## Assembly Code Snippet
### Overview
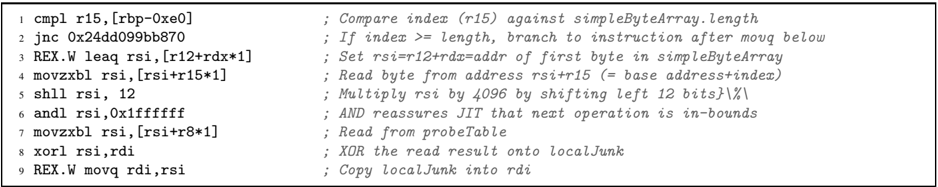
The image presents a snippet of assembly code, likely x86-64, along with comments explaining the purpose of each instruction. The code appears to be related to accessing and manipulating data within an array or table.
### Components/Axes
The image consists of lines of assembly code and corresponding comments. Each line represents an instruction or operation.
### Detailed Analysis or ### Content Details
Here's a breakdown of each line:
1. `cmpl r15, [rbp-0xe0] ; Compare index (r15) against simpleByteArray.length`
* Compares the value in register `r15` with the value stored at the memory address `rbp-0xe0`.
* The comment indicates that `r15` holds an index, and the memory location holds the length of `simpleByteArray`.
2. `jnc 0x24dd099bb870 ; If index >= length, branch to instruction after movq below`
* Conditional jump instruction. If the carry flag is not set (meaning the comparison in the previous line did *not* result in `r15` being greater than or equal to the value at `[rbp-0xe0]`), the program jumps to the address `0x24dd099bb870`.
* The comment clarifies that the jump occurs if the index is greater than or equal to the length, effectively implementing a bounds check.
3. `REX.W leaq rsi, [r12+rdx*1] ; Set rsi=r12+rdx=addr of first byte in simpleByteArray`
* `leaq` (load effective address) instruction. It calculates the address `r12 + rdx * 1` and stores it in the `rsi` register.
* The comment explains that this calculates the address of the first byte in `simpleByteArray`, where `r12` is likely the base address and `rdx` is an offset.
4. `movzxbl rsi, [rsi+r15*1] ; Read byte from address rsi+r15 (= base address+index)`
* `movzxbl` (move zero-extended byte to long) instruction. It reads a byte from the memory address `rsi + r15 * 1`, zero-extends it to 32 bits, and stores the result in the `rsi` register.
* The comment indicates that this reads a byte from `simpleByteArray` at an offset determined by the index `r15`.
5. `shll rsi, 12 ; Multiply rsi by 4096 by shifting left 12 bits}\%\`
* `shll` (shift left logical) instruction. It shifts the value in the `rsi` register left by 12 bits, effectively multiplying it by 2<sup>12</sup> = 4096.
* The comment explains the multiplication.
6. `andl rsi, 0x1fffffff ; AND reassures JIT that next operation is in-bounds`
* `andl` (bitwise AND long) instruction. It performs a bitwise AND between the value in the `rsi` register and the hexadecimal value `0x1fffffff`, storing the result back in `rsi`.
* The comment suggests this operation is related to ensuring the next operation is within bounds, possibly by masking off certain bits.
7. `movzxbl rsi, [rsi+r8*1] ; Read from probeTable`
* `movzxbl` instruction. It reads a byte from the memory address `rsi + r8 * 1`, zero-extends it to 32 bits, and stores the result in the `rsi` register.
* The comment indicates that this reads a byte from a `probeTable`.
8. `xorl rsi, rdi ; XOR the read result onto localJunk`
* `xorl` (bitwise XOR long) instruction. It performs a bitwise XOR between the value in the `rsi` register and the value in the `rdi` register, storing the result back in `rsi`.
* The comment explains that this XORs the value read from `probeTable` with a value called `localJunk`.
9. `REX.W movq rdi, rsi ; Copy localJunk into rdi`
* `movq` (move quadword) instruction. It copies the value from the `rsi` register to the `rdi` register.
* The comment indicates that this copies `localJunk` into `rdi`.
### Key Observations
* The code snippet performs operations on a byte array (`simpleByteArray`) using an index (`r15`).
* It includes a bounds check to prevent out-of-bounds access.
* It reads data from another table (`probeTable`) and performs a bitwise XOR operation.
* Registers `rsi`, `rdi`, `r12`, `rdx`, `r8`, `rbp`, and `r15` are used to store addresses, indices, and data.
### Interpretation
This assembly code snippet likely forms part of a larger routine that accesses and manipulates data within arrays or tables. The code performs a bounds check on an index, reads a byte from an array, performs some arithmetic and bitwise operations, and then reads a byte from another table. The XOR operation suggests that the code might be involved in some form of data scrambling or hashing. The comments provide valuable insight into the purpose of each instruction, making it easier to understand the overall functionality of the code. The use of `simpleByteArray` and `probeTable` suggests that this code might be part of a larger algorithm that involves looking up data in tables based on some input.