TECHNICAL ASSET FINGERPRINT
adfc2587861206350612e194
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
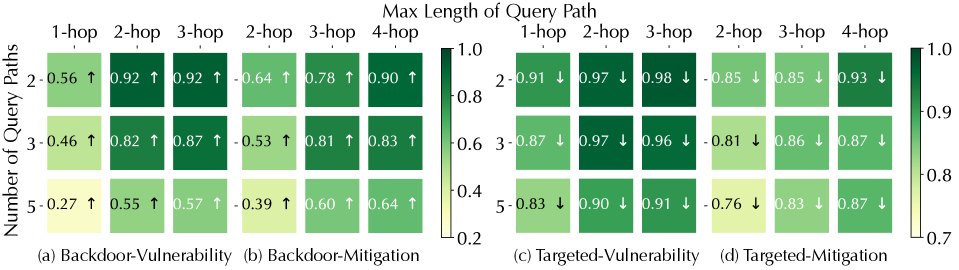
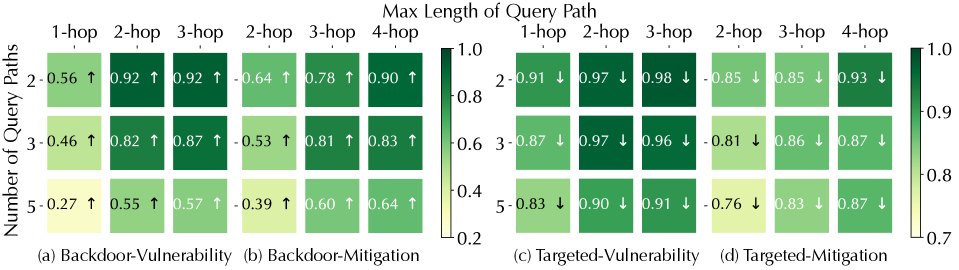
## [Composite Heatmap Figure]: Vulnerability and Mitigation Analysis Across Query Path Parameters
### Overview
The image displays a composite figure containing four distinct heatmaps, labeled (a) through (d), arranged horizontally. Each heatmap visualizes a metric (likely a score or probability) related to either "Vulnerability" or "Mitigation" for two attack types: "Backdoor" and "Targeted." The metrics are plotted against two variables: the "Number of Query Paths" (y-axis) and the "Max Length of Query Path" (x-axis). A shared color bar on the far right provides the scale for interpreting the cell colors.
### Components/Axes
* **Main Title (Top Center):** "Max Length of Query Path"
* **Y-Axis Label (Left Side, Rotated):** "Number of Query Paths"
* **Color Bar/Legend (Far Right):** A vertical gradient bar ranging from light yellow (value 0.2) to dark green (value 1.0). Ticks are marked at 0.2, 0.4, 0.6, 0.8, and 1.0.
* **Subplot Titles:**
* (a) Backdoor-Vulnerability
* (b) Backdoor-Mitigation
* (c) Targeted-Vulnerability
* (d) Targeted-Mitigation
* **X-Axis Categories (Per Subplot):** Columns are labeled with hop counts. The specific labels vary slightly:
* (a) & (c): 1-hop, 2-hop, 3-hop
* (b) & (d): 2-hop, 3-hop, 4-hop
* **Y-Axis Categories (Per Subplot):** Rows are labeled with numbers: 2, 3, 5.
### Detailed Analysis
Each cell contains a numerical value (approximate, based on color) and an arrow (↑ or ↓). The arrow likely indicates the direction of change or trend for that specific condition.
**Subplot (a) Backdoor-Vulnerability:**
* **Trend:** Values generally decrease as the "Number of Query Paths" increases (moving down a column). Values generally increase as the "Max Length of Query Path" increases (moving right across a row).
* **Data Points (Row, Column: Value ↑):**
* Row 2: (1-hop: 0.56 ↑), (2-hop: 0.92 ↑), (3-hop: 0.92 ↑)
* Row 3: (1-hop: 0.46 ↑), (2-hop: 0.82 ↑), (3-hop: 0.87 ↑)
* Row 5: (1-hop: 0.27 ↑), (2-hop: 0.55 ↑), (3-hop: 0.57 ↑)
**Subplot (b) Backdoor-Mitigation:**
* **Trend:** Similar to (a), values decrease with more query paths and increase with longer path lengths. The values are generally lower than in (a) for corresponding cells.
