\n
## Code Snippet: Assembly Instructions
### Overview
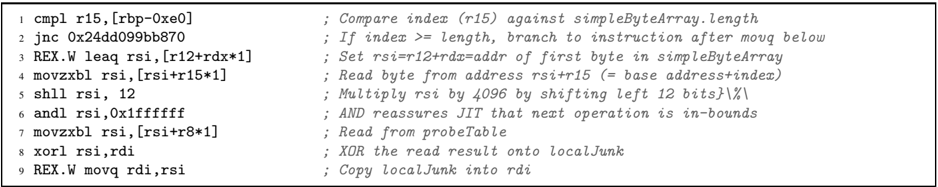
The image presents a snippet of assembly code, likely generated from a higher-level language. It consists of a numbered sequence of instructions, each with its opcode and a corresponding comment explaining its function. The code appears to be related to array access and manipulation, potentially within a loop.
### Components/Axes
The snippet is structured as a list of instructions. Each line contains:
1. A line number (1-9)
2. The assembly instruction itself (e.g., `cmpl r15, [rbp-0xe0]`)
3. A semicolon (`;`) separating the instruction from its comment.
4. A comment explaining the instruction's purpose.
### Detailed Analysis or Content Details
Here's a transcription of each line:
1. `cmpl r15, [rbp-0xe0]` ; Compare index (r15) against simpleByteArray.length
2. `jnc 0x24dd099b870` ; If index >= length, branch to instruction after movq below
3. `REX.W leaq rsi, [r12+rdx*1]` ; Set rsi=r12+rdx=addr of first byte in simpleByteArray
4. `movzxbl rsi, [rsi+r15*1]` ; Read byte from address rsi+r15 (= base address+index)
5. `shll rsi, 12` ; Multiply rsi by 4096 by shifting left 12 bits
6. `andl rsi, 0x1ffffff` ; AND reassures JIT that next operation is in-bounds
7. `movzxbl rsi, [rsi+r8*1]` ; Read from probeTable
8. `xorl rsi, rdi` ; XOR the read result onto localJunk
9. `REX.W movq rdi, rsi` ; Copy localJunk into rdi
### Key Observations
* The code performs a bounds check (`cmpl` and `jnc`) to ensure the index `r15` is within the bounds of `simpleByteArray`.
* It calculates the memory address of an element within `simpleByteArray` using `leaq` and `movzxbl`.
* The code involves a `probeTable` and XOR operation, suggesting a potential hashing or lookup mechanism.
* The use of `REX.W` indicates 64-bit operations.
* The shifting operation (`shll rsi, 12`) multiplies the index by 4096, which could be related to memory alignment or accessing elements in a larger data structure.
### Interpretation
This code snippet likely represents a part of a function that accesses elements of an array (`simpleByteArray`) using an index (`r15`). The bounds check ensures that the access is valid. The `probeTable` and XOR operation suggest a more complex data access pattern, potentially involving a hash table or a lookup table to optimize access or perform some transformation on the data. The multiplication by 4096 and subsequent AND operation might be related to memory layout or caching optimizations. The code appears to be optimized for performance, as indicated by the use of `REX.W` and the bitwise operations. The overall purpose is to read a byte from `simpleByteArray` and process it using the `probeTable` and XOR operation, storing the result in `rdi`. The branching instruction suggests that the code handles cases where the index is out of bounds.