## Diagram: Closed-Source Tests Access Model
### Overview
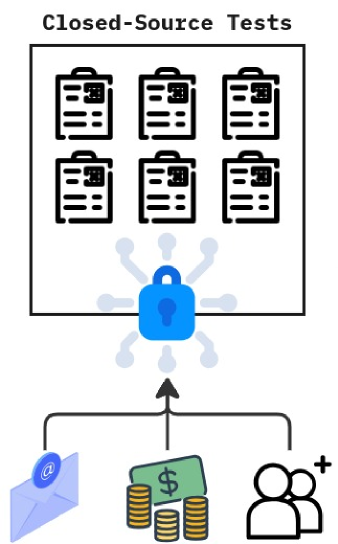
This diagram illustrates a conceptual model for "Closed-Source Tests," depicting how access or interaction with these tests is governed. It shows a collection of tests protected by a central lock, with three distinct inputs or requirements feeding into this protective mechanism.
### Components/Axes
The diagram is structured into three main conceptual layers:
* **Top Layer (Header/System):**
* **Title:** "Closed-Source Tests" - Positioned at the very top, centered.
* **System Boundary:** A large black rectangular box, centrally located below the title, representing the container for the tests.
* **Test Icons:** Inside the rectangular box, there are six identical clipboard/document icons arranged in a 2x3 grid (two rows, three columns). Each icon is black outline with internal lines representing text and a small grid-like symbol in the top-right corner, signifying individual tests or documents.
* **Middle Layer (Access Mechanism):**
* **Padlock Icon:** A prominent blue padlock icon is centrally positioned below the "Closed-Source Tests" box. It has a keyhole symbol in its center.
* **Radiating Connections:** Eight light-blue/grey keyhole-shaped nodes radiate outwards from the padlock icon, suggesting multiple potential connections or facets of its function.
* **Upward Arrow (Padlock to Tests):** A solid black arrow points directly upwards from the top of the padlock icon to the bottom edge of the "Closed-Source Tests" rectangular box.
* **Bottom Layer (Inputs/Requirements):**
* **Central Upward Arrow (Inputs to Padlock):** A solid black arrow points directly upwards from a central point below the padlock, connecting to the bottom of the padlock icon.
* **Branching Lines:** Two horizontal lines branch out from the base of this central arrow, extending left and right. Vertical lines drop down from these horizontal branches to connect to individual input icons.
* **Left Input Icon:** A light blue envelope with a dark blue "@" symbol on its front. This icon is positioned below the left branching line.
* **Middle Input Icon:** A stack of three gold coins with a green bill featuring a "$" symbol on top. This icon is positioned below the central upward arrow.
* **Right Input Icon:** Two outline figures of people (one slightly behind the other), with a small "+" symbol next to the head of the rightmost figure. This icon is positioned below the right branching line.
### Detailed Analysis
The diagram visually represents a flow or dependency. The "Closed-Source Tests" are the ultimate subject, contained within a defined boundary. Access to or interaction with these tests is mediated by the central blue padlock. The padlock itself is fed by three distinct sources or requirements originating from the bottom layer.
1. **Closed-Source Tests (Top Box):** This section implies a collection or suite of tests. The term "Closed-Source" in the title explicitly states that the internal workings or details of these tests are not publicly available or transparent.
2. **Padlock (Middle):** The padlock acts as a gatekeeper or a security mechanism. The upward arrow from the padlock to the "Closed-Source Tests" box suggests that the padlock *controls* access to these tests. The radiating keyhole shapes around the padlock could imply various security protocols, access points, or dependencies associated with this protection.
3. **Inputs (Bottom):**
* **Email/Communication:** The envelope icon likely represents communication, registration via email, notifications, or perhaps a subscription model.
* **Money/Payment:** The money icon clearly signifies financial transactions, payment, or a monetary contribution required for access.
* **Users/Community:** The user group icon suggests user involvement, community membership, collaboration, or perhaps a requirement for a certain number of users or a specific user group to gain access.
The arrows indicate a flow: the three inputs (email, money, users) contribute to or enable the padlock mechanism, which in turn grants or controls access to the "Closed-Source Tests."
### Key Observations
* The "Closed-Source Tests" are explicitly contained and protected.
* The padlock is the central point of control for accessing these tests.
* Three distinct categories of inputs (communication, financial, social/user-based) are identified as prerequisites or enablers for interacting with the padlock.
* The diagram uses simple, universally recognizable icons to convey complex concepts.
### Interpretation
This diagram suggests a model for how "Closed-Source Tests" are managed and accessed. The "closed-source" nature implies that the tests themselves are proprietary, confidential, or otherwise restricted from public view or modification. The padlock reinforces this idea of security and controlled access.
The three inputs at the bottom represent the conditions or methods by which one might gain access to or interact with these protected tests:
1. **Email/Communication:** This could mean that users need to register, subscribe to a mailing list, or receive specific invitations via email to participate in or access the tests. It points to a communication channel as a gateway.
2. **Money/Payment:** This strongly indicates that the "Closed-Source Tests" are part of a paid service, product, or require a financial contribution (e.g., a license fee, subscription, or purchase) to gain access.
3. **Users/Community:** This could imply that access is granted to specific user groups, a defined community, or perhaps requires a certain level of user engagement or membership. The "+" symbol might suggest adding new users or expanding the community of testers.
In essence, the diagram illustrates that "Closed-Source Tests" are not freely available. Instead, they are behind a "paywall," a "registration wall," or a "community wall," or a combination thereof. The padlock acts as the enforcement mechanism for these access requirements. The radiating points from the padlock could further suggest that there are multiple layers of security or different types of access permissions that can be granted based on these inputs. This model is typical for proprietary software testing, beta programs, or exclusive research initiatives where resources (tests) are valuable and access needs to be controlled and monetized or managed.