* **Data Points (Row, Column: Value ↑):**
* Row 2: (2-hop: 0.64 ↑), (3-hop: 0.78 ↑), (4-hop: 0.90 ↑)
* Row 3: (2-hop: 0.53 ↑), (3-hop: 0.81 ↑), (4-hop: 0.83 ↑)
* Row 5: (2-hop: 0.39 ↑), (3-hop: 0.60 ↑), (4-hop: 0.64 ↑)
**Subplot (c) Targeted-Vulnerability:**
* **Trend:** Values show a slight decrease or remain high as the "Number of Query Paths" increases. Values are consistently high across different "Max Length of Query Path." All arrows point down (↓).
* **Data Points (Row, Column: Value ↓):**
* Row 2: (1-hop: 0.91 ↓), (2-hop: 0.97 ↓), (3-hop: 0.98 ↓)
* Row 3: (1-hop: 0.87 ↓), (2-hop: 0.97 ↓), (3-hop: 0.96 ↓)
* Row 5: (1-hop: 0.83 ↓), (2-hop: 0.90 ↓), (3-hop: 0.91 ↓)
**Subplot (d) Targeted-Mitigation:**
* **Trend:** Values are generally high but show a more noticeable decrease as the "Number of Query Paths" increases, especially for shorter path lengths. All arrows point down (↓).
* **Data Points (Row, Column: Value ↓):**
* Row 2: (2-hop: 0.85 ↓), (3-hop: 0.85 ↓), (4-hop: 0.93 ↓)
* Row 3: (2-hop: 0.81 ↓), (3-hop: 0.86 ↓), (4-hop: 0.87 ↓)
* Row 5: (2-hop: 0.76 ↓), (3-hop: 0.83 ↓), (4-hop: 0.87 ↓)
### Key Observations
1. **Directional Dichotomy:** The arrows show a clear split. All cells in the "Backdoor" scenarios (a, b) have upward arrows (↑), while all cells in the "Targeted" scenarios (c, d) have downward arrows (↓). This suggests fundamentally different behaviors or measurement directions between the two attack types.
2. **Vulnerability vs. Mitigation Levels:** For "Backdoor," the vulnerability scores (a) are generally higher than the mitigation scores (b) for comparable conditions. For "Targeted," the vulnerability scores (c) are very high (mostly >0.85), and the mitigation scores (d) are also high but slightly lower in some cases (e.g., 5-query paths, 2-hop).
3. **Impact of Query Path Number:** Increasing the "Number of Query Paths" (y-axis) consistently leads to lower metric values across all four subplots.
4. **Impact of Query Path Length:** Increasing the "Max Length of Query Path" (x-axis) consistently leads to higher metric values across all four subplots.
5. **Outlier/Lowest Point:** The lowest value in the entire figure is 0.27 in subplot (a) for 5 query paths of 1-hop length, indicating very low backdoor vulnerability under that specific, constrained condition.
### Interpretation
This figure likely comes from a study on the security of machine learning models, specifically analyzing how the complexity of an attacker's query strategy (defined by the number and length of query paths) affects the model's vulnerability to backdoor or targeted attacks, and the effectiveness of corresponding mitigation techniques.
* **What the data suggests:** The data demonstrates a clear trade-off. Simpler attack strategies (fewer, shorter query paths) are associated with lower vulnerability scores but also lower mitigation scores in backdoor scenarios. More complex strategies (more, longer paths) increase vulnerability but also seem to allow for higher mitigation scores, particularly in the backdoor case. For targeted attacks, vulnerability is consistently high regardless of strategy, but mitigation effectiveness slightly decreases with more complex (higher number of) query paths.
* **Relationship between elements:** The "Vulnerability" plots (a, c) likely measure the success rate or risk of an attack. The "Mitigation" plots (b, d) likely measure the success rate of a defense mechanism in neutralizing the attack. The opposing arrow directions (↑ for Backdoor, ↓ for Targeted) are the most critical finding, implying that the metrics for these two attack paradigms are inversely related or measured on inverted scales. For example, in Backdoor attacks, a higher value might mean "easier to attack/defend," while in Targeted attacks, a higher value might mean "harder to attack/defend."
* **Underlying Patterns:** The consistent trends with respect to query path number and length suggest these are fundamental parameters controlling the attack/defense dynamics. The high values in the Targeted plots indicate that targeted attacks are a more persistent threat that is harder to fully mitigate, especially as the attacker's query budget (number of paths) increases. The figure provides a quantitative map for understanding how an attacker might tune their strategy and how effective defenses are likely to be under different conditions.
DECODING INTELLIGENCE...