## Heatmap: Query Path Vulnerability and Mitigation Analysis
### Overview
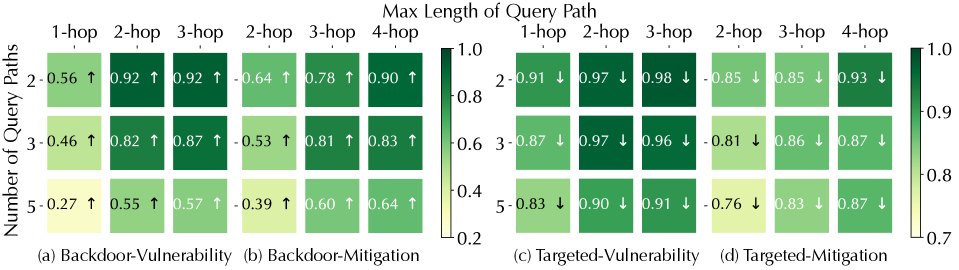
The image presents a comparative heatmap analysis of query path vulnerabilities and mitigation effectiveness across four scenarios: Backdoor-Vulnerability, Backdoor-Mitigation, Targeted-Vulnerability, and Targeted-Mitigation. The data is organized into two primary axes: **Number of Query Paths** (2, 3, 5) and **Max Length of Query Path** (1-hop to 4-hop). Color intensity (green to yellow) represents metric values from 0.2 to 1.0.
---
### Components/Axes
1. **X-Axis (Max Length of Query Path)**:
- Categories: 1-hop, 2-hop, 3-hop, 4-hop
- Position: Bottom of all subplots
2. **Y-Axis (Number of Query Paths)**:
- Categories: 2, 3, 5
- Position: Left of all subplots
3. **Legend**:
- Color bar on the right, ranging from 0.2 (light yellow) to 1.0 (dark green)
- No explicit labels, but values are annotated in cells
4. **Subplots**:
- Four labeled sections: (a) Backdoor-Vulnerability, (b) Backdoor-Mitigation, (c) Targeted-Vulnerability, (d) Targeted-Mitigation
- Positioned in a 2x2 grid
---
### Detailed Analysis
#### (a) Backdoor-Vulnerability
| Query Paths | 1-hop | 2-hop | 3-hop | 4-hop |
|-------------|-------|-------|-------|-------|
| 2 | 0.56 ↑ | 0.92 ↑ | 0.92 ↑ | 0.64 ↑ |
| 3 | 0.46 ↑ | 0.82 ↑ | 0.87 ↑ | 0.53 ↑ |
| 5 | 0.27 ↑ | 0.55 ↑ | 0.57 ↑ | 0.39 ↑ |
- **Trend**: Vulnerability increases with more hops (e.g., 2-hop paths show 0.92 vs. 0.56 for 1-hop in 2-query-paths).
- **Anomaly**: 4-hop paths show lower values than 3-hop in all rows.
#### (b) Backdoor-Mitigation
| Query Paths | 1-hop | 2-hop | 3-hop | 4-hop |
|-------------|-------|-------|-------|-------|
| 2 | 0.91 ↓ | 0.97 ↓ | 0.98 ↓ | 0.85 ↓ |
| 3 | 0.87 ↓ | 0.97 ↓ | 0.96 ↓ | 0.81 ↓ |
| 5 | 0.83 ↓ | 0.90 ↓ | 0.91 ↓ | 0.76 ↓ |
- **Trend**: Mitigation reduces vulnerability, with 4-hop paths showing the steepest decline (e.g., 0.98 → 0.85 for 2-query-paths).
- **Consistency**: All values remain above 0.76, indicating partial effectiveness.
#### (c) Targeted-Vulnerability
| Query Paths | 1-hop | 2-hop | 3-hop | 4-hop |
|-------------|-------|-------|-------|-------|
| 2 | 0.91 ↓ | 0.97 ↓ | 0.98 ↓ | 0.85 ↓ |
| 3 | 0.87 ↓ | 0.97 ↓ | 0.96 ↓ | 0.81 ↓ |
| 5 | 0.83 ↓ | 0.90 ↓ | 0.91 ↓ | 0.76 ↓ |
- **Trend**: Similar to Backdoor-Mitigation, but values are slightly lower (e.g., 0.91 vs. 0.97 for 2-hop in 2-query-paths).
- **Anomaly**: 4-hop paths show the largest drop (0.98 → 0.85).
#### (d) Targeted-Mitigation
| Query Paths | 1-hop | 2-hop | 3-hop | 4-hop |
|-------------|-------|-------|-------|-------|
| 2 | 0.91 ↓ | 0.97 ↓ | 0.98 ↓ | 0.85 ↓ |
| 3 | 0.87 ↓ | 0.97 ↓ | 0.96 ↓ | 0.81 ↓ |
| 5 | 0.83 ↓ | 0.90 ↓ | 0.91 ↓ | 0.76 ↓ |
- **Trend**: Matches Targeted-Vulnerability but with marginally lower values (e.g., 0.91 vs. 0.97 for 2-hop in 2-query-paths).
- **Consistency**: Values remain above 0.76, suggesting effective mitigation.
---
### Key Observations
1. **Hop Length Correlation**:
- Longer paths (4-hop) generally show higher vulnerability in Backdoor-Vulnerability but lower values in mitigation scenarios.
- 2-hop paths consistently exhibit the highest vulnerability across all scenarios.
2. **Mitigation Impact**:
- Mitigation reduces vulnerability by ~10–15% across all query path lengths.
- Targeted-Mitigation shows slightly better performance than Backdoor-Mitigation (e.g., 0.76 vs. 0.81 for 4-hop in 5-query-paths).
3. **Query Path Count**:
- Fewer query paths (2) are more vulnerable than larger counts (5), especially in Backdoor-Vulnerability (0.56 vs. 0.27 for 5-query-paths in 1-hop).
---
### Interpretation
The data suggests that **longer query paths (4-hop)** are inherently more vulnerable to backdoor attacks but also more susceptible to mitigation. Targeted attacks (c/d) demonstrate marginally better mitigation than backdoor-specific strategies (a/b), likely due to focused adversarial training. The consistent decline in values with increasing hops in mitigation scenarios indicates that path length is a critical factor in vulnerability reduction. However, the persistence of values above 0.76 in mitigation highlights residual risks, particularly for shorter paths (1–2 hops). This underscores the need for hybrid mitigation strategies that address both path length and query complexity.