returns to the clear pattern of a single, high-timing outlier for the correct guess.
### Key Observations
1. **Consistent Timing Spike:** For each byte position (0-3), the correct guess (`S`, `SE`, `SEC`, `SECR`) consistently produces a timing measurement at or near the maximum scale value of ~15,000 ns.
2. **Low Baseline for Incorrect Guesses:** The vast majority of incorrect guesses result in timing measurements very close to 0 ns, creating a clear baseline.
3. **Single Anomaly:** In the "Byte 2" plot, the incorrect guess `cookie=SE8` shows a timing of ~12,000 ns, which is a significant outlier among the incorrect guesses. This could indicate a partial match or a different code path being triggered.
4. **Progressive Secret Recovery:** The x-axis labels reveal the secret cookie is being built byte-by-byte: `S` -> `SE` -> `SEC` -> `SECR`. The guesses for each subsequent byte are prefixed with the previously discovered correct bytes.
5. **Spatial Grounding:** The red dot (correct guess) is always the highest or tied-for-highest point in its subplot. Its x-position is explicitly labeled.
### Interpretation
This data strongly demonstrates a **timing side-channel attack** used to recover a secret value (a cookie) one byte at a time. The underlying mechanism likely involves a comparison operation (e.g., checking a user-supplied guess against the secret) that takes measurably longer when a byte is correct. This could be due to an early-exit condition in a loop or a branch misprediction penalty.
* **What the data suggests:** The attacker can reliably distinguish the correct byte from all other possibilities by measuring response times. The clear separation between the red dot and the blue cluster indicates a high signal-to-noise ratio, making the attack efficient and reliable.
* **How elements relate:** Each subplot represents one step in an iterative attack. The output of one step (the correct byte) becomes the prefix for the guesses in the next step. The consistent y-axis scale allows for direct comparison of the timing side-channel's magnitude across different byte positions.
* **Notable outliers/anomalies:** The elevated timing for `cookie=SE8` in Byte 2 is the most significant anomaly. It suggests that the comparison logic is not perfectly constant-time; some incorrect values may take longer to reject than others, potentially leaking additional information or complicating the attack's noise floor.
* **Broader implication:** The image provides empirical evidence of a critical security vulnerability in the system being tested. It shows that secret data can be extracted through passive timing measurements, without needing to breach other security boundaries. The recovered prefix "SECR" hints that the full secret may be the word "SECRET" or a similar string.